Cybersecurity professionals have shed light on a new cybercrime group recognised as ShadowSyndicate (previously Infra Storm) that could have leveraged as lots of as 7 various ransomware people around the earlier yr.
“ShadowSyndicate is a danger actor that performs with numerous ransomware teams and affiliates of ransomware systems,” Team-IB and Bridewell said in a new joint report.
The actor, active given that July 16, 2022, has joined to ransomware exercise linked to Quantum, Nokoyawa, BlackCat, Royal, Cl0p, Cactus, and Enjoy strains, even though also deploying off-the-shelf put up-exploitation instruments like Cobalt Strike and Sliver as nicely as loaders such as IcedID and Matanbuchus.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
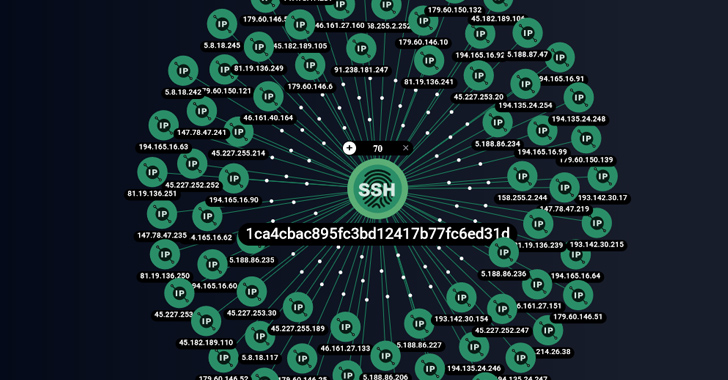
The results are based on a distinctive SSH fingerprint (1ca4cbac895fc3bd12417b77fc6ed31d) uncovered on 85 servers, 52 of which have been utilized as command-and-control (C2) for Cobalt Strike. Among those people servers are eight different Cobalt Strike license keys (or watermarks).
A majority of the servers (23) are found in Panama, adopted by Cyprus (11), Russia (9), Seychelles (8), Costa Rica (7), Czechia (7), Belize (6), Bulgaria (3), Honduras (3), and the Netherlands (3).
Group-IB explained it also uncovered further infrastructure overlaps that link ShadowSyndicate to TrickBot, Ryuk/Conti, FIN7, and TrueBot malware functions.

“Out of the 149 IP addresses that we connected to Cl0p ransomware affiliate marketers, we have seen, considering the fact that August 2022, 12 IP addresses from 4 distinctive clusters improved ownership to ShadowSyndicate, which suggests that there is some potential sharing of infrastructure involving these teams,” the businesses said.
The disclosure will come as the German law enforcement authorities declared a second qualified strike versus actors connected with the DoppelPaymer ransomware team, some of whom had been qualified before this March, executing research warrants against two suspects in Germany and Ukraine.
The persons, a 44-yr-outdated Ukrainian and a 45-calendar year-previous German nationwide, are alleged to have held critical obligations in the network and received illicit proceeds from the ransomware attacks. Their names have been not disclosed.
The advancement also follows a joint advisory issued by the U.S. Federal Bureau of Investigation (FBI) and the Cybersecurity and Infrastructure Security Agency (CISA) about a double extortion actor named Snatch (previously Workforce Truniger) that has qualified a wide array of critical infrastructure sectors because mid-2021.
“Snatch danger actors employ various different solutions to gain accessibility to and manage persistence on a victim’s network,” the agencies mentioned, contacting out their reliable evolution of strategies and the potential of the malware to evade detection by rebooting Windows programs into Harmless Manner.
“Snatch affiliates primarily depend on exploiting weaknesses in Distant Desktop Protocol (RDP) for brute-forcing and attaining administrator qualifications to victims’ networks. In some situations, Snatch affiliates have sought out compromised qualifications from criminal community forums/marketplaces.”
The U.S. Division of Homeland Security (DHS), in its most recent Homeland Threat Evaluation report, observed that ransomware groups are continuously acquiring new procedures to make improvements to their capacity to fiscally extort victims, producing 2023 the next most financially rewarding 12 months following 2021.
