A malicious offer hosted on the NuGet offer supervisor for the .NET Framework has been uncovered to supply a distant accessibility trojan identified as SeroXen RAT.
The package deal, named Pathoschild.Stardew.Mod.Construct.Config and released by a person named Disti, is a typosquat of a genuine package deal known as Pathoschild.Stardew.ModBuildConfig, software package supply chain security company Phylum claimed in a report right now.
While the genuine bundle has been given approximately 79,000 downloads to date, the malicious variant is mentioned to have artificially inflated its download depend just after becoming revealed on October 6, 2023, to surpass 100,000 downloads.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The profile guiding the package has released six other offers that have attracted no much less than 2.1 million downloads cumulatively, 4 of which masquerade as libraries for several crypto products and services like Kraken, KuCoin, Solana, and Monero, but are also created to deploy SeroXen RAT.
The attack chain is initiated through set up of the package deal by suggests of a tools/init.ps1 script that is intended to achieve code execution with out triggering any warning, a actions formerly disclosed by JFrog in March 2023 as being exploited to retrieve following-stage malware.
“Even though it is deprecated – the init.ps1 script is nonetheless honored by Visual Studio, and will run without having any warning when setting up a NuGet package,” JFrog mentioned at the time. “Within the .ps1 file, an attacker can compose arbitrary instructions.”

In the package analyzed by Phylum, the PowerShell script is utilised to down load a file named x.bin from a remote server that, in truth, is a seriously-obfuscated Windows Batch script, which, in convert, is dependable for developing and executing yet another PowerShell script to in the long run deploy the SeroXen RAT.
An off-the-shelf malware, SeroXen RAT is provided for sale for $60 for a lifetime bundle, building it very easily obtainable to cyber criminals. It is a fileless RAT that brings together the capabilities of Quasar RAT, the r77 rootkit, and the Windows command-line instrument NirCmd.
“The discovery of SeroXen RAT in NuGet offers only underscores how attackers carry on to exploit open up-source ecosystems and the builders that use them,” Phylum mentioned.
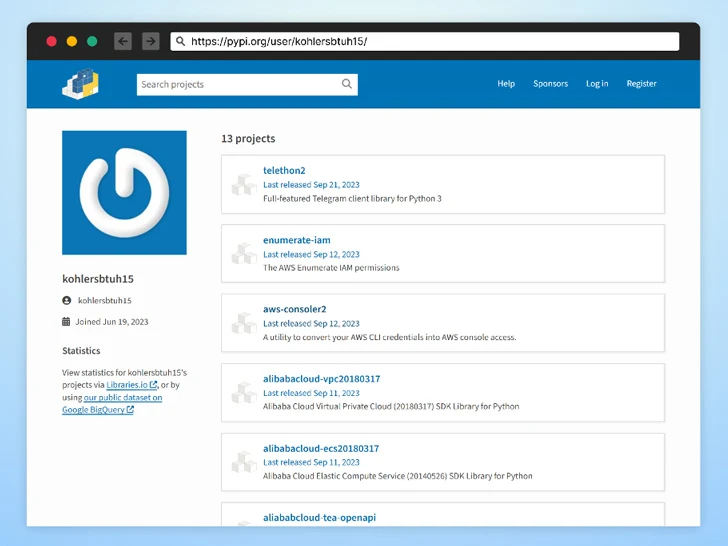
The growth will come as the enterprise detected seven malicious packages on the Python Bundle Index (PyPI) repository that impersonate genuine offerings from cloud service companies this sort of as Aliyun, Amazon Web Providers (AWS), and Tencent Cloud to surreptitiously transmit the qualifications to an obfuscated distant URL.
The names of the offers are stated underneath –
- tencent-cloud-python-sdk
- python-alibabacloud-sdk-main
- alibabacloud-oss2
- python-alibabacloud-tea-openapi
- aws-enumerate-iam
- enumerate-iam-aws
- alisdkcore
“In this campaign, the attacker is exploiting a developer’s rely on, taking an current, nicely-proven codebase and inserting a single bit of destructive code aimed at exfiltrating delicate cloud qualifications,” Phylum mentioned.
“The subtlety lies in the attacker’s system of preserving the original performance of the offers, trying to fly underneath the radar, so to converse. The attack is minimalistic and simple, still powerful.”

Checkmarx, which also shared supplemental details of the exact marketing campaign, reported it’s also created to concentrate on Telegram via a misleading offer named telethon2, which aims to mimic telethon, a Python library to interact with Telegram’s API.
A bulk of the downloads of the counterfeit libraries have originated from the U.S., adopted by China, Singapore, Hong Kong, Russia, and France.
“Rather than carrying out automatic execution, the malicious code in just these deals was strategically concealed within capabilities, built to cause only when these functions ended up termed,” the firm claimed. “The attackers leveraged Typosquatting and StarJacking procedures to lure builders to their destructive deals.”
Earlier this thirty day period, Checkmarx more uncovered a relentless and progressively sophisticated marketing campaign aimed at PyPI to seed the program offer chain with 271 malicious Python packages in order to steal sensitive information and cryptocurrency from Windows hosts.
The deals, which also came equipped with features to dismantle program defenses, ended up collectively downloaded around 75,000 situations prior to getting taken down.
Identified this short article appealing? Follow us on Twitter and LinkedIn to read more distinctive material we post.
Some parts of this posting are sourced from:
thehackernews.com


 ShellBot Uses Hex IPs to Evade Detection in Attacks on Linux SSH Servers
ShellBot Uses Hex IPs to Evade Detection in Attacks on Linux SSH Servers