Tax-spending persons in Mexico and Chile have been targeted by a Mexico-primarily based cybercrime team that goes by the title Fenix to breach focused networks and steal precious facts.
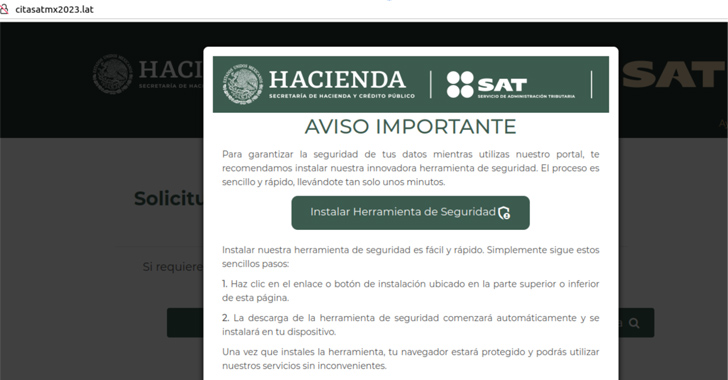
A essential hallmark of the procedure entails cloning formal portals of the Servicio de Administración Tributaria (SAT) in Mexico and the Servicio de Impuestos Internos (SII) in Chile and redirecting possible victims to those people internet sites.
“These bogus web sites prompt end users to obtain a supposed security tool, boasting it will boost their portal navigation protection,” Metabase Q security scientists Gerardo Corona and Julio Vidal stated in a modern examination.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“However, unbeknownst to the victims, this obtain truly installs the first stage of malware, ultimately enabling the theft of sensitive information these kinds of as qualifications.”
The goal of Fenix, in accordance to the Latin The us-concentrated cybersecurity firm, is to act as an initial accessibility broker and get a foothold into diverse firms in the region, and market the obtain to ransomware affiliate marketers for further more monetization.
Evidence gathered so significantly factors to the menace actor orchestrating phishing strategies coinciding with governing administration routines all through the year because at minimum the fourth quarter of 2022.
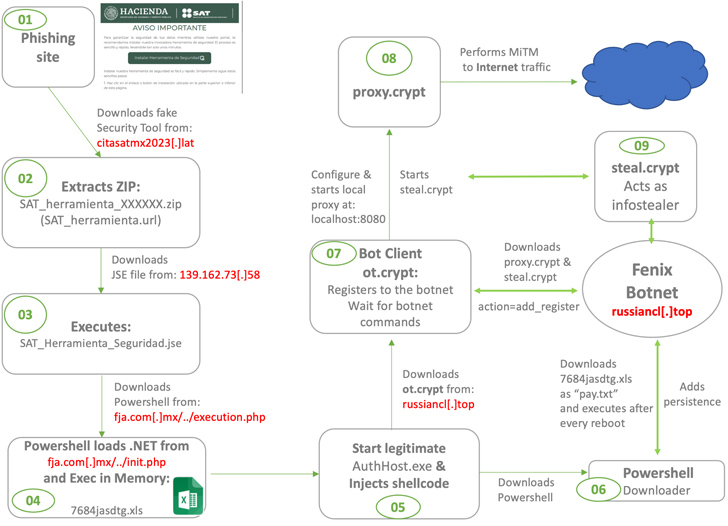
The mechanics of the marketing campaign proceeds as a result: Website visitors landing on the impersonated web-sites are urged to down load application that supposedly safeguards their facts while browsing the portal. Alternatively, people are lured by using phishing sites established up to download legitimate apps like AnyDesk.
“[Fenix] compromises weak sites using vulnerable WordPress engines and also results in new domains to start phishing campaigns,” the scientists reported, adding the team “creates typosquatting domains comparable to known applications like AnyDesk, WhatsApp, and so on.”
Upcoming WEBINARShield Versus Insider Threats: Learn SaaS Security Posture Administration
Concerned about insider threats? We have acquired you protected! Sign up for this webinar to check out realistic techniques and the strategies of proactive security with SaaS Security Posture Administration.
Be part of Today
But in truth, the ZIP file that contains the purported software package is employed as a springboard to activate an an infection sequence that potential customers to the execution of an obfuscated PowerShell script, which, in turn, loads and runs a .NET binary, after which the information “Ahora se encuentra protegido” (indicating “Now you are guarded” in Spanish) is displayed to hold up the ruse.
The .NET executable subsequently paves the way for creating persistence on the compromised host and deploying a botnet malware that’s able of running instructions been given from a distant server, loading a stealer module that exfiltrates qualifications saved in web browsers and crypto wallets, and finally deleting alone.
“We are viewing new destructive groups staying established in LATAM to deliver first obtain to ransomware gangs,” the scientists concluded. “These regional actors are not newbie and will maximize their complex abilities and as a result far more tricky to observe, detect and eradicate, it is important to foresee their actions.”
Discovered this article appealing? Follow us on Twitter and LinkedIn to examine extra special content material we article.
Some components of this short article are sourced from:
thehackernews.com

 New AI Tool ‘FraudGPT’ Emerges, Tailored for Sophisticated Attacks
New AI Tool ‘FraudGPT’ Emerges, Tailored for Sophisticated Attacks