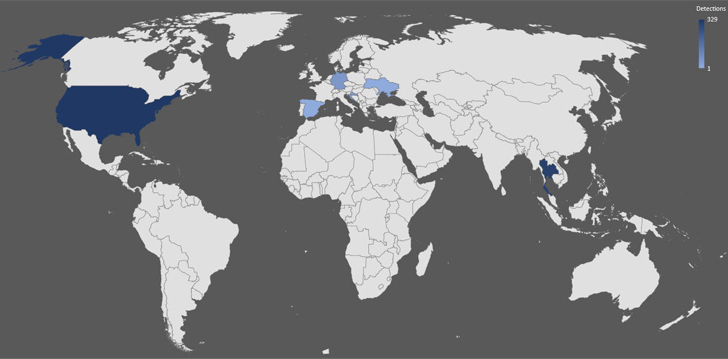
A new Golang-based facts stealer termed Skuld has compromised Windows units across Europe, Southeast Asia, and the U.S.
“This new malware strain tries to steal delicate details from its victims,” Trellix researcher Ernesto Fernández Provecho claimed in a Tuesday evaluation. “To attain this job, it searches for facts stored in programs this sort of as Discord and web browsers data from the method and information saved in the victim’s folders.”
Skuld, which shares overlaps with publicly offered stealers like Creal Stealer, Luna Grabber, and BlackCap Grabber, is the handiwork of a developer who goes by the on line alias Deathined on various social media platforms like GitHub, Twitter, Reddit, and Tumblr.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

Also spotted by Trellix is a Telegram team named deathinews, indicating that these on the web avenues could be utilized to advertise the providing in the potential as a assistance for other threat actors.
The malware, upon execution, checks if it can be working in a virtual setting in an try to thwart investigation. It more extracts the listing of functioning procedures and compares it versus a predefined blocklist. Must any process match with these present in the blocklist, Skuld proceeds to terminate the matched course of action as opposed to terminating alone.
Moreover accumulating method metadata, the malware possesses capabilities to harvest cookies and credentials stored in web browsers as nicely as information current in the Windows consumer profile folders, which include Desktop, Documents, Downloads, Shots, Audio, Films, and OneDrive.
Artifacts analyzed by Trellix display that it is engineered to corrupt legit documents linked with Greater Discord and Discord Token Protector and inject JavaScript code into the Discord app to siphon backup codes, mirroring a technique similar to that of yet another Rust-dependent infostealer a short while ago documented by Trend Micro.
Forthcoming WEBINAR🔐 Mastering API Security: Being familiar with Your True Attack Area
Find the untapped vulnerabilities in your API ecosystem and get proactive steps to ironclad security. Join our insightful webinar!
Be part of the Session.wn-button,.wn-label,.wn-label:just aftershow:inline-block.check out_two_webinarmargin:20px 10px 30px 0background:#f9fbffcolor:#160755padding: 5%border:2px stable #d9deffborder-radius:10pxtext-align:leftbox-shadow:10px 10px #e2ebff-webkit-border-prime-remaining-radius:25px-moz-border-radius-topleft:25px-webkit-border-bottom-right-radius:25px-moz-border-radius-bottomright:25px.wn-labelfont-size:13pxmargin:20px 0font-fat:600letter-spacing:.6pxcolor:#596cec.wn-label:followingwidth:50pxheight:6pxcontent:”border-top:2px reliable #d9deffmargin: 8px.wn-titlefont-dimension:21pxpadding:10px 0font-bodyweight:900textual content-align:leftline-peak:33px.wn-descriptiontext-align:leftfont-dimension:15.6pxline-height:26pxmargin:5px !importantcolor:#4e6a8d.wn-buttonpadding:6px 12pxborder-radius:5pxbackground-coloration:#4469f5font-dimensions:15pxcolor:#fff!importantborder:0line-height:inherittext-decoration:none!importantcursor:pointermargin:15px 20pxfloat:leftfont-bodyweight:500letter-spacing:.2px
Pick samples of Skuld also incorporate a clipper module to change clipboard content and steal cryptocurrency assets by swapping the wallet addresses, which the cybersecurity enterprise theorized is most likely in progress.
Details exfiltration is realized by means of an actor-managed Discord webhook or the Gofile upload services. In the situation of the latter, a reference URL to steal the uploaded ZIP file containing the stolen facts is despatched to the attacker applying the identical Discord webhook functionality.
The enhancement details to steady adoption of the Go programming language amongst menace actors thanks to its “simplicity, efficiency, and cross-system compatibility,” thereby making it an beautiful car or truck to target a number of operating programs and expand their target pool.
“Also, Golang’s compiled nature lets malware authors make binary executables that are extra demanding to evaluate and reverse engineer,” Fernández Provecho noted. “This tends to make it more challenging for security researchers and conventional anti-malware alternatives to detect and mitigate these threats successfully.”
Discovered this report interesting? Abide by us on Twitter and LinkedIn to study additional exclusive content material we submit.
Some components of this report are sourced from:
thehackernews.com

 Where from, Where to — The Evolution of Network Security
Where from, Where to — The Evolution of Network Security