In the quick-paced cybersecurity landscape, merchandise security takes centre stage. DevSecOps swoops in, seamlessly merging security procedures into DevOps, empowering teams to tackle worries. Let’s dive into DevSecOps and check out how collaboration can give your team the edge to fight cyber villains.
Application security and merchandise security
Regrettably, software security groups normally intervene late in the enhancement course of action. They retain the security level of uncovered program, making certain the integrity and confidentiality of eaten or developed details. They concentration on securing info flows, isolating environments with firewalls, and implementing strong person authentication and accessibility command.
Products security groups goal to promise the intrinsic trustworthiness of programs. They recommend resources and assets, making them available to developers and functions. In the DevSecOps strategy, each individual group is liable for the security of the apps they build. These teams utilize safe coding methods, execute static and dynamic testing, and ensure that apps are resistant to exploitation, delicate details stays safe, and the programs can manage masses and attacks.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Reinforce solution security
The SecOps guild, which intervenes in solution teams, commonly has a cross-functional purpose, making certain regularity between jobs for both of those technological and economical motives. They stimulate DevOps teams to use the chosen security equipment and assure right implementation. This step rationalizes security means, and further more collaboration lets just about every DevOps group to benefit from the get the job done and practical experience of other people.
There could be a very simple way to bolster products security with collaborative resources:
1 — Plan mitigation
In the occasion of a security incident or vulnerability, being aware of that the probable injury is recognized and controlled is necessary for SecOps. This is why offering profiling information and approaches for users to sandbox the software ranks among the the best points they can do. It may well start off with using containers with limited privileges but coming up with a security profile can just take it a phase more. Providing AppArmor profile or Seccomp filters guarantees that even if the application is compromised, each the attacker’s opportunity and attack surface keep on being very restricted and known. Incident response and forensic teams will be grateful for this.
2 — Establish irregular behavior
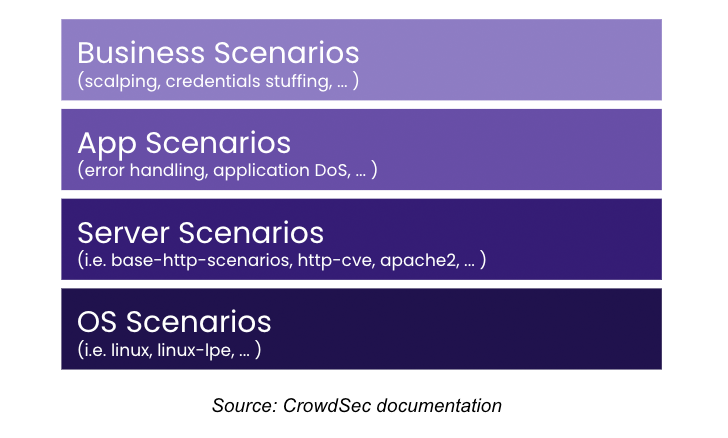
Developers can identify error indicators throughout application enhancement, commonly in the form of error messages in logs. DevOps groups can ascertain if specified error occurrences signify irregular or offensive conduct by categorizing mistake messages and associating them with irregular behavior in shared artifact repositories on Github or any other collaborative platform. Employing structured logging also makes their later assessment considerably much easier.
3 — Compare, rely, and correlate
These indicators must be as opposed, counted, and correlated. Several unsuccessful authentication tries or tries to post incorrect details or document formats are responsible markers of sudden actions. Relying on a centralized software like a SIEM for this task might contradict some DevOps concepts. Rather, software decisions ought to be created promptly and regionally, adapting at the speed of the application as necessary. There are a lot of description languages, enabling the technology of behavioral scenarios immediately from developer-supplied knowledge with minimum integration into the CI/CD process.
4 — Consider motion
As soon as deviant conduct is identified, steps must be taken to guard the application. Actions could consist of slowing down a circulation that could harm an application’s processing abilities, revoking an attacker’s entry, or banning their IP. People with a SOAR can use it to reply swiftly to security gatherings, although other people might like decentralized decision-making using instruments like CrowdSec to interface with web entrance finishes, authentication servers, or firewalls.
5 — Share security alerts
As SecOps typically do the job with numerous DevOps groups, tools that figure out abnormal habits and provide graduated responses are valuable. Sharing security alerts makes it possible for just about every DevOps group to reward from others’ ordeals. By associating a circumstance with each and every code library to characterize irregular behavior, time is saved each and every time one more crew employs that library. Eventualities stored in neighborhood repositories are obtainable to all, allowing for the creation of a security framework for every single software that integrates them. In the close, securing apps largely depends on the expertise beforehand obtained by all DevSecOps teams.
6 — Share much more
Collaborative resources help sharing of attack alerts, working with frameworks like MITRE ATT&CK for example. An aggressive resource banned for offensive habits on one software can be banned across all corporation programs. For instance, every single CrowdSec Security Engine could share alerts on a nearby or international scale, so attackers’ IPs are regarded and promptly blocked, safeguarding applications and knowledge while assuaging the burden on security infrastructures.
Much better alongside one another
DevSecOps teams unite to safe their purposes, fostering collaboration for top rated-notch trustworthiness and information security. Embracing instruments that leverage collective experience elevates protection against a rising horde of cyber criminals. By sharing attack signals and harnessing group-sourced intel, organizations stand more powerful in unison, squaring off in opposition to cyber threats. Ultimately, it can be all about teamwork, proving that we’re an unstoppable drive from cyberattacks.
You can demo the collaborative resource stated in the short article by traveling to https://reserving.crowdsec.net/reserve-a-demo
Note: This post is authored by Jerome Clauzade at CrowdSec.
Identified this report fascinating? Comply with us on Twitter and LinkedIn to examine far more special articles we article.
Some components of this posting are sourced from:
thehackernews.com

 Researchers Uncover SideWinder’s Latest Server-Based Polymorphism Technique
Researchers Uncover SideWinder’s Latest Server-Based Polymorphism Technique