Garmin, the maker of exercise trackers, smartwatches and GPS-based wearable units, is at the moment dealing with a substantial globally provider interruption right after getting hit by a targeted ransomware attack, an personnel of the corporation told The Hacker News on condition of anonymity.
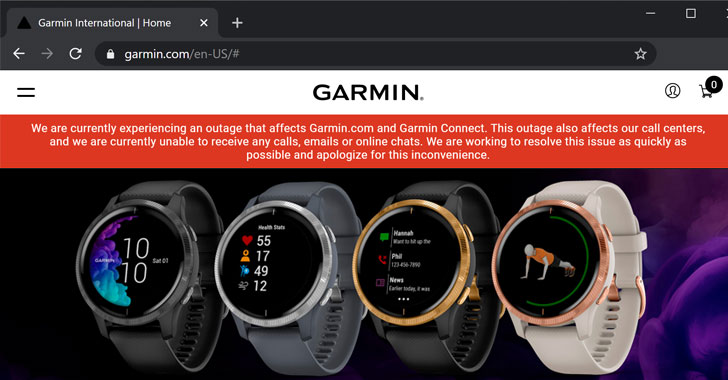
The company’s site and the Twitter account say, “We are presently suffering from an outage that influences Garmin.com and Garmin Join.”
“This outage also impacts our contact centers, and we are now unable to receive any calls, email messages or online chats. We are functioning to solve this issue as quickly as possible and apologize for this inconvenience.”
As a outcome, the corporation yesterday was compelled to briefly shut down some of its connected products and services, including Garmin Categorical, Garmin Hook up cellular, and the website—restricting tens of millions of its customers from accessing the cloud services or even syncing their watches locally to the application.
Though not much information is available on technicalities of the cyber assault, some local media studies declare hackers have managed to compromise the firm’s application and database servers with ransomware.
It also states Garmin has sent announcements to its IT staff members in Taiwan-primarily based factories announcing the future two days of planned upkeep, i.e., July 24 and 25.
A number of sources in the cybersecurity local community recommend that the cyberattack might have included WastedLocker, one particular of the specific ransomware gang, recognised as the Evil Corp or Dridex.

The modus operandi of the attackers behind WastedLocker involves compromising company networks, performing privilege escalation, and then employing lateral movement to install ransomware on precious methods prior to demanding thousands and thousands of dollars in ransom payment.
In accordance to authorities at SentinelOne, WastedLocker is a comparatively new ransomware spouse and children active for the previous number of months and has due to the fact been attacking superior-price targets across numerous industries.
WastedLocker works by using JavaScript-based SocGholish toolset to supply payload by masquerading as procedure or application updates, exploits UAC bypass procedures to elevate privileges, and leverages Cobalt Strike for lateral actions.
“All the security technology in the globe is not going to secure in opposition to identified attackers. 97% of losses stem from socially-engineered assaults and in excess of 90% are initiated by email,” Lucy Security CEO Colin Bastable shared a remark with The Hacker Information.
“There are no front traces in cyberwarfare – we are all truthful game for undesirable actors, and no entity or particular person is risk-free from cyber-assault. Prepare your individuals to detect and resist ransomware assaults – just as you patch units, patch your folks with standard, diversified, ongoing and effectively-prepared security awareness teaching to make them portion of your defenses,” Bastable included.
Gurucul CEO Saryu Nayyar also prompt the similar:
“You just will not know when the undesirable guys are heading to assault and who will be their up coming sufferer. Even so, what we do know is each organization is susceptible to ransomware attacks.”
“So, do what you can to put together and reply. Ideally, Garmin has a every day backup program for the firm’s methods and info. That is table stakes. If you get strike, at least you can get well your info.”
Garmin has not but formally confirmed no matter if the incident is a ransomware assault or not, but we have contacted the enterprise and will update the story as soon as we receive extra details on this incident.
Discovered this report interesting? Stick to THN on Fb, Twitter and LinkedIn to read extra special content we put up.

 Misconfigured S3 exposes Twilio people to Magecart attack
Misconfigured S3 exposes Twilio people to Magecart attack