An up to date variation of a malware loader regarded as BLISTER is remaining applied as section of SocGholish infection chains to distribute an open up-resource command-and-manage (C2) framework called Mythic.
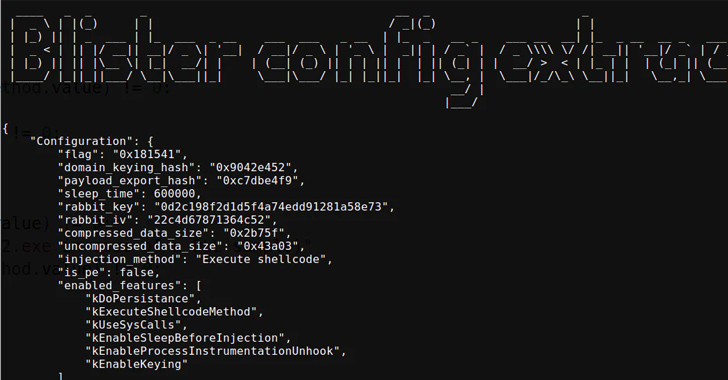
“New BLISTER update incorporates keying feature that lets for precise focusing on of victim networks and lowers publicity in just VM/sandbox environments,” Elastic Security Labs scientists Salim Bitam and Daniel Stepanic mentioned in a technical report revealed late very last thirty day period.
BLISTER was to start with uncovered by the enterprise in December 2021 acting as a conduit to distribute Cobalt Strike and BitRAT payloads on compromised devices.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The use of the malware together with SocGholish (aka FakeUpdates), a JavaScript-centered downloader malware, to provide Mythic was beforehand disclosed by Palo Alto Networks Unit 42 in July 2023.
In these attacks, BLISTER is embedded within a authentic VLC Media Participant library in an try to get all around security software and infiltrate victim environments.
Approaching WEBINARDetect, React, Protect: ITDR and SSPM for Complete SaaS Security
Find out how Identification Menace Detection & Reaction (ITDR) identifies and mitigates threats with the assist of SSPM. Find out how to safe your company SaaS apps and shield your information, even soon after a breach.
Supercharge Your Abilities
Equally SocGholish and BLISTER have been utilized in tandem as portion of several strategies, with the latter made use of as a 2nd-phase loader to distribute Cobalt Strike and LockBit ransomware, as evidenced by Red Canary and Trend Micro in early 2022.
A closer examination of the malware displays that it’s currently being actively preserved, with the malware authors incorporating a slew of approaches to fly less than the radar and complicate analysis.
“BLISTER is a loader that proceeds to stay less than the radar, actively getting utilised to load a wide variety of malware together with clipbankers, information stealers, trojans, ransomware, and shellcode,” Elastic observed in April 2023.
Uncovered this report attention-grabbing? Stick to us on Twitter and LinkedIn to read through extra special articles we article.
Some areas of this posting are sourced from:
thehackernews.com

 New Python Variant of Chaes Malware Targets Banking and Logistics Industries
New Python Variant of Chaes Malware Targets Banking and Logistics Industries