The risk actors behind a massive-scale adversary-in-the-middle (AiTM) phishing campaign concentrating on business end users of Microsoft email providers have also set their sights on Google Workspace buyers.
“This marketing campaign exclusively focused main executives and other senior members of various companies which use [Google Workspace],” Zscaler researchers Sudeep Singh and Jagadeeswar Ramanukolanu detailed in a report posted this thirty day period.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
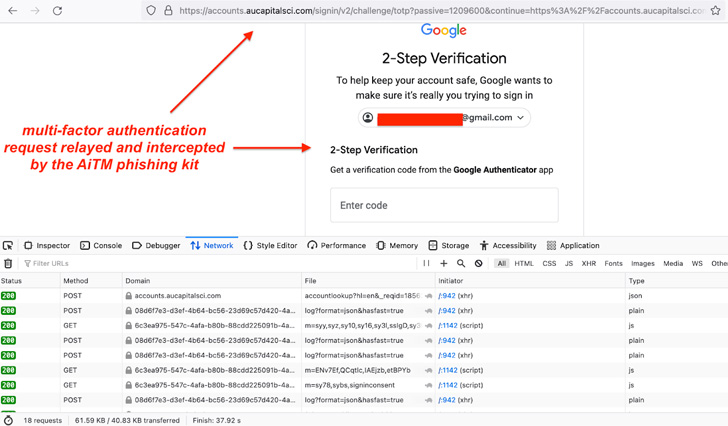
The AitM phishing attacks are claimed to have commenced in mid-July 2022, adhering to a equivalent modus operandi as that of a social engineering campaign developed to siphon users’ Microsoft qualifications and even bypass multi-factor authentication.
The small-volume Gmail AiTM phishing campaign also involves using the compromised email messages of chief executives to perform further more phishing attacks by the threat actor, with the attacks also utilizing numerous compromised domains as an intermediate URL redirector to take the victims to the landing webpage.
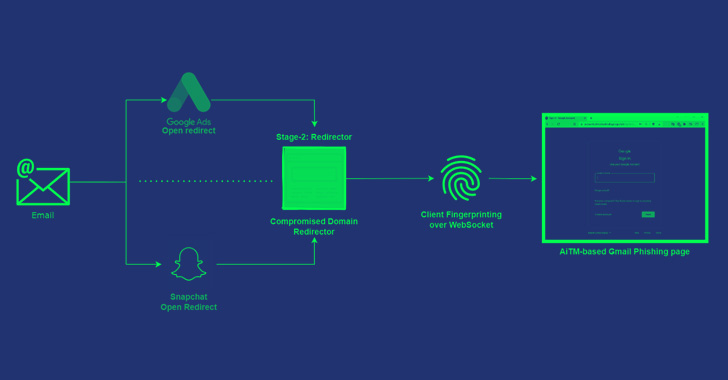
Attack chains involve sending password expiry e-mails to likely targets that consist of an embedded destructive backlink to supposedly “lengthen your access,” tapping which can take the recipient to open up redirect pages of Google Ads and Snapchat to load the phishing web site URL.
Beside open up redirect abuse, a second variant of the attacks depends on contaminated web pages which host a Base64-encoded model of the upcoming-phase redirector and the victim’s email tackle in the URL. This intermediate redirector is a JavaScript code that factors to a Gmail phishing webpage.

In a single occasion highlighted by Zscaler, the redirector webpage employed in the Microsoft AiTM phishing attack on July 11, 2022, was up to date to get the consumer to a Gmail AiTM phishing web site, connecting the two strategies to the identical menace actor.
“There was also an overlap of infrastructure, and we even recognized several situations in which the threat actor switched from Microsoft AiTM phishing to Gmail phishing using the same infrastructure,” the researchers reported.
The findings are an indication that multi-factor authentication safeguards on your own are not able to present protections against state-of-the-art phishing attacks, necessitating that people scrutinize URLs ahead of coming into credentials and refrain from opening attachments or clicking on back links in email messages despatched from untrusted or unidentified resources.
Found this write-up exciting? Stick to THN on Facebook, Twitter and LinkedIn to read through more unique material we submit.
Some components of this post are sourced from:
thehackernews.com

 US Healthcare Sector Breaches 342m+ Records Since 2009
US Healthcare Sector Breaches 342m+ Records Since 2009