Researchers on Monday took the wraps off a freshly discovered Linux and Windows re-implementation of Cobalt Strike Beacon that’s actively set its sights on authorities, telecommunications, info technology, and fiscal institutions in the wild.
The as-but undetected model of the penetration tests instrument — codenamed “Vermilion Strike” — marks a single of the unusual Linux ports, which has been customarily a Windows-dependent red staff device greatly repurposed by adversaries to mount an array of targeted attacks. Cobalt Strike expenditures by itself as a “danger emulation program,” with Beacon becoming the payload engineered to product an superior actor and duplicate their article-exploitation steps.
“The stealthy sample utilizes Cobalt Strike’s command-and-regulate (C2) protocol when speaking to the C2 server and has remote access abilities these kinds of as uploading documents, working shell instructions and producing to data files,” Intezer scientists stated in a report revealed nowadays and shared with The Hacker Information.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The Israeli cybersecurity company’s results arrive from an artifact uploaded to VirusTotal on August 10 from Malaysia. As of writing, only two anti-malware engines flag the file as malicious.
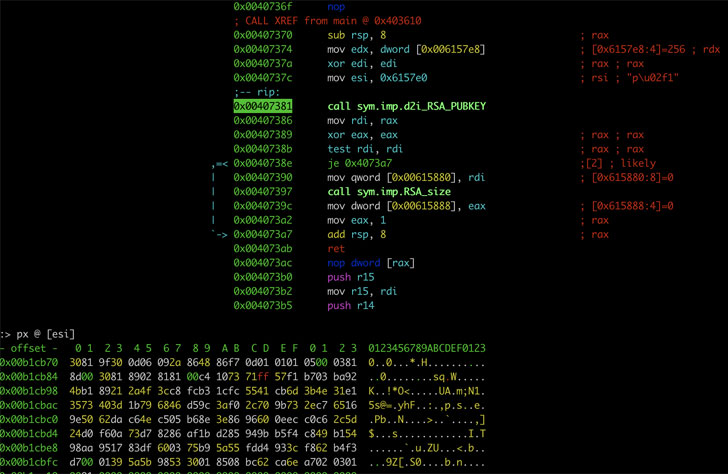
As soon as installed, the malware runs alone in the qualifications and decrypt the configuration essential for the beacon to perform, in advance of fingerprinting the compromised Linux equipment and developing communications with a remote server above DNS or HTTP to retrieve foundation64-encoded and AES-encrypted directions that let it operate arbitrary commands, publish to files, and upload documents back to the server.
Curiously, supplemental samples discovered all through the course of the investigation have drop mild on the Windows variant of the malware, sharing overlaps in the features and the C2 domains employed to remotely commandeer the hosts. Intezer also called out the espionage campaign’s minimal scope, noting the malware’s use in particular attacks as opposed to significant-scale intrusions, although also attributing it to a “competent risk actor” owing to the actuality that Vermilion Strike has not been noticed in other attacks to date.
“Vermilion Strike and other Linux threats stay a frequent menace. The predominance of Linux servers in the cloud and its continued rise invitations APTs to modify their toolsets in get to navigate the current surroundings,” the scientists said.
Observed this article intriguing? Observe THN on Fb, Twitter and LinkedIn to read through additional distinctive articles we article.
Some areas of this write-up are sourced from:
thehackernews.com

 Critical Bug Reported in NPM Package With Millions of Downloads Weekly
Critical Bug Reported in NPM Package With Millions of Downloads Weekly