Threat actors have revealed but one more round of malicious packages to Python Bundle Index (PyPI) with the aim of providing info-stealing malware on compromised developer equipment.
Curiously, while the malware goes by a wide variety of names like ANGEL Stealer, Celestial Stealer, Fade Stealer, Leaf $tealer, PURE Stealer, Satan Stealer, and @skid Stealer, cybersecurity firm Phylum located them all to be copies of W4SP Stealer.
W4SP Stealer mainly features to siphon consumer info, which includes qualifications, cryptocurrency wallets, Discord tokens, and other data files of desire. It can be developed and revealed by an actor who goes by the aliases BillyV3, BillyTheGoat, and billythegoat356.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“For some cause, every single deployment appears to have simply experimented with to do a find/change of the W4SP references in trade for some other seemingly arbitrary name,” the scientists mentioned in a report posted earlier this 7 days.

The 16 rogue modules are as follows: modulesecurity, informmodule, chazz, randomtime, proxygeneratorbil, easycordey, easycordeyy, tomproxies, sys-ej, py4sync, infosys, sysuptoer, nowsys, upamonkws, captchaboy, and proxybooster.
The marketing campaign distributing W4SP Stealer gained traction close to October 2022, despite the fact that indications are that it may perhaps have started as far again as August 25, 2022. Considering the fact that then dozens of extra bogus deals that contains W4SP Stealer have been revealed on PyPI by the persistent threat actors.
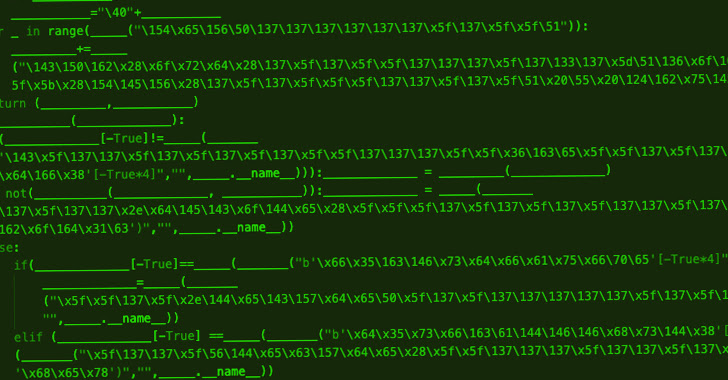
The most recent iteration of the exercise, for what it’s well worth, makes no obvious to conceal its nefarious intentions, except in the situation of chazz, which leverages the bundle to obtain obfuscated Leaf $tealer malware hosted on the klgrth[.]io paste provider.
It’s really worth noting that previous versions of the attack chains have also been spotted fetching upcoming-stage Python code directly from a general public GitHub repository that then drops the credential stealer.
The surge in new copycat variants dovetails with GitHub’s takedown of the repository that held the original W4SP Stealer source code, indicating that cybercriminals probably not affiliated with the procedure are also weaponizing the malware to attack PyPI users.
“Open up-source ecosystems this kind of as PyPI, NPM, and the like are massive quick targets for these kinds of actors to consider and deploy this form of malware on,” the scientists claimed. Their tries will only become far more recurrent, a lot more persistent, and most sophisticated.”
The program source chain security agency, which kept tabs on the risk actor’s Discord channel, further pointed out that a previously flagged package deal underneath the identify of pystyle was trojanized by BillyTheGoat to distribute the stealer.
The module has not only racked by hundreds of downloads each and every thirty day period, but also started off off as an innocuous utility in September 2021 to assist customers fashion console output. The malicious modifications have been launched in variations 2.1 and 2.2 introduced on October 28, 2022.
These two variations, which were being live on PyPI for about an hour right before they had been pulled, are alleged to have gotten 400 downloads, BillyTheGoat explained to Phylum in an “unsolicited correspondence.”
“Just simply because a offer is benign nowadays and has shown a background of staying benign for a long time does not imply it will continue being this way,” the scientists cautioned. “Threat actors have demonstrated huge endurance in making reputable offers, only to poison them with malware just after they have turn out to be adequately popular.”
Discovered this article fascinating? Observe us on Twitter and LinkedIn to go through more unique material we write-up.
Some elements of this short article are sourced from:
thehackernews.com

 TikTok’s Parent Company Admits Using the Platform’s Data to Track Journalists
TikTok’s Parent Company Admits Using the Platform’s Data to Track Journalists