Cybersecurity researchers have in depth an current version of an state-of-the-art fingerprinting and redirection toolkit called WoofLocker that’s engineered to carry out tech support ripoffs.
The refined visitors redirection plan was first documented by Malwarebytes in January 2020, leveraging JavaScript embedded in compromised sites to accomplish anti-bot and web site visitors filtering checks to provide upcoming-phase JavaScript that redirects people to a browser locker (aka browlock).
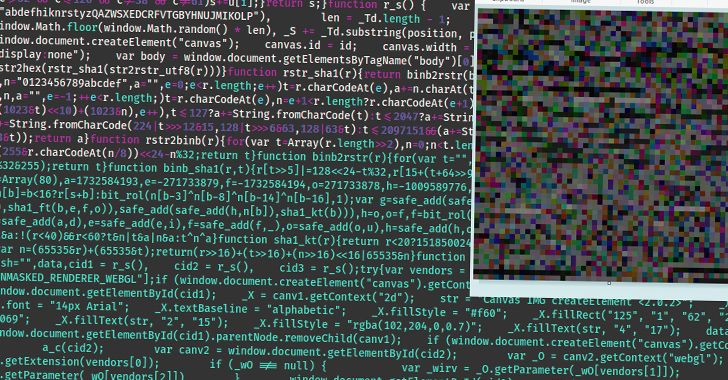
This redirection mechanism, in turn, would make use of steganographic tricks to conceal the JavaScript code in just a PNG impression that’s served only when the validation stage is effective. Really should a person be detected as a bot or not appealing site visitors, a decoy PNG file without the need of the destructive code is applied.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
WoofLocker is also known as 404Browlock due to the point that traveling to the browlock URL specifically with no the acceptable redirection or one particular-time session token effects in a 404 mistake web page.
The cybersecurity firm’s most current evaluation reveals that the campaign is continue to ongoing.

“The techniques and strategies are pretty identical, but the infrastructure is now more strong than just before to defeat likely takedown attempts,” Jérôme Segura, director of menace intelligence at Malwarebytes, claimed.
“It is just as difficult to reproduce and examine the redirection mechanism now as it was then, specifically in light-weight of new fingerprinting checks” to detect the presence of digital devices, selected browser extensions, and security applications.
A the greater part of the sites loading WoofLocker are adult internet sites, with the infrastructure employing hosting providers in Bulgaria and Ukraine that give the threat actors stronger protection against takedowns.
The most important target of browser lockers is to get focused victims to call for guidance to solve (non-existent) personal computer difficulties and get remote control around the computer to draft an bill that recommends impacted people to fork out for a security remedy to deal with the dilemma.
“This is handled by third-functions through fraudulent contact centers,” Segura pointed out back again in 2020. “The threat actor guiding the website traffic redirection and browlock will get compensated for each individual prosperous lead.”

The actual identity of the threat actor stays not known and there is proof preparations for the marketing campaign have been underway as early as 2017.
“Compared with other campaigns that count on purchasing ads and taking part in whack-a-mole with hosting suppliers and registrars, WoofLocker is a quite steady and low servicing business,” Segura said. “The web sites hosting the malicious code have been compromised for many years whilst the fingerprinting and browser locker infrastructure seems to be employing good registrar and hosting suppliers.”
The disclosure comes as the company detailed a new malvertising an infection chain that includes utilizing bogus ads on lookup engines to direct end users seeking for remote accessibility packages and scanners to booby-trapped web-sites that direct to the deployment of stealer malware.

What sets this marketing campaign aside is its capacity to fingerprint readers utilizing the WEBGL_debug_renderer_information API to get the victim’s graphics driver properties to type actual browsers from crawlers and virtual machines and exfiltrate the data to a distant server in get to ascertain the next system of motion.

“By utilizing superior filtering ahead of redirecting possible victims to malware, risk actors make certain that their destructive ads and infrastructure remain online lengthier,” Segura stated. “Not only does it make it far more tricky for defenders to establish and report this sort of gatherings, it also likely has an influence on takedown steps.”
The development also follows new study which identified that web-sites belonging to U.S. govt organizations, foremost universities, and experienced companies have been hijacked around the past five years and utilized to press fraud provides and promotions by means of “poison PDF” files uploaded to the portals.
A lot of of these ripoffs are aimed at children and endeavor to trick them into downloading applications, malware, or submitting personal information in trade for non-existent benefits in on the net gaming platforms this kind of as Fortnite and Roblox.
Located this short article intriguing? Follow us on Twitter and LinkedIn to read much more distinctive content material we post.
Some parts of this article are sourced from:
thehackernews.com

 New Juniper Junos OS Flaws Expose Devices to Remote Attacks – Patch Now
New Juniper Junos OS Flaws Expose Devices to Remote Attacks – Patch Now