As lots of as 34 special susceptible Windows Driver Product (WDM) and Windows Driver Frameworks (WDF) motorists could be exploited by non-privileged threat actors to achieve full management of the devices and execute arbitrary code on the underlying techniques.
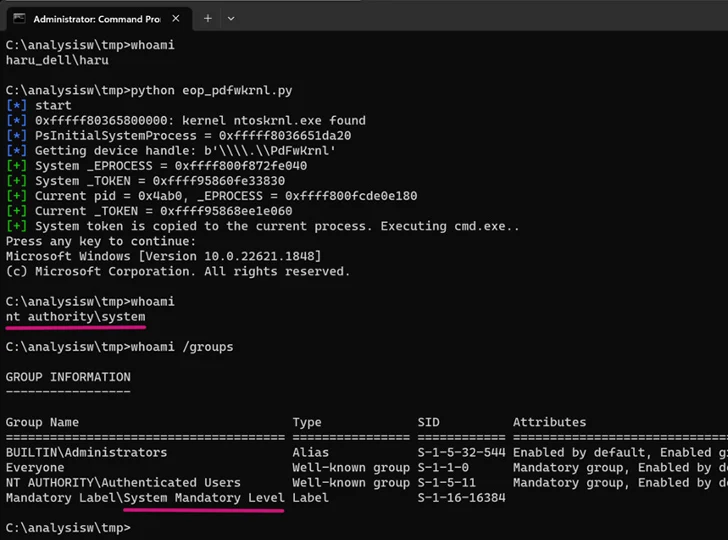
“By exploiting the motorists, an attacker with no privilege may erase/change firmware, and/or elevate [operating system] privileges,” Takahiro Haruyama, a senior risk researcher at VMware Carbon Black, reported.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The study expands on former scientific tests, these kinds of as ScrewedDrivers and POPKORN that used symbolic execution for automating the discovery of susceptible motorists. It particularly focuses on motorists that include firmware accessibility by means of port I/O and memory-mapped I/O.
The names of some of the susceptible drivers consist of AODDriver.sys, ComputerZ.sys, dellbios.sys, GEDevDrv.sys, GtcKmdfBs.sys, IoAccess.sys, kerneld.amd64, ngiodriver.sys, nvoclock.sys, PDFWKRNL.sys (CVE-2023-20598), RadHwMgr.sys, rtif.sys, rtport.sys, stdcdrv64.sys, and TdkLib64.sys (CVE-2023-35841).
Of the 34 drivers, 6 enable kernel memory obtain that can be abused to elevate privilege and defeat security answers. Twelve of the motorists could be exploited to subvert security mechanisms like kernel deal with space format randomization (KASLR).
7 of the motorists, together with Intel’s stdcdrv64.sys, can be utilized to erase firmware in the SPI flash memory, rendering the program unbootable. Intel has given that issued a correct for the problem.
VMware explained it also discovered WDF motorists these kinds of as WDTKernel.sys and H2OFFT64.sys that are not vulnerable in conditions of obtain management, but can be trivially weaponized by privileged threat actors to pull off what’s termed a Convey Your Very own Susceptible Driver (BYOVD) attack.

The technique has been employed by a variety of adversaries, such as the North Korea-connected Lazarus Group, as a way to acquire elevated privileges and disable security program working on compromised endpoints so as to evade detection.
“The recent scope of the APIs/guidance specific by the [IDAPython script for automating static code analysis of x64 vulnerable drivers] is slim and only minimal to firmware entry,” Haruyama mentioned.
“Nonetheless, it is simple to prolong the code to include other attack vectors (e.g. terminating arbitrary processes).”
Uncovered this post attention-grabbing? Abide by us on Twitter and LinkedIn to examine extra exclusive content material we publish.
Some parts of this post are sourced from:
thehackernews.com

 FIRST Announces CVSS 4.0 – New Vulnerability Scoring System
FIRST Announces CVSS 4.0 – New Vulnerability Scoring System