Inadequately secured Microsoft SQL (MS SQL) servers are remaining specific in the U.S., European Union, and Latin American (LATAM) regions as portion of an ongoing fiscally inspired campaign to achieve original obtain.
“The analyzed menace campaign seems to stop in one particular of two ways, both the advertising of ‘access’ to the compromised host, or the top shipping of ransomware payloads,” Securonix scientists Den Iuzvyk, Tim Peck, and Oleg Kolesnikov claimed in a specialized report shared with The Hacker Information.
The campaign, joined to actors of Turkish origin, has been codenamed RE#TURGENCE by the cybersecurity company.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

Initial entry to the servers entails conducting brute-pressure attacks, followed by the use of xp_cmdshell configuration possibility to run shell instructions on the compromised host. This exercise mirrors that of a prior marketing campaign dubbed DB#JAMMER that arrived to light-weight in September 2023.
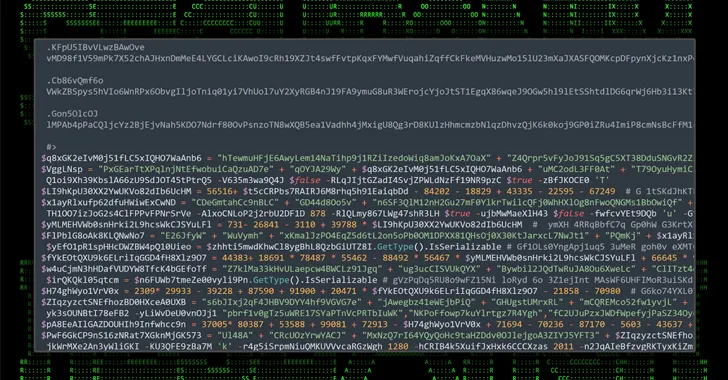
This stage paves the way for the retrieval of a PowerShell script from a remote server that’s liable for fetching an obfuscated Cobalt Strike beacon payload.
The put up-exploitation toolkit is then employed to down load the AnyDesk remote desktop application from a mounted network share for accessing the device and downloading more applications this kind of as Mimikatz to harvest credentials and Innovative Port Scanner to carry out reconnaissance.
Lateral motion is achieved by usually means of a genuine procedure administration utility known as PsExec, which can execute plans on distant Windows hosts.
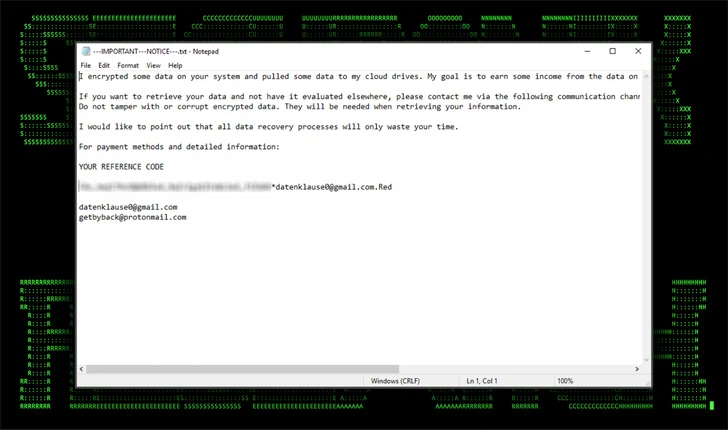
That attack chain, finally, culminates with the deployment of Mimic ransomware, a variant of which was also utilized in the DB#JAMMER marketing campaign.
“The indicators as properly as malicious TTPs utilised in the two strategies are absolutely distinct, so there is a very substantial probability these are two disparate campaigns,” Kolesnikov told The Hacker Information.

“More exclusively, even though the original infiltration strategies are equivalent, DB#JAMMER was marginally additional innovative and made use of tunneling. RE#TURGENCE is additional focused and tends to use authentic instruments and remote checking and administration, this kind of as AnyDesk, in an attempt to mix in with ordinary exercise.”
Securonix explained it uncovered an operational security (OPSEC) blunder created by the threat actors that permitted it to monitor clipboard activity owing to the actuality that the clipboard sharing attribute of AnyDesk was enabled.
This designed it possible to glean their Turkish origins and their on the net alias atseverse, which also corresponds to a profile on Steam and a Turkish hacking discussion board named SpyHack.
“Normally refrain from exposing critical servers instantly to the internet,” the scientists cautioned. “With the circumstance of RE#TURGENCE attackers have been straight able to brute force their way into the server from outside the primary network.”
Observed this report appealing? Stick to us on Twitter and LinkedIn to read a lot more special articles we submit.
Some pieces of this posting are sourced from:
thehackernews.com

 Why Public Links Expose Your SaaS Attack Surface
Why Public Links Expose Your SaaS Attack Surface