Two file administration applications on the Google Play Retail outlet have been learned to be spy ware, placing the privacy and security of up to 1.5 million Android end users at risk. These apps engage in misleading habits and secretly mail delicate consumer data to destructive servers in China.
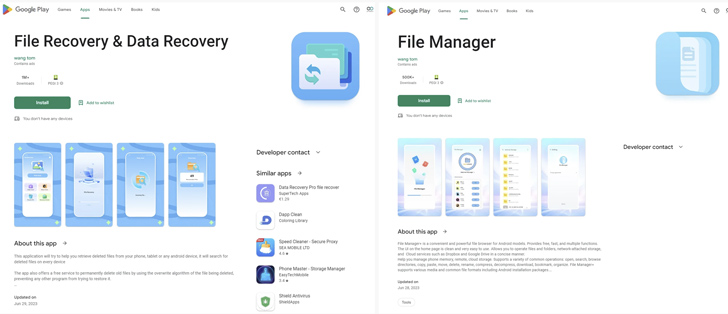
Pradeo, a major cell security firm, has uncovered this alarming infiltration. The report reveals that equally spy ware applications, particularly File Restoration and Data Restoration (com.location.new music.filedate) with in excess of 1 million installs, and File Supervisor (com.file.box.grasp.gkd) with around 500,000 installs, are made by the same team. These seemingly harmless Android applications use comparable malicious techniques and mechanically start when the product reboots devoid of consumer input.
Contrary to what they claim on the Google Engage in Retail outlet, where the two apps guarantee users that no knowledge is gathered, Pradeo’s analytics engine has observed that numerous personalized info is collected devoid of users’ knowledge. Stolen details features get in touch with lists, media information (photographs, audio data files and videos), true-time place, mobile place code, network supplier aspects, SIM service provider network code, functioning program variation, machine brand name, and design.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
What is specially alarming is the significant amount of money of data transferred by these spyware applications. Each and every application performs a lot more than a hundred transmissions, a substantial amount of money for destructive activities. At the time the knowledge is gathered, it is sent to several servers in China, which are deemed malicious by security experts.
To make issues worse, the builders of these adware apps have applied sneaky techniques to appear extra authentic and make it difficult to uninstall them. Hackers artificially elevated the amount of downloads of applications with install Farms or mobile product emulators, making a fake sense of trustworthiness. Also, equally apps have highly developed permissions that let them to cover their icons on the household display, building it tough for unsuspecting consumers to uninstall them.
Pradeo delivers security suggestions for people today and businesses in gentle of this disturbing discovery. Men and women must be cautious when downloading applications, specially those without scores if they assert a big person foundation. It is exceptionally critical to examine and understand app permissions right before accepting them to stop breaches like this.
Upcoming WEBINAR🔐 Privileged Entry Administration: Master How to Conquer Key Issues
Explore diverse approaches to conquer Privileged Account Administration (PAM) worries and degree up your privileged entry security system.
Reserve Your Place
Businesses should prioritize educating their employees about cellular threats and placing up automatic cellular detection and reaction devices to defend towards probable attacks.
This incident highlights the ongoing fight involving cybersecurity authorities and destructive actors exploiting unsuspecting customers. Malware and adware attacks are continually evolving and finding new techniques to infiltrate trustworthy platforms like the Google Enjoy Keep. As a user, it is imperative to remain vigilant, exercise warning when downloading apps, and depend on dependable sources for software.
Discovered this short article interesting? Follow us on Twitter and LinkedIn to read more exceptional articles we submit.
Some parts of this posting are sourced from:
thehackernews.com


 Vishing Goes High-Tech: New ‘Letscall’ Malware Employs Voice Traffic Routing
Vishing Goes High-Tech: New ‘Letscall’ Malware Employs Voice Traffic Routing