Inadequately secured Linux SSH servers are staying specific by undesirable actors to put in port scanners and dictionary attack tools with the purpose of targeting other susceptible servers and co-opting them into a network to have out cryptocurrency mining and distributed denial-of-support (DDoS) attacks.
“Threat actors can also opt for to install only scanners and offer the breached IP and account credentials on the dark web,” the AhnLab Security Emergency Reaction Centre (ASEC) stated in a report on Tuesday.
In these attacks, adversaries consider to guess a server’s SSH qualifications by managing via a listing of frequently made use of combinations of usernames and passwords, a approach referred to as dictionary attack.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Should the brute-drive endeavor be profitable, it is followed by the danger actor deploying other malware, such as scanners, to scan for other inclined units on the internet.
Particularly, the scanner is made to search for devices exactly where port 22 — which is linked with the SSH support — is energetic and then repeats the method of staging a dictionary attack in order to set up malware, effectively propagating the an infection.

An additional notable part of the attack is the execution of instructions such as “grep -c ^processor /proc/cpuinfo” to determine the variety of CPU cores.
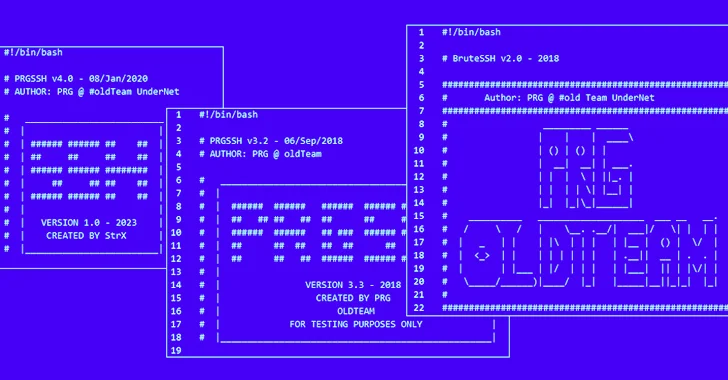
“These applications are thought to have been produced by PRG outdated Group, and every threat actor modifies them slightly in advance of making use of them in attacks,” ASEC reported, including there is proof of such malicious computer software being utilised as early as 2021.
To mitigate the risks linked with these attacks, it can be advisable that buyers count on passwords that are tricky to guess, periodically rotate them, and keep their units up-to-day.
The results appear as Kaspersky discovered that a novel multi-platform menace called NKAbuse is leveraging a decentralized, peer-to-peer network connectivity protocol recognised as NKN (shorter for New Kind of Network) as a communications channel for DDoS attacks.
Found this article intriguing? Follow us on Twitter and LinkedIn to read a lot more special content we post.
Some elements of this report are sourced from:
thehackernews.com

 Carbanak Banking Malware Resurfaces with New Ransomware Tactics
Carbanak Banking Malware Resurfaces with New Ransomware Tactics