Collaboration is a effective selling point for SaaS apps. Microsoft, Github, Miro, and many others market the collaborative mother nature of their software program applications that lets end users to do extra.
One-way links to files, repositories, and boards can be shared with any person, anywhere. This encourages teamwork that can help produce more powerful strategies and projects by encouraging collaboration among personnel dispersed throughout regions and departments.
At the exact same time, the openness of knowledge SaaS platforms can be problematic. A 2023 survey by the Cloud Security Alliance and Adaptive Defend uncovered that 58% of security incidents in excess of the final two a long time involved information leakage. Obviously, sharing is excellent, but details sharing ought to be place in test. Most SaaS applications have mechanisms to control sharing. These instruments are very efficient in ensuring that enterprise means are not open for display on the general public web. This short article will glance at a few prevalent facts leakage situations and advise most effective tactics for safe and sound sharing.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Learn how to see the files that are publicly shared from your SaaS
Turning Proprietary Code Community
GitHub repositories have a extensive historical past of leaking details. These facts leaks are ordinarily induced by person mistake, the place the developer unintentionally exposes private repositories or an admin adjustments permissions to facilitate collaboration.
GitHub leaks have impacted important models, such as X (formerly Twitter) whose proprietary code for its platform and internal resources leak onto the internet. GitHub leaks generally expose delicate secrets and techniques, like OAuth tokens, API keys, usernames and passwords, encryption keys, and security certificates.
When proprietary code and firm tricks leak, it can set business continuity at risk. Securing code within just GitHub repositories must be a leading precedence.
Stunning Hazards of Publicly Obtainable Calendars
On the floor, publicly shared calendars may well not feel to be significantly of a security risk. Calendars aren’t recognised for sensitive knowledge. In truth, they consist of a treasure trove of information that companies would not want slipping into the arms of cybercriminals.
Calendars consist of conference invitations with videoconference back links and passwords. Retaining that information and facts open up to the community could consequence in unwanted or malicious attendees at your conference. Calendars also incorporate agendas, presentations, and other delicate supplies.
The data from calendars can also be employed in phishing or social engineering attacks. For instance, if a menace actor with obtain to Alice’s calendar sees that she has a get in touch with with Bob at 3 o’clock, the menace actor can phone Bob though posing as Alice’s assistant and request that Bob email some delicate data in advance of the conference.
Collaborating with Exterior Company Suppliers
Even though SaaS applications simplify performing with companies and other service companies, these collaborations frequently involve associates who occur into the job for limited periods of time. Except if managed, the shared files and collaboration boards give anyone doing work on the undertaking access to the resources for all time.
Undertaking house owners will commonly create one consumer name for the agency or share important documents with any individual who has the url. This simplifies administration and might help save income in terms of licenses. However, the venture owner has ceded management above to who can entry and function on the supplies.
Anybody in just the exterior staff not only has access to proprietary venture files but they normally retain that obtain after they leave the enterprise if they recall the username and password. When methods are shared with anybody with a hyperlink, they can effortlessly ahead the link to their individual email account and access the files when they want.
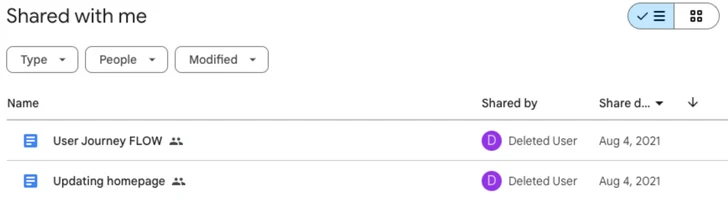 Determine 1: End users keep accessibility to shared Google Docs even soon after the employee who shared the documents has left the business
Determine 1: End users keep accessibility to shared Google Docs even soon after the employee who shared the documents has left the business
Uncover which configurations are exposing your info to the public.
Ideal Procedures for Risk-free File Sharing
Sharing methods is an essential factor of business operations. SaaS Security agency Adaptive Protect suggests providers comply with these ideal practices any time sharing data files with external users.
- Always share documents with unique customers, and call for some type of authentication.
- Never share by means of “any individual with the hyperlink.” When attainable, the admin need to disable this ability.
- When programs make it possible for, include an expiration day to the shared file.
- Increase an expiration date to file-sharing invitations.
- Remove share permissions from any general public document that is no for a longer period remaining utilised.
Moreover, businesses ought to look for a SaaS security resource that can discover publicly shared resources and flag them for remediation. This capacity will help companies understand the risk they are using with publicly shared documents and immediate them towards securing any data files at risk.
Find out how a Resource Stock can discover all publicly available resources.
Found this short article attention-grabbing? Comply with us on Twitter and LinkedIn to browse far more distinctive information we submit.
Some elements of this article are sourced from:
thehackernews.com

 Alert: New Vulnerabilities Discovered in QNAP and Kyocera Device Manager
Alert: New Vulnerabilities Discovered in QNAP and Kyocera Device Manager