A group of scientists has unveiled facts of a new vulnerability affecting Intel CPUs that allows attackers to attain encryption keys and other solution details from the processors.
Dubbed ÆPIC Leak, the weakness is the initially-of-its-variety to architecturally disclose delicate info in a fashion which is akin to an “uninitialized memory go through in the CPU alone.”
“In contrast to transient execution attacks like Meltdown and Spectre, ÆPIC Leak is an architectural bug: the delicate knowledge gets specifically disclosed with out relying on any (noisy) facet channel,” the academics reported.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The review was performed by researchers from the Sapienza University of Rome, the Graz College of Technology, Amazon Web Services, and the CISPA Helmholtz Heart for Information Security.
The vulnerability (CVE-2022-21233, CVSS rating: 6.), which has an effect on CPUs with Sunny Go over microarchitecture, is rooted in a element termed Sophisticated Programmable Interrupt Controller (APIC), which delivers a mechanism to deal with and route components interrupt indicators in a scalable way.

“The scan of the I/O deal with space on Intel CPUs dependent on the Sunny Cove microarchitecture exposed that the memory-mapped registers of the area Innovative Programmable Interrupt Controller (APIC) are not adequately initialized,” the scientists observed.
“As a final result, architecturally examining these registers returns stale data from the microarchitecture. Any info transferred between the L2 and the final-degree cache can be read via these registers.”
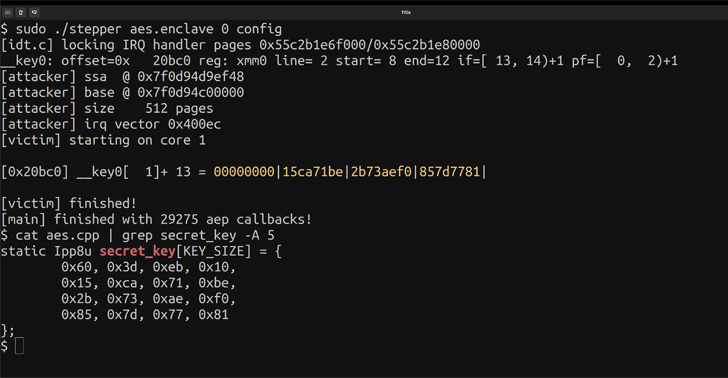
ÆPIC Leak exclusively targets programs employing Intel’s dependable execution surroundings (TEE) regarded as Program Guard eXtensions (SGX), triggering the leakage of AES and RSA keys from safe enclaves that operate on the exact bodily CPU core with a results level of 94% and 74% respectively.
“By shielding picked code and info from modification, builders can partition their software into hardened enclaves or dependable execution modules to assist improve software security,” Intel points out about the security assurances provided by SGX.
The flaw, set basically, breaks the aforementioned assures, enabling an attacker with permissions to execute privileged native code on a concentrate on machine to extract the non-public keys, and worse defeat attestation, a cornerstone of the security primitives made use of in SGX to guarantee the integrity of code and data.
In reaction to the results, Intel has produced firmware updates, whilst describing the issue as a medium-severity vulnerability related to incorrect isolation of shared sources, leading to facts disclosure by way of local entry.

It’s also worth noting that Intel has considering the fact that deprecated assist for SGX for its consumer CPUs, what with a litany of attack approaches plaguing the technology, like SGX-ROP, MicroScope, Plundervolt, Load Worth Injection, SGAxe, and VoltPillager.
SQUIP Aspect Channel Attack Affect AMD CPUs
The improvement arrives as researchers shown what is actually the 1st-at any time facet channel attack (CVE-2021-46778) on scheduler queues impacting AMD Zen 1, Zen 2, and Zen 3 microarchitectures that could be abused by an adversary to recuperate RSA keys.
The attack, codenamed SQUIP (brief for Scheduler Queue Use by way of Interference Probing), involves measuring the contention amount on scheduler queues to potentially glean delicate details.
No security updates have been launched to patch the line of attack, but the chipmaker has suggested that “software builders hire current ideal practices, which include regular-time algorithms and keeping away from top secret-dependent control flows where by acceptable.”
Found this post interesting? Comply with THN on Facebook, Twitter and LinkedIn to go through additional unique articles we article.
Some sections of this article are sourced from:
thehackernews.com


 #DEFCON: Electrovolt Exploits Against Electron Desktop Apps Exposed
#DEFCON: Electrovolt Exploits Against Electron Desktop Apps Exposed