The U.S. Section of the Treasury imposed sanctions in opposition to a Russian woman for using part in the laundering of virtual forex for the country’s elites and cybercriminal crews, which includes the Ryuk ransomware group.
Ekaterina Zhdanova, for each the division, is said to have facilitated massive cross border transactions to assist Russian persons to achieve obtain to Western financial marketplaces and circumvent intercontinental sanctions.
“Zhdanova utilizes entities that absence Anti-Cash Laundering/Combatting the Financing of Terrorism (AML/CFT) controls, these kinds of as OFAC-designated Russian cryptocurrency exchange Garantex Europe OU (Garantex),” the treasury office stated past 7 days.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“Zhdanova relies on many strategies of worth transfer to shift resources internationally. This features the use of dollars and leveraging connections to other global income laundering associates and businesses.”
It can be truly worth noting that Garantex was beforehand sanctioned by the U.S. in April 2022, coinciding with the takedown of the dark web market known as Hydra.
Zhdanova has also been accused of featuring services to individuals connected with the Russian Ryuk ransomware group, laundering about $2.3 million of suspected target payments on behalf of a Ryuk ransomware affiliate in 2021.
Ryuk, a predecessor to the Conti ransomware, first emerged on the threat landscape in 2018, and has compromised governments, academia, health care, producing, and technology businesses all over the world.

Previously this February, a 30-calendar year-old Russian citizen named Denis Mihaqlovic Dubnikov pleaded guilty in the U.S. to revenue laundering costs and for making an attempt to conceal the source of cash acquired in link with Ryuk ransomware attacks.
Ransomware Proceeds to Evolve
The improvement comes as a record 514 ransomware victims had been documented for the thirty day period of September 2023, registering a 153% increase calendar year-in excess of-12 months, and up from 502 in July and 390 in August.
Almost 100 of people attacks have been attributed to nascent groups like LostTrust and RansomedVC. Some of the other new entrants observed in recent months contain Dark Angels, Knight, Cash Message, and Excellent Day.
“The file ranges of ransomware attacks are partly the final result of the emergence of new danger actors like RansomedVC,” NCC Group reported late very last month.
“RansomedVC operates as ‘penetration testers.’ Having said that, its approach to extortion also incorporates the assert that any vulnerabilities discovered in their targets’ network will be described in compliance with Europe’s Typical Data Safety Regulation (GDPR).
The inflow of new teams demonstrates the evolving ransomware landscape, even as more set up danger actors proceed to adapt and refine their practices and techniques to dodge security controls.
Last thirty day period, Palo Alto Networks Device 42 described BlackCat’s addition of a utility codenamed Munchkin to its arsenal in order to propagate the ransomware payload to remote machines and shares on a target corporation network.
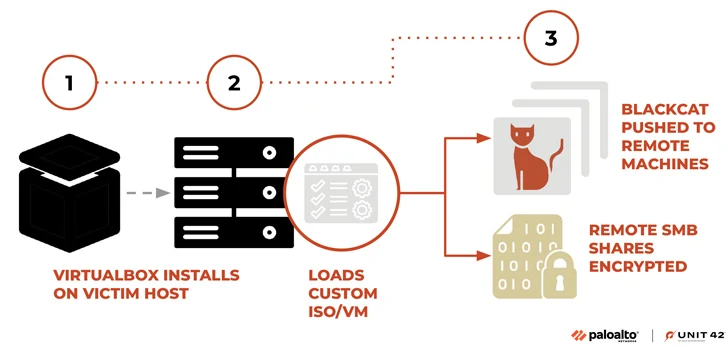
“This tooling delivered a Linux-dependent operating procedure (OS) operating Sphynx,” Device 42 researchers stated. “Threat operators can use this utility to run BlackCat on remote machines, or to deploy it to encrypt distant Server Information Block (SMB)/Prevalent Internet File Shares (CIFS).”

The diversification of ransomware is evidenced by the fact that hacktivist collectives these types of as GhostSec – which is part of The Five Family members – have entered the fray, releasing a custom made locker named GhostLocker for money get.
“Even if GhostLocker is not profitable in the [ransomware-as-a-service] current market, it looks noticeable that it is a turning issue as a product,” SOCRadar reported. “The actuality that it is fairly reduced-priced, functions with a really small share basis, and is available to just about anyone can boost ransomware attacks to extreme ranges.”
Cybersecurity organization Uptycs, in its possess examination of GhostSec and GhostLocker, explained the move as a “stunning departure from their earlier things to do and stated agenda,” presented the collective’s historical past of focusing on Israeli entities in guidance of Palestine.
The spike in ransomware attacks has also prompted an alliance of 50 international locations, referred to as the International Counter Ransomware Initiative, pledged hardly ever to spend ransom needs in a bid to discourage financially motivated actors and ransomware gangs from profiting off such strategies.
“To protect in opposition to ransomware, it is very important to adopt a in depth protection strategy,” Uptycs mentioned. “This technique should really encompass resilient backup programs, helpful security software program, consumer instruction, and a proactive incident reaction plan.”
Identified this report attention-grabbing? Adhere to us on Twitter and LinkedIn to read through extra exceptional articles we write-up.
Some sections of this posting are sourced from:
thehackernews.com


 StripedFly Malware Operated Unnoticed for 5 Years, Infecting 1 Million Devices
StripedFly Malware Operated Unnoticed for 5 Years, Infecting 1 Million Devices