Risk hunters weigh in on how the enterprise of ransomware, the complicated associations in between cybercriminals, and how they work together and hawk their wares on the Dark Web.
Ransomware is not just a type of malware – it’s also at the heart of a advanced, flourishing underground economy that has all the conventions of reputable commerce.
It is a neighborhood made up of big malware developers, affiliates and channel partners, and people that present adjacent companies, this kind of as marketing network entry. Operators even have their possess publicity arms that place out press releases and retain their “brands,” and they have shopper-support operations.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
They located that the normal financial system of ransomware is perfectly-produced and advanced, with “several actors providing expert services to 1 another,” according to research from Kaspersky. For instance, botmasters offer you obtain to presently-compromised units software builders improve the malware and preliminary entry brokers specialize in furnishing network obtain via backdoors or security vulnerability exploits for points like Remote Desktop Protocol (RDP).
This article is dependent on a a lot more in-depth piece, out there in the free Threatpost Insider E book, entitled “2021: The Evolution of Ransomware.” Down load it today for much much more on the ransomware underground economic climate!
“This accessibility can be offered in an auction or as a mounted price, starting off as very low as $50,” Kaspersky scientists explained, in a modern submitting. “The attackers who produce the preliminary compromise, much more often than not, are possibly botnet entrepreneurs who operate on large and vast-achieving strategies and sell accessibility to the target equipment in bulk, or hackers who are consistently on the lookout for publicly disclosed software program vulnerabilities to exploit as shortly as they are declared and just before a patch is used.”
RaaS Affiliate marketers Are Very carefully Vetted
At the middle of the scene is the simple fact that ransomware operators normally undertake affiliate marketers, to whom they present ransomware-as-a-assistance (RaaS) offerings. Affiliates can be viewed as the channel companions of the underground, dependable for ransomware distribution to conclusion victims. They commonly pocket concerning 60 and 80 percent of the ransom, with the rest heading into the operators and authors’ coffers.
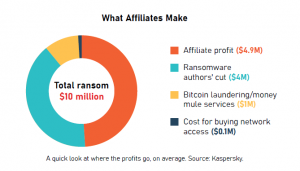
Click to enlarge.
“These gangs operate like legitimate businesses: They have client support and IT support, and will do what they can to improve their brand reputation,” according to experts at Intel 471, in a collaborative job interview. “So, your most well-liked variants are individuals that end result in larger payouts and take care of the criminal’s asks as soon as they are brought into an affiliate software.”
RaaS functions carefully pick their affiliate partners, with prerequisites that differ from technological know-how to the potential to prove they have roots in Russia or the former Soviet states.
“Well-recognized ransomware gangs are recognised to be relatively picky,” according to Intel 471. “The basic necessity for a applicant willing to enroll into any higher-profile RaaS affiliate application is commonly to reveal availability of compromised accesses or opportunity resources of such accesses to profitable company networks.”
In a 2020 posting in the Russian-language Exploit forum, MedusaLocker posted its needs to potential affiliate marketers. These included “practical experience with ransomware, self-assured person of Cobalt Strike, equipped to escalate regional administrator and area administrator privileges, functioning information of backup programs and comprehending of OpSec.”
Meanwhile, in purchase to avert infiltration of affiliate courses by western legislation-enforcement expert services and by cyber-risk researchers, some RaaS gangs carry out supplemental safety measures, which consist of vouching by current users, a necessity for a native command of the Russian language, or vetting of area and cultural know-how pertaining to Russia and ex-USSR nations around the world, Intel scientists added.

