A new IoT botnet malware dubbed RapperBot has been noticed promptly evolving its capabilities because it was 1st discovered in mid-June 2022.
“This family borrows seriously from the original Mirai resource code, but what separates it from other IoT malware families is its constructed-in functionality to brute drive credentials and obtain accessibility to SSH servers in its place of Telnet as executed in Mirai,” Fortinet FortiGuard Labs stated in a report.
The malware, which will get its title from an embedded URL to a YouTube rap audio movie in an earlier model, is stated to have amassed a escalating assortment of compromised SSH servers, with over 3,500 exceptional IP addresses utilised to scan and brute-pressure their way into the servers.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

RapperBot’s present implementation also delineates it from Mirai, enabling it to largely purpose as an SSH brute-drive software with constrained capabilities to have out dispersed denial-of-service (DDoS) attacks.
The deviation from classic Mirai actions is even further evidenced in its try to set up persistence on the compromised host, proficiently permitting the menace actor to preserve extended-term accessibility very long right after the malware has been taken out or the system has been rebooted.
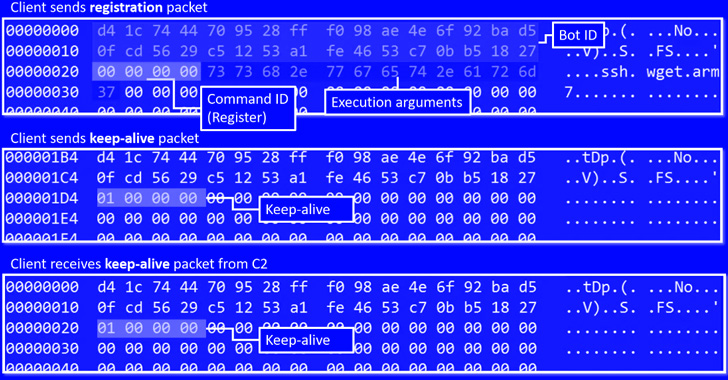
The attacks entail brute-forcing possible targets employing a listing of qualifications gained from a remote server. Upon correctly breaking into a susceptible SSH server, the valid credentials are exfiltrated again to the command-and-command.
“Considering that mid-July, RapperBot has switched from self-propagation to preserving remote entry into the brute-forced SSH servers,” the researchers mentioned.
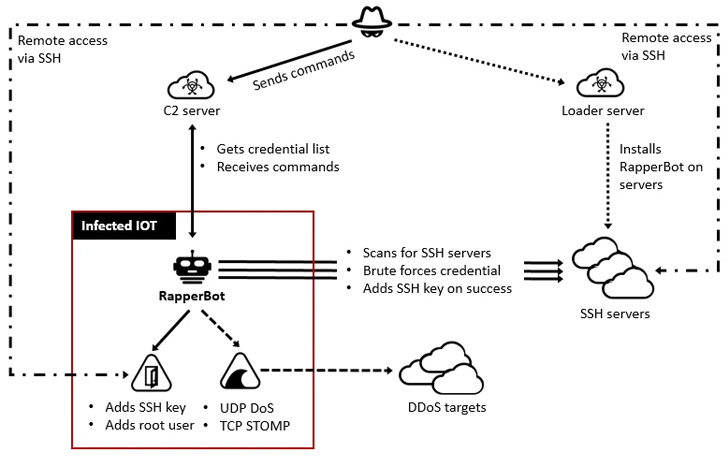
The entry is achieved by adding the operators’ SSH general public critical to a particular file known as “~/.ssh/authorized_keys,” allowing the adversary to hook up and authenticate to the server using the corresponding personal private critical with out possessing to furnish a password.
“This offers a threat to compromised SSH servers as menace actors can obtain them even right after SSH credentials have been changed or SSH password authentication is disabled,” the scientists spelled out.
“In addition, since the file is replaced, all existing authorized keys are deleted, which stops reputable users from accessing the SSH server by way of community crucial authentication.”
The shift also enables the malware to maintain its entry to these hacked devices by way of SSH, permitting the actor to leverage the foothold to conduct Mirai-styled denial-of-support attacks.
These discrepancies from other IoT malware families have experienced the aspect-outcome of creating its main motivations some thing of a thriller, a point more intricate by the point that RapperBot’s authors have remaining small-to-no telltale indications of their provenance.

The ditching of self-propagation in favor of persistence notwithstanding, the botnet is mentioned to have been through sizeable improvements in a shorter span of time, chief among the them staying the removing of DDoS attack features from the artifacts at just one level, only to be reintroduced a 7 days later.
The targets of the campaign, ultimately, continue being nebulous at ideal, with no comply with-on activity observed post a prosperous compromise. What is actually obvious is that SSH servers with default or guessable qualifications are currently being corralled into a botnet for some unspecified future purpose.
To fend off these kinds of infections, it really is recommended that end users established powerful passwords for devices or disable password authentication for SSH the place feasible.
“While this danger intensely borrows code from Mirai, it has attributes that established it aside from its predecessor and its variants,” the researchers stated. “Its ability to persist in the sufferer program provides danger actors the flexibility to use them for any malicious intent they motivation.”
Found this write-up exciting? Follow THN on Facebook, Twitter and LinkedIn to examine extra special articles we submit.
Some sections of this post are sourced from:
thehackernews.com

 Hackers Exploit Twitter Vulnerability to Exposes 5.4 Million Accounts
Hackers Exploit Twitter Vulnerability to Exposes 5.4 Million Accounts