A down load manager web site served Linux end users malware that stealthily stole passwords and other delicate information and facts for much more than 3 decades as element of a source chain attack.
The modus operandi entailed creating a reverse shell to an actor-managed server and setting up a Bash stealer on the compromised program. The marketing campaign, which took area in between 2020 and 2022, is no lengthier energetic.
“This stealer collects data this sort of as process data, searching history, saved passwords, cryptocurrency wallet data files, as nicely as credentials for cloud products and services (AWS, Google Cloud, Oracle Cloud Infrastructure, Azure),” Kaspersky researchers Georgy Kucherin and Leonid Bezvershenko mentioned.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
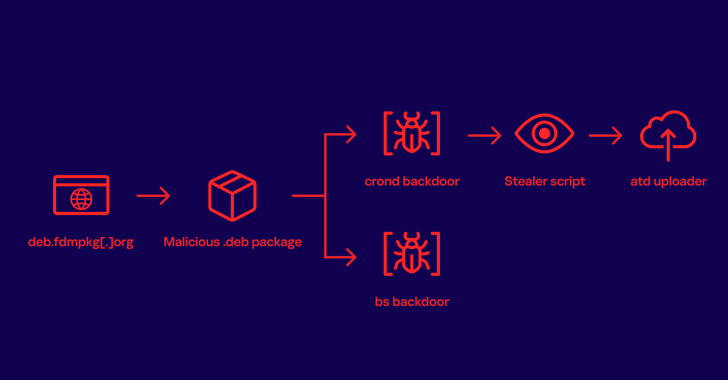
The web page in dilemma is freedownloadmanager[.]org, which, in accordance to the Russian cybersecurity agency, provides a authentic Linux application referred to as “Absolutely free Obtain Manager,” but starting up in January 2020, started redirecting some customers who tried to download it to a further domain deb.fdmpkg[.]org that served a booby-trapped Debian deal.
It can be suspected that the malware authors engineered the attack based on certain predefined filtering standards (say, a electronic fingerprint of the program) to selectively direct probable victims to the malicious variation. The rogue redirects ended in 2022 for inexplicable good reasons.

The Debian package deal contains a publish-set up script that is executed upon its installation to drop two ELF documents, /var/tmp/bs and a DNS-primarily based backdoor (/var/tmp/crond) that launches a reverse shell to a command-and-regulate (C2) server, which is been given in response to a DNS request to one particular of the 4 domains –
- 2c9bf1811ff428ef9ec999cc7544b43950947b0f.u.fdmpkg[.]org
- c6d76b1748b67fbc21ab493281dd1c7a558e3047.u.fdmpkg[.]org
- 0727bedf5c1f85f58337798a63812aa986448473.u.fdmpkg[.]org
- c3a05f0dac05669765800471abc1fdaba15e3360.u.fdmpkg[.]org
“The conversation protocol is, based on the connection variety, possibly SSL or TCP,” the researchers stated. “In the situation of SSL, the crond backdoor launches the /var/tmp/bs executable and delegates all even more communications to it. Or else, the reverse shell is created by the crond backdoor by itself.”
The supreme aim of the attack is to deploy a stealer malware and harvest sensitive knowledge from the procedure. The selection information is then uploaded to the attacker’s server making use of an uploader binary downloaded from the C2 server.
crond, Kaspersky reported, is a variant of a backdoor identified as Bew that has been in circulation since 2013, though an early version of the Bash stealer malware was earlier documented by Yoroi in June 2019.
Impending WEBINARIdentity is the New Endpoint: Mastering SaaS Security in the Modern Age
Dive deep into the long term of SaaS security with Maor Bin, CEO of Adaptive Shield. Explore why identification is the new endpoint. Protected your spot now.
Supercharge Your Skills
It really is not right away apparent how the compromise really took put and what the conclude plans of the marketing campaign were. What is actually apparent is that not absolutely everyone who downloaded the program received the rogue offer, enabling it to evade detection for decades.
“Even though the campaign is currently inactive, this situation of Totally free Down load Supervisor demonstrates that it can be quite complicated to detect ongoing cyberattacks on Linux devices with the bare eye,” the researchers explained.
“Consequently, it is crucial that Linux machines, both equally desktop and server, are equipped with reliable and successful security options.”
Observed this report attention-grabbing? Adhere to us on Twitter and LinkedIn to study far more exclusive information we publish.
Some components of this write-up are sourced from:
thehackernews.com

 Avoid These 5 IT Offboarding Pitfalls
Avoid These 5 IT Offboarding Pitfalls