Russian cyber espionage actors affiliated with the Federal Security Provider (FSB) have been noticed making use of a USB propagating worm called LitterDrifter in attacks targeting Ukrainian entities.
Examine Level, which detailed Gamaredon’s (aka Aqua Blizzard, Iron Tilden, Primitive Bear, Shuckworm, and Winterflounder) most current tactics, branded the group as partaking in huge-scale campaigns that are followed by “facts collection endeavours aimed at precise targets, whose selection is most likely motivated by espionage targets.”
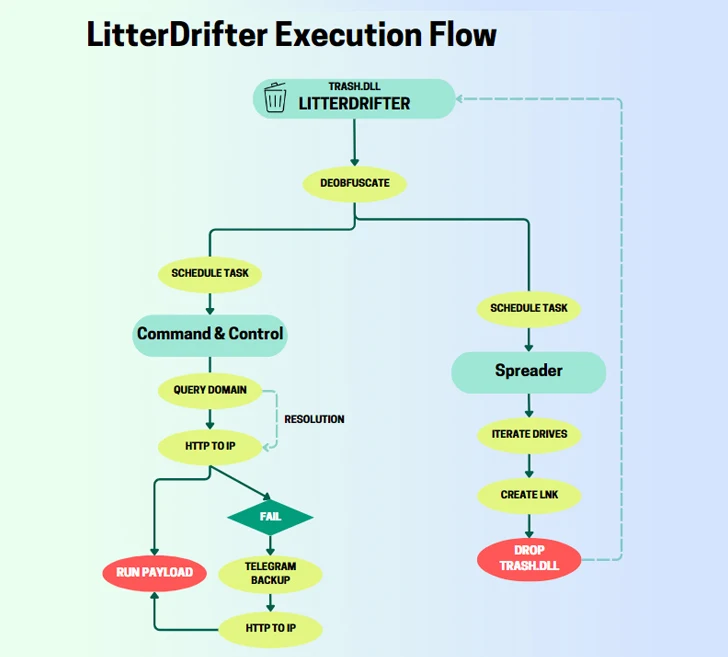
The LitterDrifter worm packs in two principal options: mechanically spreading the malware by way of connected USB drives as effectively as communicating with the menace actor’s command-and-handle (C&C) servers. It really is also suspected to be an evolution of a PowerShell-dependent USB worm that was previously disclosed by Symantec in June 2023.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Created in VBS, the spreader module is accountable for distributing the worm as a concealed file in a USB generate together with a decoy LNK which is assigned random names. The malware will get its title LitterDrifter owing to the actuality that the preliminary orchestration ingredient is named “trash.dll.”

“Gamaredon’s approach to the C&C is rather distinctive, as it utilizes domains as a placeholder for the circulating IP addresses basically applied as C2 servers,” Check out Position described.
LitterDrifter is also able of connecting to a C&C server extracted from a Telegram channel, a tactic it has consistently set to use given that at the very least the begin of the yr.
The cybersecurity firm explained it also detected indicators of attainable infection exterior of Ukraine centered on VirusTotal submissions from the U.S., Vietnam, Chile, Poland, Germany, and Hong Kong.
Gamaredon has had an energetic existence this calendar year, whilst consistently evolving its attack techniques. In July 2023, the adversary’s rapid information exfiltration capabilities came to gentle, what with the menace actor transmitting sensitive data inside of an hour of the preliminary compromise.
“It is really clear that LitterDrifter was made to guidance a substantial-scale selection procedure,” the company concluded. “It leverages easy, yet productive approaches to be certain it can reach the widest attainable set of targets in the location.”
The improvement arrives as Ukraine’s Nationwide Cybersecurity Coordination Center (NCSCC) disclosed attacks orchestrated by Russian state-sponsored hackers targeting embassies across Europe, which includes Italy, Greece, Romania, and Azerbaijan.
The intrusions, attributed to APT29 (aka BlueBravo, Cloaked Ursa, Cozy Bear, Iron Hemlock, Midnight Blizzard, and The Dukes), contain the exploitation of the lately disclosed WinRAR vulnerability (CVE-2023-38831) by using benign-wanting lures that claim to offer you BMWs for sale, a theme it has utilized in the past.

The attack chain commences with sending victims phishing email messages that contains a website link to a specially crafted ZIP file that, when released, exploits the flaw to retrieve a PowerShell script from a distant server hosted on Ngrok.
“A about craze of exploiting CVE-2023-38831 vulnerability by Russian intelligence companies hacking groups demonstrates its increasing popularity and sophistication,” NCSCC explained.
Before this 7 days, the Computer Crisis Response Crew of Ukraine (CERT-UA) unearthed a phishing marketing campaign that propagates destructive RAR archives that masquerades as a PDF document from the Security Service of Ukraine (SBU) but, in actuality, is an executable that sales opportunities to the deployment of Remcos RAT.
CERT-UA is tracking the action beneath the moniker UAC-0050, which was also linked to an additional spate of cyber attacks aimed at point out authorities in the region to supply Remcos RAT in February 2023.
Observed this write-up fascinating? Comply with us on Twitter and LinkedIn to go through additional exclusive information we post.
Some parts of this article are sourced from:
thehackernews.com


 Beware: Malicious Google Ads Trick WinSCP Users into Installing Malware
Beware: Malicious Google Ads Trick WinSCP Users into Installing Malware