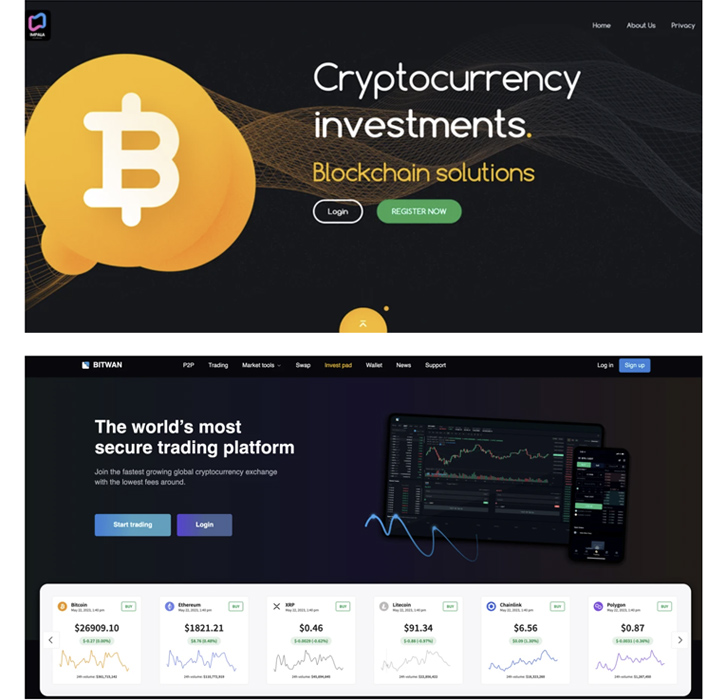
A earlier undetected cryptocurrency fraud has leveraged a constellation of about 1,000 fraudulent internet sites to ensnare customers into a bogus rewards scheme due to the fact at minimum January 2021.
“This large marketing campaign has most likely resulted in 1000’s of folks getting scammed throughout the world,” Development Micro researchers explained in a report published past 7 days, linking it to a Russian-talking menace actor named “Impulse Workforce.”
“The scam works by using an state-of-the-art payment fraud that consists of tricking victims into believing that they’ve gained a specific volume of cryptocurrency. Even so, to get their rewards, the victims would will need to pay out a compact sum to open up an account on their internet site.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The compromise chain starts off with a direct concept propagated by way of Twitter to entice potential targets into going to the decoy web site. The account responsible for sending the messages has because been closed.
The concept urges recipients to signal up for an account on the web page and apply a promo code specified in the message to acquire a cryptocurrency reward amounting to .78632 bitcoin (about $20,300).
But at the time an account is set up on the phony system, customers are requested to activate an account by making a minimum deposit worth .01 bitcoin (about $258) to ensure their identification and full the withdrawal.

“When comparatively sizable, the sum important to activate the account pales in comparison to what end users would get in return,” the researchers pointed out. “Nonetheless, as predicted, recipients under no circumstances get anything in return when they spend the activation quantity.”
A general public Telegram channel that data each payment produced by the victims shows that the illicit transactions have yielded the actors a little over $5 million involving December 24, 2022, and March 8, 2023.
Craze Micro claimed it unearthed hundreds of domains associated to this fraud, with some of them staying active as significantly back as 2016. All the fake websites belong to an affiliate “rip-off crypto venture” codenamed Impulse that is been marketed on Russian cybercrime boards considering the fact that February 2021.
Like ransomware-as-a-services (RaaS) functions, the enterprise requires affiliate actors to fork out a price to be part of the software and share a percentage of the earnings with the initial authors.
To lend the procedure a veneer of legitimacy, the threat actors are thought to have develop a lookalike edition of a identified anti-fraud instrument identified as ScamDoc, which assigns a belief rating for different web sites, in a plausible attempt to move off the sketchy crypto providers as trustworthy.
Development Micro said it also stumbled upon personal messages, on the net videos, and adverts on other social networks this kind of as TikTok and Mastodon, indicating that the affiliate marketers are working with a large vary of solutions to advertise the fraudulent action.
“The threat actor streamlines operations for its affiliate marketers by offering hosting and infrastructure so they can run these fraud sites on their personal,” the scientists claimed. “Affiliates are then capable to concentrate on other elements of the procedure, this kind of as operating their personal advertising and marketing strategies.”
Future WEBINAR🔐 Mastering API Security: Knowledge Your Real Attack Area
Uncover the untapped vulnerabilities in your API ecosystem and get proactive steps towards ironclad security. Be part of our insightful webinar!
Sign up for the Session.wn-button,.wn-label,.wn-label:just afterdisplay:inline-block.check out_two_webinarmargin:20px 10px 30px 0background:#f9fbffcolor:#160755padding: 5%border:2px solid #d9deffborder-radius:10pxtext-align:leftbox-shadow:10px 10px #e2ebff-webkit-border-prime-still left-radius:25px-moz-border-radius-topleft:25px-webkit-border-bottom-suitable-radius:25px-moz-border-radius-bottomright:25px.wn-labelfont-dimension:13pxmargin:20px 0font-bodyweight:600letter-spacing:.6pxcolor:#596cec.wn-label:right afterwidth:50pxheight:6pxcontent:”border-major:2px stable #d9deffmargin: 8px.wn-titlefont-dimension:21pxpadding:10px 0font-body weight:900text-align:leftline-peak:33px.wn-descriptiontextual content-align:leftfont-size:15.6pxline-top:26pxmargin:5px !importantcolor:#4e6a8d.wn-buttonpadding:6px 12pxborder-radius:5pxbackground-coloration:#4469f5font-dimension:15pxcolor:#fff!importantborder:0line-height:inherittext-decoration:none!importantcursor:pointermargin:15px 20pxfloat:leftfont-pounds:500letter-spacing:.2px
The conclusions appear weeks soon after Akamai took the wraps off a renewed Romanian cryptojacking marketing campaign named Diicot (formerly Mexals) that employs a Golang-dependent Secure Shell (SSH) worm module and a new LAN spreader for propagation.
Then last month, Elastic Security Labs thorough the use of an open-resource rootkit known as r77 to deploy the XMRig cryptocurrency miner in a number of Asian nations around the world.
“r77’s key intent is to disguise the existence of other software on a system by hooking vital Windows APIs, building it an ideal resource for cybercriminals seeking to carry out stealthy attacks,” the scientists mentioned.
“By leveraging the r77 rootkit, the authors of the malicious crypto miner were capable to evade detection and continue on their marketing campaign undetected.”
It can be truly worth pointing out that the r77 rootkit is also incorporated in SeroXen, a nascent variant of the Quasar remote administration tool that is remaining bought for only $30 for a monthly license or $60 for a lifetime bundle.
Located this report fascinating? Adhere to us on Twitter and LinkedIn to read much more unique content we submit.
Some elements of this posting are sourced from:
thehackernews.com


 Critical RCE Flaw Discovered in Fortinet FortiGate Firewalls – Patch Now!
Critical RCE Flaw Discovered in Fortinet FortiGate Firewalls – Patch Now!