An up to date version of an Android banking trojan referred to as Xenomorph has set its sights on much more than 35 economical institutions in the U.S.
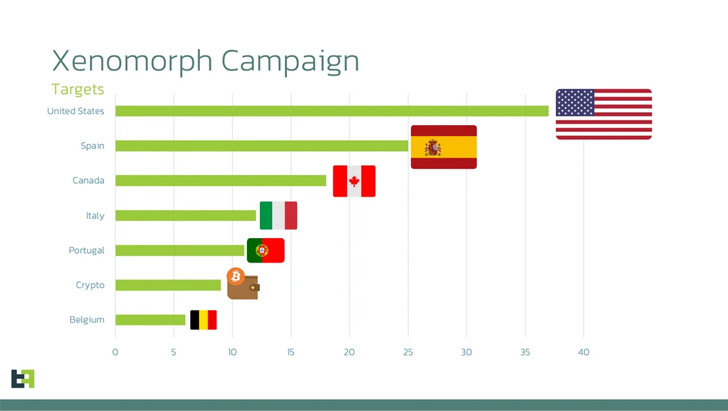
The campaign, according to Dutch security firm ThreatFabric, leverages phishing web internet pages that are made to entice victims into installing malicious Android applications that goal a broader list of applications than its predecessors. Some of the other specific prominent nations focused comprise Spain, Canada, Italy, and Belgium.
“This new list adds dozens of new overlays for institutions from the United States, Portugal, and several crypto wallets, pursuing a trend that has been constant amongst all banking malware family members in the last year,” the business stated in an assessment published Monday.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Xenomorph is a variant of yet another banker malware identified as Alien which 1st emerged in 2022. Afterwards that yr, the financial malware was propagated by means of a new dropper dubbed BugDrop, which bypassed security functions in Android 13.

A subsequent iteration noticed earlier this March arrived equipped with capabilities to conduct fraud using what’s acknowledged as the Automated Transfer Method (ATS).
The characteristic makes it possible for its operators, named Hadoken Security, to wholly seize regulate above the system by abusing Android’s accessibility privileges and illicitly transfer funds from the compromised gadget to an actor-managed account.
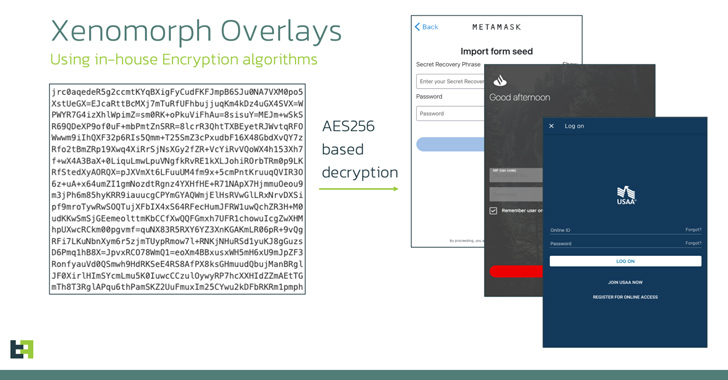
The malware also leverages overlay attacks to steal sensitive facts this sort of as credentials and credit score card numbers by displaying faux login screens on top rated of the qualified bank apps. The overlays are retrieved from a distant server in the type of a checklist of URLs.
In other terms, the ATS framework would make it achievable to routinely extract qualifications, access account balance information, initiate transactions, get MFA tokens from authenticator applications, and conduct fund transfers, all without the need of the need to have for any human intervention.
“Actors have set a good deal of exertion into modules that assist Samsung and Xiaomi gadgets,” the researchers stated. “This would make perception, thinking of that these two put together make up approximately 50% of the total Android industry share.”
Some of the new capabilities added to the most up-to-date variations of Xenomorph consist of an “antisleep” aspect that prevents the phone’s display screen from turning off by making an active force notification, an choice to simulate a easy touch at a specific display screen coordinate, and impersonate another application making use of a “mimic” element.
Approaching WEBINARFight AI with AI — Battling Cyber Threats with Subsequent-Gen AI Equipment
Ready to deal with new AI-driven cybersecurity difficulties? Be a part of our insightful webinar with Zscaler to address the escalating threat of generative AI in cybersecurity.
Supercharge Your Skills
As a way to bypass detection for extended intervals of time, the malware hides its icon from the residence display launcher on installation. The abuse of the accessibility solutions further more permits it to grant alone all the permissions it needs to run unimpeded on a compromised device.
Earlier versions of the banking trojan have masqueraded as reputable apps and utilities on the Google Participate in Retail outlet. But the most up-to-date attack wave observed in mid-August 2023 switches up the modus operandi by distributing the applications through counterfeit sites providing Chrome browser updates.
In a indication that the danger actors are focusing on several running devices, the investigation discovered that the payload hosting infrastructure is also remaining utilized to serve Windows stealer malware these kinds of as Lumma C2 and RisePro, as properly as a malware loader referred to as Non-public Loader.
“Xenomorph maintains its position as an incredibly perilous Android banking malware, that includes a incredibly flexible and strong ATS motor, with a number of modules previously created, with the concept of supporting several manufacturer’s equipment,” ThreatFabric explained.
Discovered this write-up attention-grabbing? Follow us on Twitter and LinkedIn to examine additional distinctive material we submit.
Some sections of this write-up are sourced from:
thehackernews.com

 Threat Report: The High Tech Industry Targeted the Most with 46% of NLX-Tagged Attack Traffic
Threat Report: The High Tech Industry Targeted the Most with 46% of NLX-Tagged Attack Traffic