Microsoft is warning of an increase in adversary-in-the-center (AiTM) phishing strategies, which are currently being propagated as element of the phishing-as-a-service (PhaaS) cybercrime product.
In addition to an uptick in AiTM-capable PhaaS platforms, the tech huge noted that current phishing companies like PerSwaysion are incorporating AiTM abilities.
“This enhancement in the PhaaS ecosystem enables attackers to carry out high-volume phishing strategies that endeavor to circumvent MFA protections at scale,” the Microsoft Danger Intelligence crew reported in a series of posts on X (previously Twitter).

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

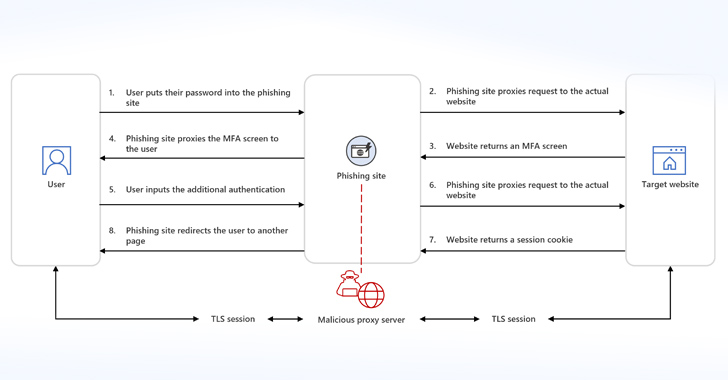
Phishing kits with AiTM capabilities get the job done in two methods, a person of which worries the use of reverse proxy servers (i.e., the phishing page) to relay targeted traffic to and from the customer and legit website and stealthily seize person qualifications, two-factor authentication codes, and session cookies.
A second method consists of synchronous relay servers.
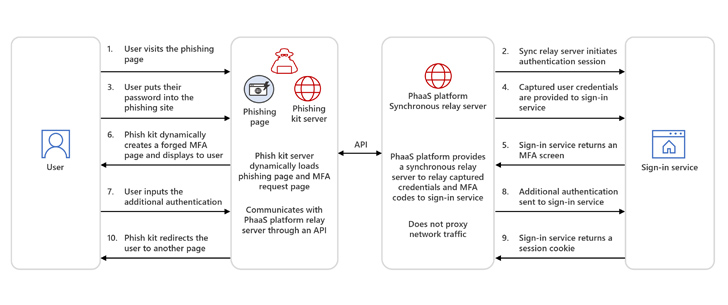
“In AiTM through synchronous relay servers the concentrate on is offered with a copy or mimic of a indicator-in page, like conventional phishing attacks,” Microsoft explained. “Storm-1295, the actor group driving the Greatness PhaaS system, features synchronous relay providers to other attackers.”
Greatness was to start with documented by Cisco Talos in Could 2023 as a assistance that allows cybercriminals goal company end users of the Microsoft 365 cloud service applying convincing decoy and login web pages. It can be reported to have been energetic considering the fact that at least mid-2022.

The final goal of these attacks is to siphon session cookies, enabling menace actors to obtain privileged systems without the need of reauthentication.
“Circumventing MFA is the goal that enthusiastic attackers to develop AiTM session cookie theft techniques,” the tech giant noted. “Unlike standard phishing attacks, incident reaction procedures for AiTM call for revocation of stolen session cookies.”
Located this posting attention-grabbing? Adhere to us on Twitter and LinkedIn to read a lot more distinctive written content we post.
Some elements of this posting are sourced from:
thehackernews.com

 Experts Uncover How Cybercriminals Could Exploit Microsoft Entra ID for Elevated Privilege
Experts Uncover How Cybercriminals Could Exploit Microsoft Entra ID for Elevated Privilege