A Chinese-speaking phishing gang dubbed PostalFurious has been connected to a new SMS marketing campaign that’s targeting customers in the U.A.E. by masquerading as postal companies and toll operators, per Group-IB.
The fraudulent scheme involves sending customers bogus textual content messages asking them to pay out a car or truck trip cost to keep away from additional fines. The messages also contain a shortened URL to conceal the genuine phishing url.
Clicking on the website link directs the unsuspecting recipients to a phony landing web site that’s intended to capture payment qualifications and own information. The campaign is estimated to be active as of April 15, 2023.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

“The URLs from the texts lead to faux branded payment web pages that check with for particular information, such as title, tackle, and credit rating card facts,” Team-IB claimed. “The phishing web pages correct the formal title and brand of the impersonated postal service provider.”
The exact scale of the attacks is at this time mysterious. What is actually known is that the text messages ended up despatched from phone quantities registered in Malaysia and Thailand, as effectively as via email addresses via the Apple iMessage services.
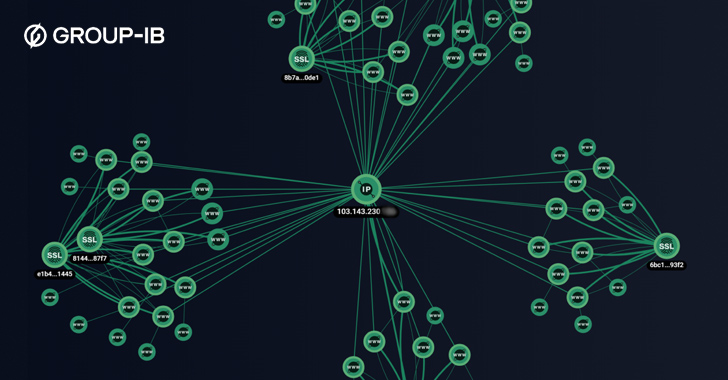
In a bid to continue to be undetected, the phishing inbound links are geofenced these types of that the pages can only be accessed from U.A.E.-dependent IP addresses. The risk actors have also been noticed registering new phishing domains every day to extend their access.
In accordance to the Singapore-primarily based cybersecurity organization, a second near-equivalent marketing campaign noticed on April 29, 2023, mimicked a U.A.E. postal operator.
Upcoming WEBINAR 🔐 Mastering API Security: Being familiar with Your Genuine Attack Surface area
Find the untapped vulnerabilities in your API ecosystem and just take proactive steps towards ironclad security. Join our insightful webinar!
Sign up for the Session.advertisement-button,.advertisement-label,.advert-label:immediately afterscreen:inline-block.advertisement_two_webinarmargin:20px 10px 30px 0background:#f9fbffcolor:#160755padding: 5%border:2px strong #d9deffborder-radius:10pxtext-align:leftbox-shadow:10px 10px #e2ebff-webkit-border-major-remaining-radius:25px-moz-border-radius-topleft:25px-webkit-border-bottom-suitable-radius:25px-moz-border-radius-bottomright:25px.ad-labelfont-measurement:13pxmargin:20px 0font-pounds:600letter-spacing:.6pxcolor:#596cec.advert-label:just afterwidth:50pxheight:6pxcontent:”border-top:2px strong #d9deffmargin: 8px.advert-titlefont-size:21pxpadding:10px 0font-body weight:900textual content-align:leftline-peak:33px.ad-descriptiontextual content-align:leftfont-dimensions:15.6pxline-top:26pxmargin:5px !importantcolor:#4e6a8d.advertisement-buttonpadding:6px 12pxborder-radius:5pxbackground-color:#4469f5font-measurement:15pxcolor:#fff!importantborder:0line-height:inherittext-decoration:none!importantcursor:pointermargin:15px 20pxfloat:leftfont-fat:500letter-spacing:.2px
The smishing activity marks an growth of the danger actor’s attempts considering the fact that at minimum 2021, when it commenced focusing on consumers in the Asia-Pacific region. Team-IB stated PostalFurious functions show the “transnational mother nature of structured cybercrime.”
To steer clear of falling prey to these kinds of cons, it’s proposed to observe careful clicking practices when it comes to back links and attachments, keep computer software up-to-day, and ensure solid electronic hygiene routines.
The improvement comes on the heels of a identical postal-themed phishing marketing campaign dubbed Operation Purple Deer that has been found out targeting various Israeli organizations to distribute a distant access trojan referred to as AsyncRAT. The attacks have been pinned on a danger actor codenamed Aggah.
Located this post appealing? Adhere to us on Twitter and LinkedIn to read through extra exclusive information we write-up.
Some elements of this report are sourced from:
thehackernews.com

 Zyxel Firewalls Under Attack! Urgent Patching Required
Zyxel Firewalls Under Attack! Urgent Patching Required