The Russia-connected affect operation called Doppelganger has focused Ukrainian, U.S., and German audiences by means of a mixture of inauthentic news sites and social media accounts.
These strategies are developed to amplify information designed to undermine Ukraine as effectively as propagate anti-LGBTQ+ sentiment, U.S. armed service competence, and Germany’s economic and social issues, in accordance to a new report shared with The Hacker News.
Doppelganger, explained by Meta as the “greatest and the most aggressively-persistent Russian-origin procedure,” is a pro-Russian network identified for spreading anti-Ukrainian propaganda. Active considering that at least February 2022, it has been connected to two providers named Structura Nationwide Systems and Social Structure Agency.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Activities linked with the influence procedure are recognized to leverage created web-sites as perfectly as those people impersonating authentic media – a procedure referred to as brandjacking – to disseminate adversarial narratives.
Upcoming WEBINAR Find out Insider Threat Detection with Software Response Approaches
Discover how software detection, reaction, and automated conduct modeling can revolutionize your defense from insider threats.
Be a part of Now
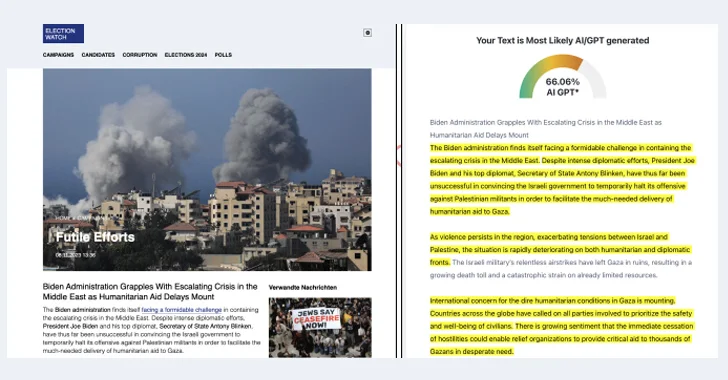
The newest campaigns are also characterized by the use of highly developed obfuscation tactics, including “manipulating social media thumbnails and strategic initially and second-phase web page redirects to evade detection, and the possible use of generative synthetic intelligence (AI) to develop inauthentic news articles,” the cybersecurity agency claimed.
The results demonstrate Doppelgänger’s evolving practices and toss mild on the use of AI for info warfare and to generate scalable impact material.
The marketing campaign targeting Ukraine is mentioned to consist of a lot more than 800 social media accounts, in addition to banking on to start with and second-stage domains to conceal the correct vacation spot. Some of these hyperlinks also use the Keitaro Traffic Distribution System (TDS) to assess the total success and effectiveness of the campaign.

A single of the notable elements of the U.S. and German campaigns is the use of inauthentic media retailers these kinds of as Election Watch, MyPride, Warfare Insider, Besuchszweck, Grenzezank, and Haüyne Scherben that publish malign content material as unique news and feeling stores.
“Doppelgänger exemplifies the enduring, scalable, and adaptable character of Russian facts warfare, demonstrating strategic tolerance aimed at progressively shifting general public feeling and behavior,” Recorded Foreseeable future stated.
It can be value pointing out that Meta, in its quarterly Adversarial Danger Report printed previous 7 days, reported it also identified a new cluster of internet sites linked to Doppelganger that are geared in the direction of U.S. and European political affairs, this kind of as migration and border security.

“Their latest web articles appears to have been copy-pasted from mainstream U.S. information outlets and altered to query U.S. democracy and endorse conspiratorial themes,” Meta reported, highlighting Election Observe as one particular of the U.S.-focused sites.
“Quickly following the Hamas terrorist attack in Israel [in October 2023], we observed these web sites commence putting up about the crisis in the Center East as a evidence of American decline and at minimum one particular site claimed Ukraine supplied Hamas with weapons.”
Meta also said it took steps to disrupt three independent covert impact operations – two from China and 1 from Russia – throughout the third quarter of 2023 that leveraged fictitious personas and media manufacturers to target audiences in India and the U.S., and share articles about Russia’s invasion of Ukraine.
It, nonetheless, famous that proactive threat sharing by the federal federal government in the U.S. linked to international election interference has been paused given that July 2023, reducing off a crucial supply of data that could be precious to disrupt destructive international strategies by complex threat actors.
Uncovered this write-up fascinating? Stick to us on Twitter and LinkedIn to browse more exceptional information we submit.
Some parts of this report are sourced from:
thehackernews.com

 Generative AI Security: Preventing Microsoft Copilot Data Exposure
Generative AI Security: Preventing Microsoft Copilot Data Exposure