Down load “The Evolution of Ransomware” to achieve important insights on emerging traits amidst promptly rising attack volumes. Simply click above to hone your defense intelligence!
For example, a publishing in the Exploit cybercrime forum by the REvil ransomware gang in slide 2020 famous, “No question, in the FBI and other distinctive expert services, there are people today who converse Russian completely, but their amount is undoubtedly not the just one indigenous speakers have. Examine these individuals by inquiring them issues about the heritage of Ukraine, Belarus, Kazakhstan or Russia, which cannot be googled. Authentic proverbs, expressions, and many others.”
This difficult vetting processes arises from the reality that criminals who make cash illegally from on the internet fraud work inside tight-knit circles by necessity, Dustin Warren, senior security researcher at SpyCloud, explained to Threatpost.
“It is not unusual for criminals to be vouched into these trusted circles where by they do the job with other criminals taking part in different styles of fraud,” he explained. “Reputation is almost everything to these criminals, and they get the job done for a extremely lengthy time to build this standing so that they can get into these circles where by dollars is remaining created.”
Competing for Marketplace Share
In the cybercriminal underground, ransomware samples and builders are likely for anywhere among $300 to $4,000, with ransomware-as-a-service rentals costing $120 to $1,900 for every year. That is in accordance to a latest evaluation by Kaspersky of the 3 principal underground community forums where ransomware is circulated.
In some instances, this has led to a bit of an arms race to establish the most ground breaking, sophisticated or stealthiest code for the market place.
“Ransomware is usually resold, and malware suppliers undoubtedly compete for current market share,” Warren stated. “There are often improvements in the is effective, specially about evading antivirus protections and other controls that might be in the way, to getting able to encrypt files the swiftest. They financial institution on their targets getting complicated guidelines about how they patch their methods and how frequently.”

Down load “The Evolution of Ransomware” to acquire beneficial insights on emerging developments amidst swiftly escalating attack volumes. Simply click over to hone your protection intelligence!
Some strains and companies are unequivocally more popular than others, just simply because they do the job superior than some others, he extra. But, the possibility that a danger actor finally decides to purchase and use often is dependent on other aspects as nicely, these types of as the standing of the writer of the malware or operator of the RaaS procedure, cost, geolocation, how simple the vendor is to function with or the concentrate on victim’s attack landscape.
Backlash in opposition to operators can at times materialize. For instance, it was lately revealed that cybercriminals who have labored as affiliate marketers with ransomware group DarkSide, accountable for the Colonial Pipeline attack, are acquiring a challenging time acquiring compensated for their work now that the team has experienced its operations interrupted so, they’re turning to admins of the group’s Dark Web felony forum to form issues out in what researchers simply call a “shady variation of the People’s Court docket.”
Also, when a criminal application developer builds a new strand of ransomware, the human being will frequently very first share the challenge for free with a pick out number of other trusted neighborhood customers.
“This free duplicate of the malware is referred to as a ‘vouched’ duplicate, and its intent is to enable respected actors to supply comments and validate the new piece of malware,” Warren explained. “Then, immediately after the malware has been proficiently peer reviewed and tweaked accordingly, the developer will advertise it publicly, on a forum for instance.”
People today obtain ransomware computer software based mostly off of selling price as well as their individual use circumstances, according to Warren: “As these kinds of, great ransomware strains eventually get a subsequent actors will usually retain up with and acquire new versions of the exact ransomware job as they are produced (AZOrult is a very good case in point of this).”
Enterprise is booming on the cyber-underground. But that could adjust a coalition of 60 world entities (including the U.S. Department of Justice) has proposed a sweeping plan to create a ransomware activity pressure, to hunt down and disrupt ransomware gangs by going right after their economical operations.
And, in the wake of the Colonial Pipeline hack, underground boards them selves are wanting to choose some of the warmth off by removing RaaS ads and the like.
Philip Reiner, the CEO of IST and the executive director of the Ransomware Undertaking Force, warned that one thing has to give.
“The price of ransom compensated by organizations has nearly doubled in the past 12 months, and is generating new risks, a lot of that go significantly further than monetary hurt,” he said. “In the previous 12 months on your own, we have noticed ransomware attacks hold off lifesaving medical therapy, destabilize critical infrastructure and threaten our national security.”
Download our distinctive Totally free Threatpost Insider Book, “2021: The Evolution of Ransomware,” to assistance hone your cyber-protection approaches towards this increasing scourge. We go further than the standing quo to uncover what’s future for ransomware and the connected rising threats. Get the entire tale and Obtain the Book now – on us!
Some pieces of this article are sourced from:
threatpost.com


 Intel SGX in the real world
Intel SGX in the real world