A few cafe purchasing platforms MenuDrive, Harbortouch, and InTouchPOS were the goal of two Magecart skimming strategies that resulted in the compromise of at the very least 311 dining establishments.
The trio of breaches has led to the theft of extra than 50,000 payment card information from these contaminated restaurants and posted for sale on the dark web.
“The on line buying platforms MenuDrive and Harbortouch were focused by the similar Magecart marketing campaign, resulting in e-skimmer bacterial infections on 80 dining places using MenuDrive and 74 working with Harbortouch,” cybersecurity agency Recorded Long term discovered in a report.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“InTouchPOS was targeted by a individual, unrelated Magecart marketing campaign, ensuing in e-skimmer bacterial infections on 157 places to eat making use of the platform.”

Magecart actors have a historical past of infecting e-commerce sites with JavaScript skimmers to steal on-line shoppers’ payment card information, billing information and facts, and other individually identifiable information (PII).
The 1st set of routines is thought to have started off close to January 18, 2022, and continued until eventually the malicious area utilised in the marketing campaign was blocked on Might 26. The InTouchPOS campaign, on the other hand, has remained active given that November 12, 2021.
It can be worth noting that the details exfiltration domain used in the infections of MenuDrive and Harbortouch has also been determined by the U.S. Federal Bureau of Investigation (FBI) in a May possibly 2022 flash warn.
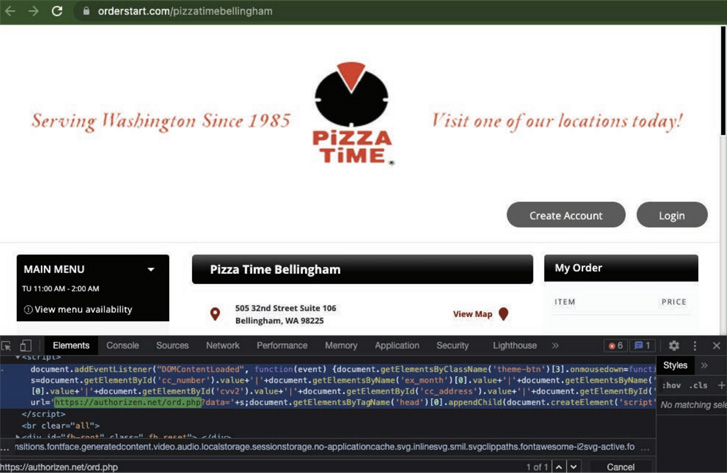
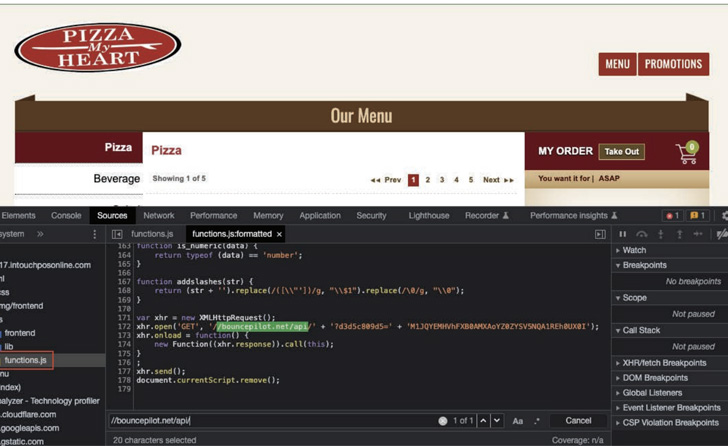
The attacks entail inserting destructive PHP code into the businesses’ online checkout internet pages by using gain of recognized security flaws in the solutions to scrape and transmit the consumer details to a server underneath the attacker’s command.
The strategy is that by targeting on the internet purchasing platforms, it can guide to a scenario exactly where when even a single platform is attacked, dozens or even hundreds of places to eat can have their transactions compromised, which permits “cybercriminals to steal large quantities of buyer payment card knowledge disproportionate to the range of devices they essentially hack.”

The enhancement is significant for a variety of factors. Very first, the intrusions are a departure from the menace actor’s standard concentrating on of the Magento e-commerce system, a truth exemplified by the uptick in skimmer attacks aimed at a WordPress plugin named WooCommerce.
Moreover, it serves to highlight how Magecart strategies are now singling out small, local eating places that depend on third-party program from lesser-identified on the internet buying companies in lieu of creating their individual checkout web web pages, effectively widening the pool of attack vectors.
“Centralized buying platforms servicing a number of merchants provide a exclusive prospect for Magecart menace actors to acquire shopper PII and payment card details,” the researchers mentioned. “Cybercriminals’ increasing fascination in focusing on online ordering platforms signifies a new dimension of risk for dining places.”
Identified this write-up intriguing? Follow THN on Fb, Twitter and LinkedIn to read through much more exceptional material we submit.
Some components of this posting are sourced from:
thehackernews.com


 Medical Device Maker to Pay $13m in False Claims Case
Medical Device Maker to Pay $13m in False Claims Case