Multi-cloud adoption is at an all-time higher. Though cybersecurity firm Fortinet approximated in 2021 that 76% of organizations were working with at minimum two cloud support suppliers (CSP), IT management supplier Flexera located in 2022 that already 89% of enterprises experienced a multi-cloud technique in line.
As a benefits, an expanding share of businesses’ digital property are no more time in just one area, both on-premises or in the cloud, but spread all over various bodily and digital areas and operate by numerous services companies.
Therefore, the traditional security techniques do not do the job any longer, Katy Anton, vice-president of security architecture at JPMorgan Chase, argued during a presentation at the Cloud & Cyber Security Expo, in London on March 8-9, 2023.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“In standard cybersecurity approaches that we’ve been utilized to, almost everything is put inside of a castle. We have a stringent perimeter where by we can area our worthwhile assets and we’re on the lookout to authorize trustworthy buyers to obtain this details,” she defined.
“In contemporary architecture, this way of doing is no longer suitable given that our valuable info is spread all over numerous third-party vendors. This forces us to undertake a zero belief solution, based on the minimum-privilege entry theory and targeted on securing identities instead than assets, with potent key keys management, authentication and API security.”
Numerous businesses have transitioned to the multi-cloud tactic with no adapting their security tactic, Anton explained.
She famous that Gartner has uncovered that 90% or businesses will inappropriately expose their details in the cloud.
One of the critical good reasons for that, she argued, is that numerous companies wrongly believe that the CSPs fully ensure the security of the facts they hand in excess of to them.
“Gartner predicted that 99% of cyber incidents will be triggered by misconfigurations from the customer by 2025. This is tremendously because of to a misunderstanding of the shared responsibility product,” Anton famous.
A 3-Tier Framework
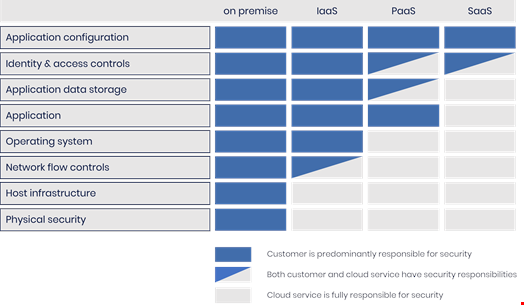
The shared accountability model is a cloud security framework typically used by CSPs like Amazon Web Providers (AWS), Microsoft Azure and Google Cloud, explaining where their security duty finishes, and wherever the customer’s duty starts.
The Cloud Standards Client Council, an advocacy group for cloud end users, describes three tiers of cloud assistance contracts – software-as-a-service (SaaS), platform-as-a-provider (PaaS) infrastructure-as-a-provider (IaaS) – and notes that users’ duties generally raise as they move from SaaS to PaaS to IaaS.
SaaS is a software shipping model the place the vendor centrally hosts an software in the cloud that can be employed by a subscriber. Dropbox, Zoom, Microsoft 365 or Google Workspace typically suggest a SaaS deal. In this design, the service provider is accountable for software security, as effectively as its routine maintenance and management.
PaaS is composed in giving a system, such as RedHat OpenShift or Google Kubernetes Motor for occasion, that can be acquired and made use of to build, run and handle apps. In this model, the vendor delivers each the hardware and application and is accountable for security of the system and its infrastructure.
IaaS is an infrastructure shipping design wherein a vendor gives a large vary of computing resources such as virtualized servers, storage and network devices about the internet. AWS, Azure and GCP are the leaders of IaaS. In this model, the consumer is usually liable for preserving security of something they have or install on the cloud infrastructure (functioning technique, applications, containers, workloads, knowledge, code…).
In all a few models, nevertheless, some security obligations will constantly be the customer’s, such as identity and access management (IAM) of the belongings, consumer security and qualifications or endpoint security. Other security responsibilities will commonly drop beneath the CSP’s remit, like the safety and security of the physical layer and all linked hardware and infrastructure, like the amenities that run cloud sources.
Sharing the Duty for Security Shortcomings
National Cyber Security Centre (NCSC) sets out a 3-tier shared obligation security product for cloud security, nevertheless this is only a framework and not regulation.
 The 3 tiers of the shared security product in accordance to the UK’s Nationwide Cyber Security Centre. Resource: NCSC
The 3 tiers of the shared security product in accordance to the UK’s Nationwide Cyber Security Centre. Resource: NCSC
Deryck Mitchelson, Verify Point’s EMEA industry CISO, spoke at the Cloud & Cyber Security Expo about how he assisted the Scottish department of the UK’s National Wellness Services (NHS) transfer to a native multi-cloud architecture.
He agreed with Anton that understanding the framework is critical in securely implanting a multi-cloud method.
Mitchelson explained to Infosecurity, “Many of our prospects get started their multi-cloud journey with no completely knowing the place their duties are with regards to security.”
He additional, “Organizations must go by way of their shared duty model with their CSP, look at advice from govt organizations and talk to their security supplier, which can supply non-seller insights, or even consider care of some the weighty lifting absent from them as nicely.”
The fault, nevertheless, is not only down to cloud customers, Mitchelson said. “Cloud suppliers need to be a great deal more clear in what they do – and what they really don’t do – and offer a lot extra security by default.”
Some pieces of this short article are sourced from:
www.infosecurity-journal.com


 Does Your Help Desk Know Who’s Calling?
Does Your Help Desk Know Who’s Calling?