A new, huge-scale phishing marketing campaign has been noticed making use of adversary-in-the-center (AitM) tactics to get all around security protections and compromise enterprise email accounts.
“It works by using an adversary-in-the-middle (AitM) attack approach able of bypassing multi-factor authentication,” Zscaler scientists Sudeep Singh and Jagadeeswar Ramanukolanu mentioned in a Tuesday report. “The campaign is precisely built to achieve conclusion users in enterprises that use Microsoft’s email providers.”
Popular targets incorporate fintech, lending, insurance, electrical power, producing, and federal credit union verticals located in the U.S., U.K., New Zealand, and Australia.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

This is not the first time these types of a phishing attack has occur to gentle. Previous month, Microsoft disclosed that over 10,000 corporations had been focused given that September 2021 by usually means of AitM procedures to breach accounts secured with multi-factor authentication (MFA).
The ongoing marketing campaign, efficient June 2022, commences with an invoice-themed email despatched to targets containing an HTML attachment, which features a phishing URL embedded inside it.
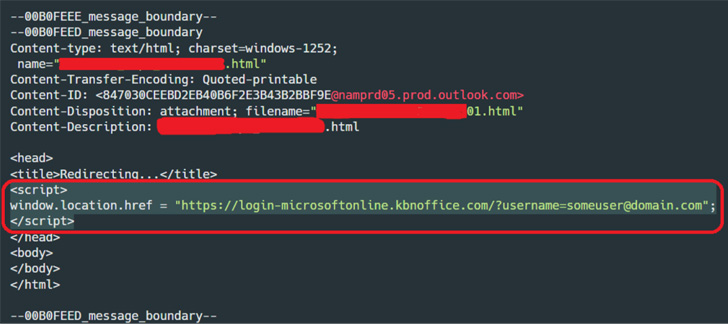
Opening the attachment via a web browser redirects the email receiver to the phishing page that masquerades as a login website page for Microsoft Workplace, but not right before fingerprinting the compromised device to determine no matter whether the sufferer is essentially the supposed target.
AitM phishing attacks go further than the conventional phishing methods developed to plunder credentials from unwitting customers, particularly in scenarios in which MFA is enabled – a security barrier that helps prevent the attacker from logging into the account with only the stolen credentials.
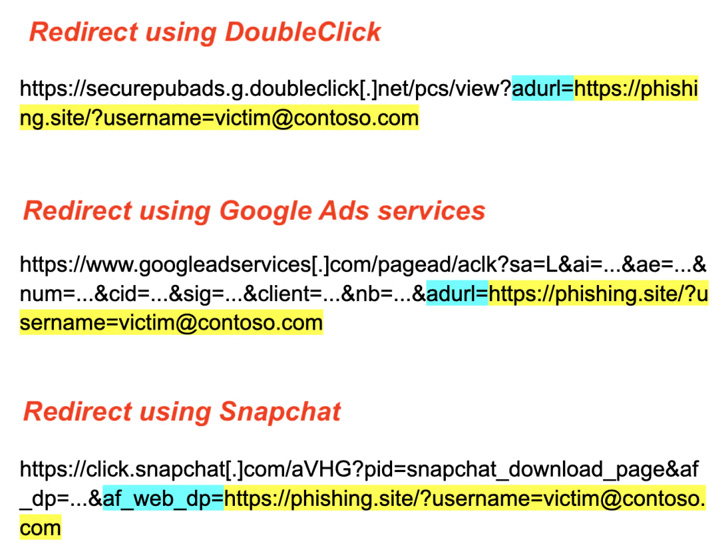
To circumvent this, the rogue landing page designed using a phishing kit functions as a proxy that captures and relays all the interaction amongst the customer (i.e., sufferer) and the email server.
“The kits intercept the HTML articles obtained from the Microsoft servers, and right before relaying it again to the sufferer, the written content is manipulated by the package in many approaches as desired, to make positive the phishing course of action functions,” the scientists said.

This also entails replacing all the one-way links to the Microsoft domains with equivalent one-way links to the phishing area so as to be certain that the back-and-forth remains intact with the fraudulent site all through the session.
Zscaler explained it observed the attacker manually logging into the account eight minutes after the credential theft, following it up by looking at email messages and checking the user’s profile data.
What’s far more, in some circumstances, the hacked email inboxes are subsequently made use of to send out added phishing emails as part of the very same campaign to conduct small business email compromise (BEC) scams.
“Even however security characteristics these types of as multi-factor authentication (MFA) add an added layer of security, they should really not be regarded as as a silver bullet to safeguard towards phishing attacks,” the scientists observed.
“With the use of sophisticated phishing kits (AiTM) and intelligent evasion approaches, threat actors can bypass equally regular as very well as state-of-the-art security solutions.”
Identified this article fascinating? Adhere to THN on Fb, Twitter and LinkedIn to examine more distinctive information we put up.
Some elements of this posting are sourced from:
thehackernews.com


 DDoS Attacks Pepper Taiwanese Government Sites
DDoS Attacks Pepper Taiwanese Government Sites