Possible connections concerning a subscription-primarily based crimeware-as-a-services (Caas) alternative and a cracked copy of Cobalt Strike have been recognized in what the scientists suspect is becoming provided as a software for its prospects to stage article-exploitation routines.
Prometheus, as the provider is known as, initial arrived to light-weight in August 2021 when cybersecurity enterprise Group-IB disclosed aspects of destructive program distribution strategies undertaken by cybercriminal groups to distribute Campo Loader, Hancitor, IcedID, QBot, Buer Loader, and SocGholish in Belgium and the U.S.
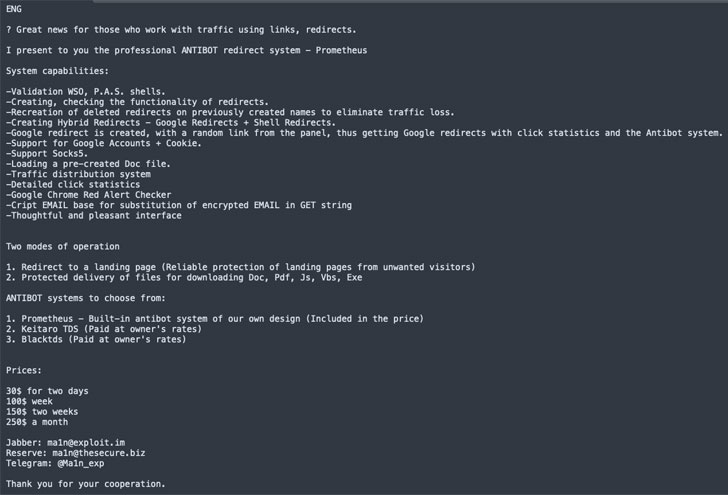
Costing $250 a month, it is really promoted on Russian underground forums as a site visitors distribution service (TDS) to help phishing redirection on a mass scale to rogue landing webpages that are built to deploy malware payloads on the focused techniques.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

“Prometheus can be deemed a entire-bodied company/system that makes it possible for threat teams to purvey their malware or phishing functions with ease,” BlackBerry Investigate and Intelligence Crew stated in a report shared with The Hacker Information. “The major components of Prometheus include a web of malicious infrastructure, malicious email distribution, illicit file-hosting by means of reputable solutions, traffic redirection and the skill to provide malicious files.”
Generally, the redirection is funneled from a person of two key resources, namely with the support of destructive adverts (aka malvertising) on genuine internet websites, or by means of sites that have been tampered to insert destructive code.
In the scenario of Prometheus, the attack chain commences with a spam email containing a HTML file or a Google Docs web site that, upon interaction, redirects the sufferer to a compromised web page hosting a PHP backdoor that fingerprints the machine to decide no matter if the to “to provide the victim with malware or redirect them to a further webpage that may possibly include a phishing scam.”
Earliest exercise connected to the operators of the service, who go by the identify “Ma1n” on hacking message boards, is stated to have commenced in October 2018, with the author joined to other illicit equipment providing large high-quality redirects and PowerMTA kits for mailing to corporate mailboxes, just before placing up Prometheus TDS for sale on September 22, 2020.
That’s not all. BlackBerry also uncovered overlaps concerning Prometheus-relevant action and an illegitimate version of the Cobalt Strike adversary simulation and danger emulation software program, elevating the risk that the copy is currently being “proliferated by the Prometheus operators them selves.”
“It’s achievable that another person connected with the Prometheus TDS is keeping this cracked copy and providing it on obtain,” the researchers explained. “It is also attainable that this cracked installation could be supplied as element of a regular playbook or a digital equipment (VM) set up.”
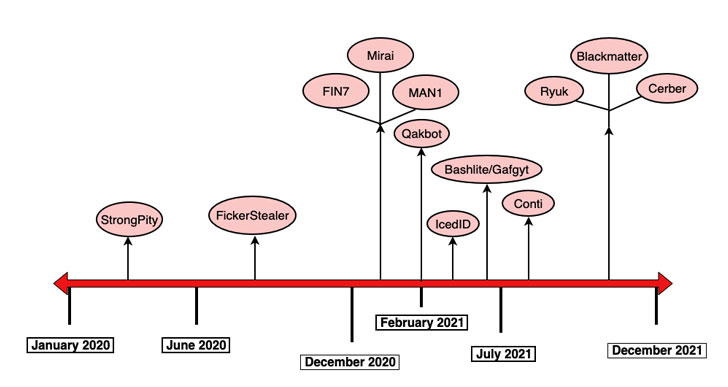
This is substantiated by the simple fact that a quantity of menace actors, together with DarkCrystal RAT, FickerStealer, FIN7, Qakbot, and IceID, as well as ransomware cartels these as REvil, Ryuk (Wizard Spider), BlackMatter, and Cerber, have employed the cracked copy in concern above the previous two years.
On prime of that, the identical Cobalt Strike Beacon has also been noticed in conjunction with things to do related with an initial entry broker tracked as Zebra2104, whose providers have been set to use by teams like StrongPity, MountLocker, and Phobos for their own campaigns.
“Even though TDS’es aren’t a new principle, the stage of complexity, aid and very low economical value provides credence to the idea that this is a pattern that is possible to increase in the risk landscape’s in the vicinity of long run,” the researchers mentioned.
“The quantity of groups that are using choices these kinds of as the Prometheus TDS, discuss to the success and efficacy of these illicit infrastructure for use products and services, which are in essence total-fledged enterprises that aid the destructive pursuits of groups no matter of their dimension, amount of resourcing or motives.”
Located this write-up interesting? Observe THN on Fb, Twitter and LinkedIn to browse extra unique articles we write-up.
Some components of this short article are sourced from:
thehackernews.com


 Cyber Threat Protection — It All Starts with Visibility
Cyber Threat Protection — It All Starts with Visibility