Patches have been released for two security flaws impacting the Curl details transfer library, the most intense of which could potentially end result in code execution.
The checklist of vulnerabilities is as follows –
- CVE-2023-38545 (CVSS score: 7.5) – SOCKS5 heap-primarily based buffer overflow vulnerability
- CVE-2023-38546 (CVSS score: 5.) – Cookie injection with none file
CVE-2023-38545 is the a lot more significant of the two, and has been described by the project’s guide developer, Daniel Stenberg, as “likely the worst Curl security flaw in a extensive time.” It influences libcurl versions 7.69. to and which includes 8.3..

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

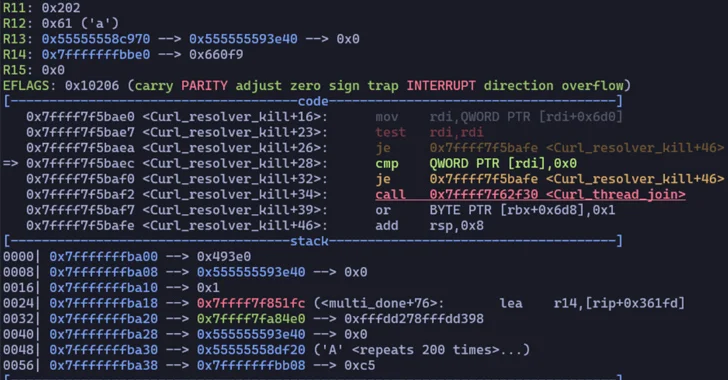
“This flaw makes Curl overflow a heap-dependent buffer in the SOCKS5 proxy handshake,” the maintainers mentioned in an advisory. “When Curl is requested to pass alongside the hostname to the SOCKS5 proxy to let that to take care of the address as a substitute of it finding carried out by Curl alone, the maximum size that hostname can be is 255 bytes.”
“If the hostname is detected to be longer than 255 bytes, Curl switches to area title resolving and rather passes on the resolved tackle only to the proxy. Because of to a bug, the area variable that indicates ‘let the host solve the name’ could get the incorrect worth all through a slow SOCKS5 handshake, and opposite to the intention, duplicate the too extended hostname to the focus on buffer instead of copying just the fixed deal with there.”
Curl explained the vulnerability could probably be exploited without the have to have for a denial-of-assistance attack and an overflow could be triggered with a malicious HTTPS server carrying out a redirect to a specially crafted URL.
“Seeing that Curl is an ubiquitous undertaking it can be assumed with good self-confidence that this vulnerability will get exploited in the wild for remote code execution, with additional refined exploits being formulated,” JFrog explained. “Nonetheless – the established of pre-ailments essential in get for a device to be vulnerable is a lot more restrictive than originally considered.”

“A legitimate exploit would require an attacker to result in code execution by, for illustration, passing a hostname to a web app that would result in the code execution in Curl,” Johannes B. Ullrich, the dean of analysis at the SANS Technology Institute, said. “Subsequent, the exploit only exists if Curl is made use of to connect to a SOCKS5 proxy. This is a further dependency, making exploitation fewer possible.”
The 2nd vulnerability, which impacts libcurl variations 7.9.1 to 8.3., makes it possible for a bad actor to insert cookies at will into a managing application making use of libcurl beneath specific situations.
Patches for equally flaws are accessible in model 8.4. launched on Oct 11, 2023. Especially, the update makes certain that Curl no more time switches to regional solve method if a hostname is way too very long, therefore mitigating the risk of heap-based mostly buffer overflows.
“This spouse and children of flaws would have been unattainable if Curl had been prepared in a memory-risk-free language as an alternative of C, but porting Curl to a different language is not on the agenda,” Stenberg included.
Found this article exciting? Comply with us on Twitter and LinkedIn to examine far more exclusive material we article.
Some elements of this report are sourced from:
thehackernews.com

 Over 17,000 WordPress Sites Compromised by Balada Injector in September 2023
Over 17,000 WordPress Sites Compromised by Balada Injector in September 2023