Cybersecurity researchers on Thursday exposed security issues in the Android application produced by Chinese drone-maker Da Jiang Innovations (DJI) that will come with an vehicle-update mechanism that bypasses Google Play Shop and could be utilized to set up malicious applications and transmit delicate own info to DJI’s servers.
The twin stories, courtesy of cybersecurity companies Synacktiv and GRIMM, identified that DJI’s Go 4 Android application not only asks for intensive permissions and collects personal information (IMSI, IMEI, the serial selection of the SIM card), it makes of anti-debug and encryption strategies to thwart security analysis.
“This mechanism is extremely related to command and regulate servers encountered with malware,” Synacktiv reported.
“Supplied the broad permissions essential by DJI GO 4 — contacts, microphone, digicam, site, storage, transform network connectivity — the DJI or Weibo Chinese servers have pretty much complete control around the user’s phone.”
The Android app has in excess of just one million installs by means of the Google Perform Keep. But the security vulnerabilities identified in the app will not implement to its iOS version, which is not obfuscated, nor does it have the hidden update characteristic.
A “Shady” Self-Update System
GRIMM explained the investigate was carried out in response to a security audit requested by an unnamed defense and general public protection technology vendor that sought to “look into the privacy implications of DJI drones within the Android DJI GO 4 software.”
Reverse engineering the application, Synacktiv reported it uncovered the existence of a URL (“hxxps://service-adhoc.dji.com/app/update/community/test”) that it makes use of to download an application update and prompt the user to grant permission to “Install Mysterious Apps.”
“We modified this request to set off a pressured update to an arbitrary application, which prompted the person first for allowing the set up of untrusted apps, then blocking him from applying the software until eventually the update was installed,” the researchers reported.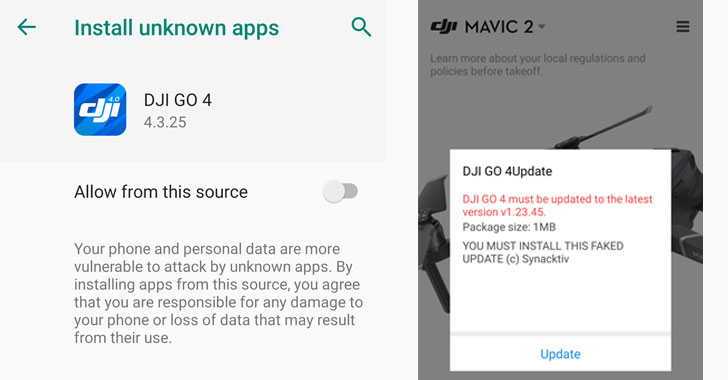
Not only is it a direct violation of Google Play Keep pointers, but the implications of this element are also monumental. An attacker could compromise the update server to goal people with destructive application updates.
Even additional regarding, the app continues to run in the track record even following it really is shut and leverages a Weibo SDK (“com.sina.weibo.sdk”) to put in an arbitrarily downloaded application, triggering the function for end users who have opted to are living stream the drone online video feed by means of Weibo. GRIMM claimed it didn’t discover any proof that it was exploited to target folks with destructive application installations.
In addition to this, the scientists observed that the app will take advantage of MobTech SDK to hoover metadata about the phone, which include monitor dimension, brightness, WLAN address, MAC tackle, BSSIDs, Bluetooth addresses, IMEI and IMSI quantities, carrier identify, SIM serial Amount, SD card data, OS language and kernel variation, and site details.
DJI Pushes Back again Towards the Conclusions
Calling the results “common software concerns,” DJI disputed the exploration, stating it contradicts “reviews from the U.S. Section of Homeland Security (DHS), Booz Allen Hamilton and some others that have found no evidence of sudden data transmission connections from DJI’s applications created for authorities and professional customers.”
“There is no proof they ended up at any time exploited, and they ended up not applied in DJI’s flight manage devices for authorities and professional consumers,” the business said, incorporating it wasn’t equipped to replicate the actions of the application restarting on its individual.
“In upcoming versions, end users will also be able to download the formal variation from Google Participate in if it is out there in their state. If users do not consent to carrying out so, their unauthorized (hacked) model of the app will be disabled for protection causes.”
DJI is the world’s biggest maker of industrial drones and has confronted greater scrutiny along with other Chinese corporations over countrywide security considerations, foremost the U.S. Division of the Inside to ground its fleet of DJI drones before this January.
Last May perhaps, the DHS experienced warned providers that their info may perhaps be at threat if they use industrial drones made in China and that they “incorporate components that can compromise your data and share your details on a server accessed outside of the enterprise by itself.”
“This choice can make apparent that the U.S. government’s considerations about DJI drones, which make up a modest part of the DOI fleet, have tiny to do with security and are rather section of a politically-enthusiastic agenda to reduce current market levels of competition and assist domestically developed drone technology, irrespective of its deserves,” the company experienced reported in a assertion again in January.
Identified this article attention-grabbing? Comply with THN on Facebook, Twitter and LinkedIn to browse additional special articles we article.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

 Smartwatch Maker Garmin Shuts Down Solutions Immediately after Ransomware Attack
Smartwatch Maker Garmin Shuts Down Solutions Immediately after Ransomware Attack