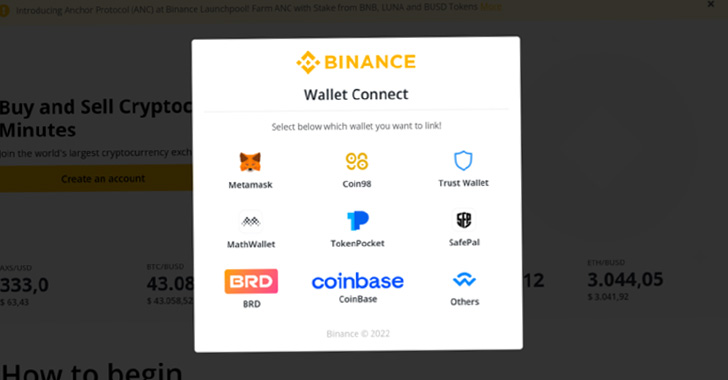
Cybercriminals are impersonating popular crypto platforms this kind of as Binance, Celo, and Have faith in Wallet with spoofed e-mails and pretend login internet pages in an attempt to steal login particulars and deceptively transfer virtual funds.
“As cryptocurrency and non-fungible tokens (NFTs) develop into additional mainstream, and capture headlines for their volatility, there is a bigger chance of more people today falling sufferer to fraud making an attempt to exploit people today for digital currencies,” Proofpoint reported in a new report.
“The rise and proliferation of cryptocurrency has also presented attackers with a new system of financial extraction.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
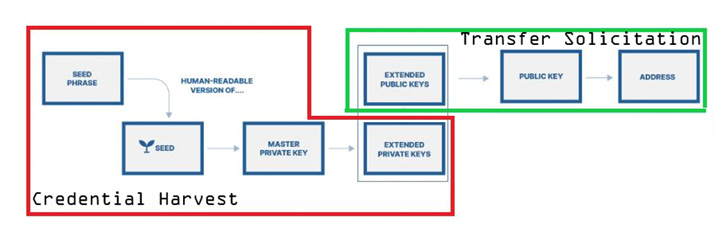
The concentrating on of sensitive cryptocurrency data by risk actors was not too long ago echoed by the Microsoft 365 Defender Investigation Team, which warned about the emerging danger of cryware wherein private keys, seed phrases, and wallet addresses are plundered with the purpose of siphoning digital currencies by usually means of fraudulent transfers.

The swift acceptance of Web3 in modern yrs has brought on a shift in the phishing landscape, paving the way for a variety of social engineering and exploitation mechanisms that are aimed at stealing cryptocurrencies in distinctive approaches ranging from credential harvesting to the use of commodity stealer malware.
This contains spam e-mails that have hyperlinks to rogue URLs that down load malware and redirect customers to a credential harvesting landing site or even phony lookalike versions of NFT investing platforms like OpenSea. Other strategies prompt possible victims to enter their seed phrases.
In a phishing attack detected by the company security business in February 2022, a Have confidence in Wallet-themed entice was noticed nudging email recipients, especially university college students, to verify their wallets by entering the recovery phrases.
A crucial enabler of these customized strategies is the relative relieve with which counterfeit landing pages can be constructed working with phishing kits, letting considerably less proficient threat actors to distribute and regulate campaigns at a substantial scale.
Additional incentivizing the cybercriminal plan are phishing-as-a-service (PHaaS) operators like BulletProofLink that offer phishing templates, spamming companies, bulletproof hosting products and services, and credential assortment providers, amid others.
The kits, which are continuously up-to-date and expanded, are created to mimic different brands such as blockchain[.]com as well as other NFT and other cryptocurrency wallet assistance vendors.
Also popular are enterprise email compromise (BEC) tries to aid the fraudulent transfer of digital coins as a result of messages that solicit cryptocurrency less than the guise of seller payments and donation requests to assist the Ukraine war exertion.

The conclusions arrive as losses from crypto-connected crime jumped 79% year-over-year in 2021, with the U.S. Federal Trade Commission (FTC) noting that far more than 46,000 people have claimed dropping about $1 billion in electronic currencies to scams.
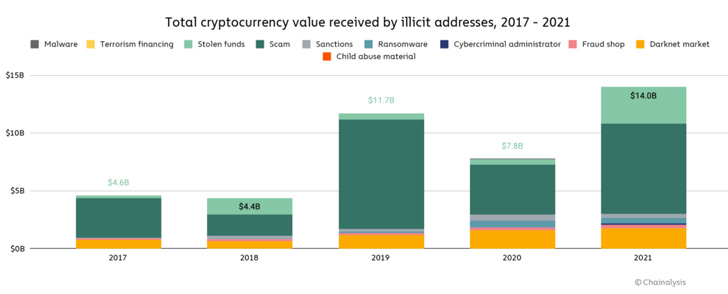
What is more, Blockchain analytics company Chainalysis observed that cryptocurrency-based mostly criminal offense strike a new all-time significant in 2021, even as illicit addresses gained $14 billion above the course of the year, up from $7.8 billion in 2020.
“Cybercriminal threats to cryptocurrency are not new, however as the normal community experiences developing adoption of cryptocurrency, persons might be far more possible to engage with social engineering lures utilizing these themes,” Sherrod DeGrippo, vice president of threat investigation and detection at Proofpoint, claimed.
“Crypto went mainstream with Superbowl adverts this year and threat actors have taken take note of the chance for a brief payday. There is no less difficult strategy of financial extraction than the illicit transfer of cryptocurrency.”
Discovered this posting interesting? Follow THN on Facebook, Twitter and LinkedIn to browse more special material we publish.
Some components of this short article are sourced from:
thehackernews.com

 Researchers Disclose Critical Flaws in Industrial Access Control System from Carrier
Researchers Disclose Critical Flaws in Industrial Access Control System from Carrier