“These groups have elevated their use of multilevel extortion, in which they encrypt and exfiltrate their targets’ info and typically threaten to publicly release stolen info, use DDoS attacks, or harass the victim’s customers to coerce the sufferer to fork out,” the DHS report stated.
Upcoming WEBINARFight AI with AI — Battling Cyber Threats with Future-Gen AI Instruments
Completely ready to deal with new AI-driven cybersecurity problems? Be part of our insightful webinar with Zscaler to tackle the expanding menace of generative AI in cybersecurity.
Supercharge Your Skills
Akira is a circumstance in position. The ransomware has expanded its get to since emerging as a Windows-based mostly menace in March 2023 to include things like Linux servers and VMWare ESXi digital machines, underscoring its means to speedily adapt to developments. As of mid-September, the team has properly hit 110 victims in the U.S. and the U.K.
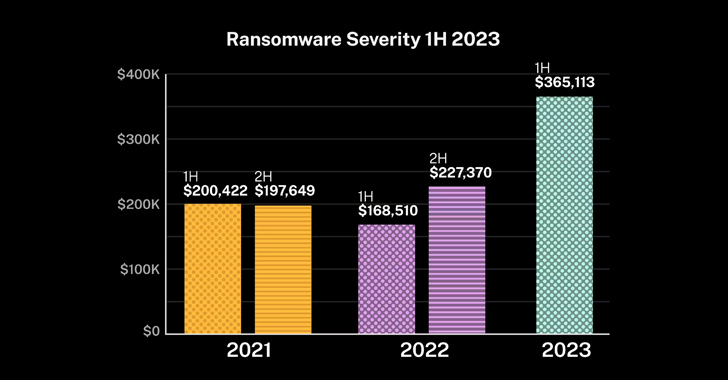
The resurgence of ransomware attacks has also been accompanied by a spike in cyber insurance policy statements, with over-all statements frequency growing 12% in the first 50 percent of the 12 months in the U.S. and victims reporting an typical decline total of extra than $365,000, a 61% leap from the second half of 2022.
“Organizations with far more than $100 million in profits observed the largest enhance in frequency, and even though other profits bands have been more stable, they also confronted surges in statements,” cyber insurance firm Coalition stated.
The regular flux in the threat landscape is greatest exemplified by BlackCat, Cl0p, and LockBit, which have remained some of the most prolific and evolutionary ransomware family members in recent months, generally targeting compact and big enterprises spanning banking, retail, and transportation sectors. The variety of lively RaaS and RaaS-relevant teams has developed in 2023 by 11.3%, climbing from 39 to 45.
A report from eSentire final 7 days thorough two LockBit attacks in which the e-crime group was noticed leveraging the sufferer companies’ internet-exposed distant monitoring and management (RMM) resources (or their personal) to spread the ransomware across the IT surroundings or drive it to their downstream customers.
The reliance on this kind of living-off-the-land (LotL) techniques is an attempt to stay clear of detection and confuse attribution efforts by blending destructive and reputable use of IT management resources, the Canadian business claimed.
In a further instance of a BlackCat attack highlighted by Sophos this thirty day period, the attackers were witnessed encrypting Microsoft Azure Storage accounts immediately after attaining entry to an unnamed customer’s Azure portal.
“For the duration of the intrusion, the menace actors have been observed leveraging a variety of RMM equipment (AnyDesk, Splashtop, and Atera), and using Chrome to obtain the target’s mounted LastPass vault by using the browser extension, in which they attained the OTP for accessing the target’s Sophos Central account, which is utilised by prospects to handle their Sophos merchandise,” the enterprise mentioned.
“The adversary then modified security policies and disabled Tamper Defense in Central just before encrypting the customer’s units and distant Azure Storage accounts by means of ransomware executable with the extension .zk09cvt.”
Discovered this short article attention-grabbing? Adhere to us on Twitter and LinkedIn to study additional unique content material we article.
Some elements of this short article are sourced from:
thehackernews.com

 Essential Guide to Cybersecurity Compliance
Essential Guide to Cybersecurity Compliance