Menace actors are leveraging accessibility to malware-contaminated Windows and macOS devices to deliver a proxy server software and use them as exit nodes to reroute proxy requests.
In accordance to AT&T Alien Labs, the unnamed business that delivers the proxy assistance operates much more than 400,000 proxy exit nodes, despite the fact that it really is not quickly obvious how numerous of them were being co-opted by malware put in on infected equipment without having user understanding and interaction.
“While the proxy web page promises that its exit nodes come only from customers who have been educated and agreed to the use of their system,” the cybersecurity firm claimed it discovered evidence where “malware writers are setting up the proxy silently in infected techniques.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
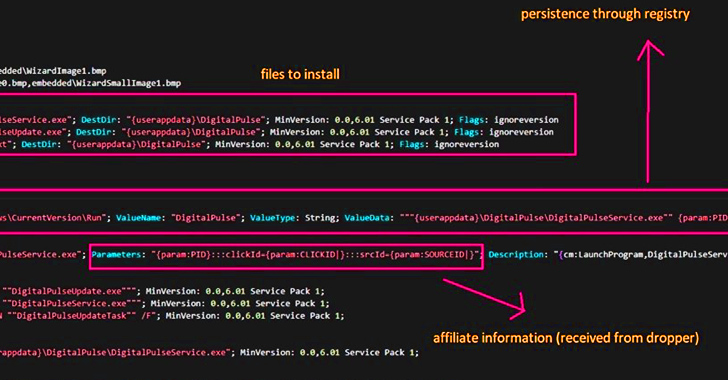
Several malware households have been observed offering the proxy to buyers seeking for cracked application and games. The proxy application, written in the Go programming language, is able of concentrating on both equally Windows and macOS, with the previous capable of evading detection by applying a legitimate digital signature.

In addition to obtaining further more recommendations from a remote server, the proxy is configured to gather facts about the hacked devices, which include managing processes, CPU and memory utilization, and battery status. What’s additional, the set up of the proxy computer software is accompanied by the deployment of more malware or adware factors.
“The monetization of malware propagating proxy servers through an affiliate program is troublesome, as it generates a formal framework to increase the pace at which this menace will spread,” security researcher Ofer Caspi reported.
The disclosure builds upon prior conclusions from AT&T in which macOS machines compromised by AdLoad adware are currently being corralled into a giant, residential proxy botnet, increasing the risk that the operators of AdLoad could be jogging a spend-per-Install marketing campaign.
AdLoad is one particular the largest identified adware strains concentrating on macOs. Regarded to impersonate well-liked movie players and other greatly-employed programs, Adload hijacks browsers and forces victims to go to possibly destructive websites, enabling cybercriminals to revenue off the schemes.
“The pervasive nature of AdLoad possibly infecting countless numbers of equipment globally — suggests that end users of MacOS units are a valuable target for the adversaries powering this malware and are staying tricked to down load and put in undesirable applications,” the enterprise reported.
“The rise of malware delivering proxy programs as a valuable expense, facilitated by affiliate packages, highlights the crafty mother nature of adversaries’ methods. These proxies, covertly installed by means of alluring offers or compromised computer software, provide as channels for unauthorized financial gains.”

The development arrives as macOS units have significantly become a prized target, with the dark web witnessing a 1,000% surge in danger actors promoting data stealer strains and subtle equipment that can circumvent macOS security functions, particularly Gatekeeper and Transparency, Consent and Manage (TCC) given that 2019.
“In 2022 and the initially 50 percent of 2023, macOS-targeting exercise has intensified,” Accenture said in a report printed this month.
“A mixture of the growing use of macOS in corporate environments, the superior possible earnings of risk actors inclined and in a position to concentrate on macOS and the surging desire for macOS resources and wares propose this pattern will continue.”
Romanian cybersecurity firm Bitdefender, in its individual macOS Threat Landscape Report, reported that Mac buyers are predominantly specific by three vital threats in the past 12 months: Trojans (51.8%), Possibly Unwelcome Applications (25.3%), and Adware (22.6%).
“EvilQuest remains the one most typical piece of malware targeting Macs at 52.7%,” it noted. “Trojans created to exploit unpatched vulnerabilities existing a serious danger to buyers who typically postpone putting in the latest security patches from Apple.”
Located this write-up appealing? Observe us on Twitter and LinkedIn to study more unique written content we article.
Some elements of this write-up are sourced from:
thehackernews.com

 HiatusRAT Malware Resurfaces: Taiwan Firms and U.S. Military Under Attack
HiatusRAT Malware Resurfaces: Taiwan Firms and U.S. Military Under Attack