Destructive actors are deploying a beforehand undiscovered binary, an Internet Info Companies (IIS) webserver module dubbed “Owowa,” on Microsoft Exchange Outlook Web Accessibility servers with the goal of thieving qualifications and enabling distant command execution.
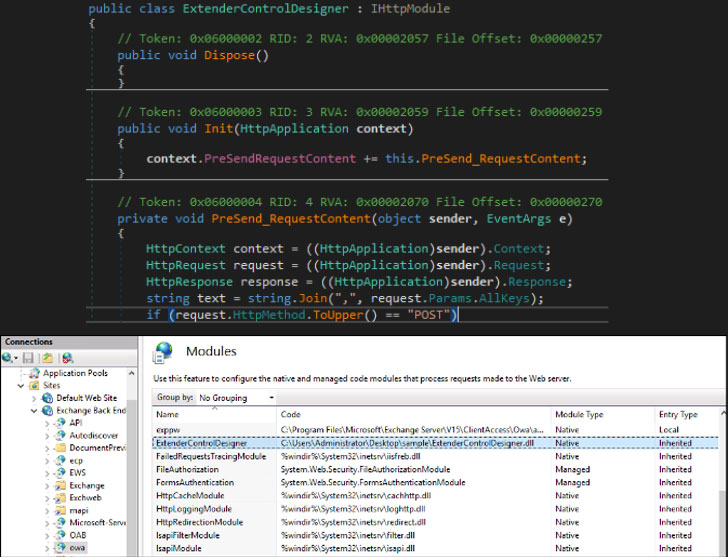
“Owowa is a C#-developed .NET v4. assembly that is supposed to be loaded as a module in just an IIS web server that also exposes Exchange’s Outlook Web Accessibility (OWA),” Kaspersky researchers Paul Rascagneres and Pierre Delcher claimed. “When loaded this way, Owowa will steal credentials that are entered by any person in the OWA login web site, and will make it possible for a remote operator to run commands on the underlying server.”
The concept that a rogue IIS module can be fashioned as a backdoor is not new. In August 2021, Slovak cybersecurity organization ESET’s review of the IIS landscape uncovered as numerous as 14 malware households that ended up made as indigenous IIS modules in an attempt to intercept HTTP traffic and remotely commandeer the compromised desktops.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

As a persistent element on the compromised procedure, Owawa is engineered to capture the qualifications of customers who are successfully authenticated on the OWA authentication web web page. Exploitation can then be accomplished by sending “seemingly innocuous requests” to the uncovered web providers by entering precisely crafted commands inside the username and password fields in the OWA authentication page of a compromised server.
Specifically, if the OWA username is “jFuLIXpzRdateYHoVwMlfc,” Owawa responds again with the encrypted qualifications. If the username, on the other hand, is “dEUM3jZXaDiob8BrqSy2PQO1”, the PowerShell command typed in the OWA password discipline is executed, the success of which are despatched again to the attacker.
The Russian security business reported it detected a cluster of targets with compromised servers positioned in Malaysia, Mongolia, Indonesia, and the Philippines that mainly belong to government corporations, with the exception of a person server that is hooked up to a government-owned transportation firm. That stated, further businesses in Europe are believed to have been victimized by the actor as well.
Though no inbound links have been unearthed among the Owowa operators and other publicly documented hacking groups, a username “S3crt” (go through “solution”) that was uncovered embedded in the supply code of the discovered samples has yielded more malware executables that are very likely the do the job of the same developer. Main between them are a selection of binaries developed to execute an embedded shellcode, load subsequent-stage malware retrieved from a remote server, and set off the execution of Cobalt Strike payloads.
Kaspersky’s Worldwide Study and Analysis Crew (Good) also reported it recognized an account with the identical username on Keybase, in which the individual has shared offensive tools these kinds of as Cobalt Strike and Main Impact, in addition to demonstrating an curiosity in the latter on RAIDForums.
“IIS modules are not a frequent structure for backdoors, particularly when in contrast to usual web application threats like web shells and can consequently simply be skipped throughout conventional file monitoring endeavours,” Rascagneres and Delcher reported. “The malicious module […] signifies an efficient solution for attackers to acquire a solid foothold in qualified networks by persisting inside an Exchange server.”
Located this posting exciting? Observe THN on Facebook, Twitter and LinkedIn to study much more exclusive content we submit.
Some sections of this posting are sourced from:
thehackernews.com



 Government Experts in Last Minute Seasonal Scam Warning
Government Experts in Last Minute Seasonal Scam Warning