Purchaser engagement platform Twilio on Monday disclosed that a “advanced” menace actor received “unauthorized access” applying an SMS-centered phishing campaign aimed at its employees to acquire facts on a “confined number” of accounts.
The social-engineering attack was bent on stealing personnel qualifications, the enterprise claimed, contacting the as-but-unknown adversary “perfectly-structured” and “methodical in their actions.” The incident arrived to light on August 4.
“This wide based mostly attack versus our staff base succeeded in fooling some personnel into giving their credentials,” it mentioned in a detect. “The attackers then made use of the stolen credentials to obtain access to some of our interior units, the place they have been equipped to access particular client details.”

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

The communications giant has 268,000 lively buyer accounts, and counts businesses like Airbnb, Box, Dell, DoorDash, eBay, Glassdoor, Lyft, Salesforce, Stripe, Twitter, Uber, VMware, Yelp, and Zendesk amongst its clients. It also owns the well known two-factor authentication (2FA) service Authy.
Twilio, which is still continuing its investigation into the hack, pointed out it can be performing immediately with customers who had been impacted. It didn’t disclose the scale of the attack, the quantity of personnel accounts that had been compromised, or what kinds of knowledge could have been accessed.
Phishing schemes, equally leveraging email and SMS, are identified to lean on intense scare strategies to coerce victims into handing around their sensitive information. This is no exception.
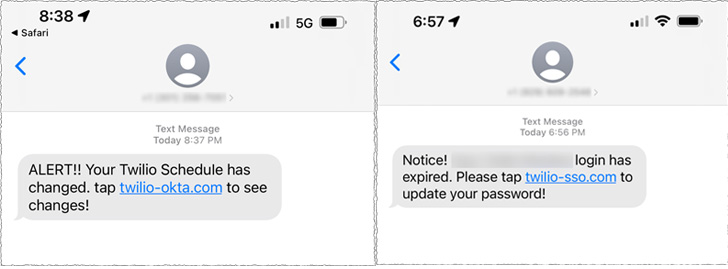
The SMS messages are reported to have been despatched to both current and former staff members masquerading as coming from its IT section, luring them with password expiry notifications to click on malicious links.
The URLs included words these kinds of as “Twilio,” “Okta,” and “SSO” (shorter for single sign-on) to increase the opportunity of accomplishment and redirected the victims to a phony web site that impersonated the company’s sign-in web page. It truly is not right away crystal clear if the breached accounts have been secured by 2FA protections.

Twilio explained the messages originated from U.S. provider networks and that it labored with the telecom support and hosting companies to shut down the scheme and the attack infrastructure utilized in the campaign. The takedown efforts, however, have been offset by the attackers migrating to other carriers and hosting vendors.
“Furthermore, the threat actors seemed to have complex skills to match employee names from sources with their phone figures,” it noted.
The San Francisco-centered company has because revoked entry to the compromised employee accounts to mitigate the attack, introducing it’s examining additional specialized safeguards as a preventive measure.
The disclosure arrives as spear-phishing continues to be a main risk confronted by enterprises. Past month, it emerged that the $620 million Axie Infinity hack was the consequence of one of its previous staff members acquiring tricked by a fraudulent position supply on LinkedIn.
Uncovered this write-up interesting? Comply with THN on Facebook, Twitter and LinkedIn to study far more exceptional material we submit.
Some components of this posting are sourced from:
thehackernews.com


 Report Provides Updates on July’s Maui Ransomware Incident
Report Provides Updates on July’s Maui Ransomware Incident