The peer-to-peer (P2) worm acknowledged as P2PInfect has witnessed a surge in activity considering the fact that late August 2023, witnessing a 600x soar among September 12 and 19, 2023.
“This raise in P2PInfect website traffic has coincided with a developing amount of variants viewed in the wild, suggesting that the malware’s developers are functioning at an really high development cadence,” Cado Security researcher Matt Muir said in a report released Wednesday.
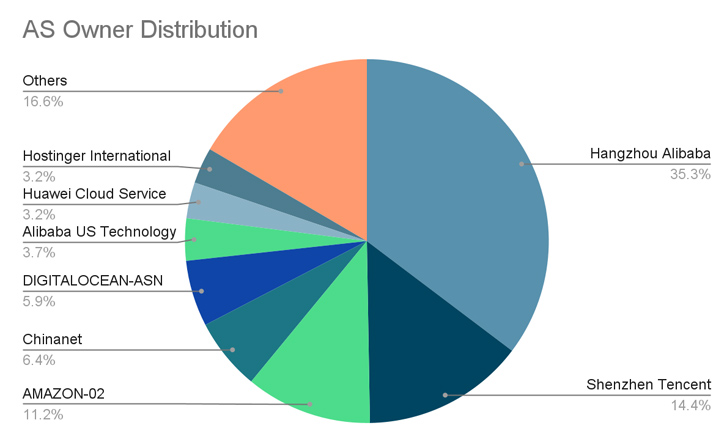
A bulk of the compromises have been noted in China, the U.S., Germany, the U.K., Singapore, Hong Kong, and Japan.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
P2PInfect first came to light in July 2023 for its capacity to breach poorly secured Redis cases. The risk actors behind the campaign have considering the fact that resorted to distinctive ways for initial obtain, such as the abuse of the database’s replication attribute to produce the malware.

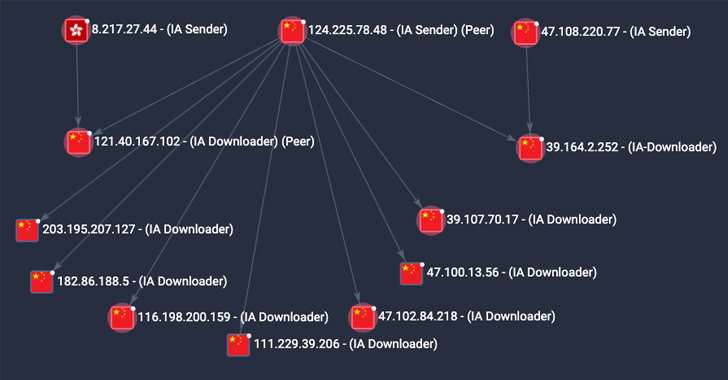
Cado Security claimed it has observed an improve in initial access activities attributable to P2PInfect in which the Redis SLAVEOF command is issued by an actor-controlled node to a goal to help replication.
This is adopted by delivering a destructive Redis module to the concentrate on, which, in flip, runs a command to retrieve and launch the primary payload, soon after which an additional shell command is run to remove the Redis module from the disk as nicely as disable the replication.
1 of the new options of the more recent variants is the addition of a persistence mechanism that leverages a cron position to start the malware just about every 30 minutes.In addition, there now exists a secondary system that retrieves a copy of the malware binary from a peer and executes should really it be deleted or the most important course of action is terminated.
P2PInfect more overwrites current SSH authorized_keys information with an attacker-controlled SSH vital, successfully protecting against current end users from logging in in excess of SSH.
“The main payload also iterates by way of all end users on the process and attempts to change their user passwords to a string prefixed by Pa_ and followed by 7 alphanumeric figures (e.g. Pa_13HKlak),” Muir reported. This stage, nevertheless, necessitates that the malware has root access.
Forthcoming WEBINARLevel-Up SaaS Security: A Detailed Tutorial to ITDR and SSPM
Stay in advance with actionable insights on how ITDR identifies and mitigates threats. Find out about the indispensable function of SSPM in making sure your identification continues to be unbreachable.
Supercharge Your Competencies
Despite the increasing sophistication of the malware, P2PInfect’s actual targets are unclear. Cado Security reported it noticed the malware trying to fetch a crypto miner payload, but there is no evidence of cryptomining to date.
“It really is obvious that P2PInfect’s builders are fully commited to keeping and iterating on the operation of their malicious payloads, though at the same time scaling the botnet across continents and cloud suppliers at a fast level,” Muir stated.
“It is expected that those people driving the botnet are either ready to employ added performance in the miner payload, or are intending to promote accessibility to the botnet to other persons or groups.”
Found this article interesting? Stick to us on Twitter and LinkedIn to read through additional unique content we article.
Some elements of this write-up are sourced from:
thehackernews.com

 The Rise of the Malicious App
The Rise of the Malicious App