A .NET-dependent evasive crypter named DarkTortilla has been utilised by risk actors to distribute a broad array of commodity malware as properly as specific payloads like Cobalt Strike and Metasploit, probably considering the fact that 2015.
“It can also produce ‘add-on packages’ this sort of as added malicious payloads, benign decoy files, and executables,” cybersecurity firm Secureworks stated in a Wednesday report. “It functions strong anti-investigation and anti-tamper controls that can make detection, evaluation, and eradication hard.”
Malware shipped by the crypter involves info steakers and remote accessibility trojans (RATs) these kinds of as Agent Tesla, AsyncRat, NanoCore, and RedLine Stealer. “DarkTortilla has flexibility that very similar malware does not,” the scientists famous.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

Crypters are software program equipment that use a mix of encryption, obfuscation, and code manipulation of malware so as to bypass detection by security solutions.
The shipping of DarkTortilla takes place by using destructive spam emails which comprise archives with an executable for an preliminary loader that is employed to decode and start a core processor module possibly embedded inside of alone or fetched from text storage web pages this sort of as Pastebin.
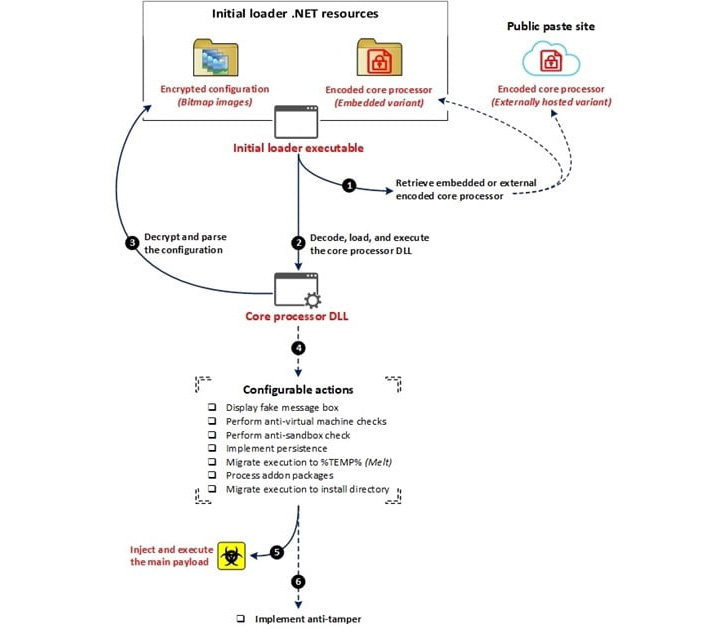
The core processor is then responsible for developing persistence and injecting the major RAT payload into memory with no leaving a path on the file program through an elaborate configuration file that also makes it possible for it to fall increase-on packages, together with keyloggers, clipboard stealers, and cryptocurrency miners.
DarkTortilla is more noteworthy for its use of anti-tamper controls that make certain both the processes utilized to execute the elements in memory are right away rerun upon termination.
Specifically, the persistence of the first loader is achieved by indicates of a 2nd executable referred to as a WatchDog that’s created to hold tabs on the selected process and rerun it need to it be killed.

This procedure is reminiscent of a identical system adopted by a danger actor known as Moses Employees, which, before this calendar year, was observed relying on a watchdog-primarily based approach to prevent any interruption to its payloads. Also utilized are two other controls to guarantee the ongoing execution of the dropped WatchDog executable alone and the persistence for the first loader.
Secureworks said it recognized an average of 93 exclusive DarkTortilla samples getting uploaded to the VirusTotal malware databases for every week over a 17-month period from January 2021 to Could 2022.
“DarkTortilla is capable of evading detection, is really configurable, and delivers a vast assortment of well-known and helpful malware,” the scientists concluded. “Its abilities and prevalence make it a formidable risk.”
Located this article appealing? Abide by THN on Facebook, Twitter and LinkedIn to read a lot more exceptional information we submit.
Some sections of this report are sourced from:
thehackernews.com


 Hackers Deploy Bumblebee Loader to Breach Target Networks
Hackers Deploy Bumblebee Loader to Breach Target Networks