Even as Visa issued a warning about a new JavaScript web skimmer recognised as Baka, cybersecurity researchers have uncovered a new flaw in the firm’s EMV enabled cards that enable cybercriminals to receive resources and defraud cardholders as effectively as merchants illicitly.
The investigate, published by a group of academics from the ETH Zurich, is a PIN bypass attack that permits the adversaries to leverage a victim’s stolen or lost credit rating card for making significant-worth buys with no awareness of the card’s PIN, and even trick a level of sale (PoS) terminal into accepting an unauthentic offline card transaction.
All contemporary contactless playing cards that make use of the Visa protocol, together with Visa Credit rating, Visa Debit, Visa Electron, and V Pay out playing cards, are afflicted by the security flaw, but the scientists posited it could apply to EMV protocols implemented by Find and UnionPay as nicely. The loophole, nonetheless, will not effects Mastercard, American Convey, and JCB.
The results will be offered at the 42nd IEEE Symposium on Security and Privacy to be held in San Francisco next May.
Modifying Card Transaction Qualifiers Through MitM Attack
EMV (brief for Europay, Mastercard, and Visa), the greatly made use of international protocol regular for smartcard payment, necessitates that greater amounts can only be debited from credit score cards with a PIN code.
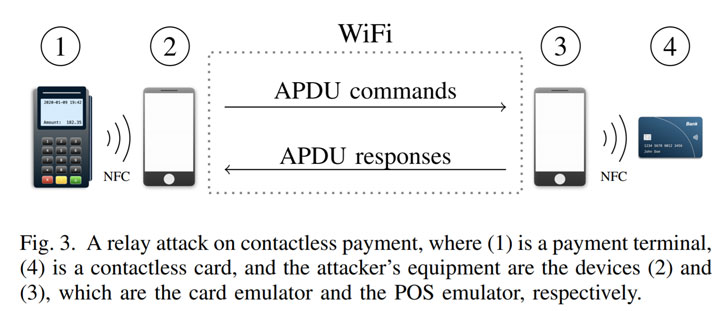
But the set up devised by ETH scientists exploits a critical flaw in the protocol to mount a male-in-the-middle (MitM) attack via an Android application that “instructs the terminal that PIN verification is not necessary due to the fact the cardholder verification was carried out on the consumer’s product.”
The issue stems from the actuality the Cardholder verification process (CVM), which is employed to validate irrespective of whether an personal trying a transaction with a credit score or debit card is the authentic cardholder, is not cryptographically secured from modification.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
As a outcome, the Card Transaction Qualifiers (CTQ) utilised to establish what CVM check out, if any, is needed for the transaction can be modified to advise the PoS terminal to override the PIN verification and that the verification was carried out employing the cardholder’s gadget these types of as a smartwatch or smartphone (named Purchaser Product Cardholder Verification Strategy or CDCVM).
Exploiting Offline Transactions Without having Being Billed
In addition, the researchers uncovered a next vulnerability, which includes offline contactless transactions carried out by possibly a Visa or an outdated Mastercard card, enabling the attacker to change a precise piece of knowledge termed “Application Cryptogram” (AC) ahead of it is shipped to the terminal.
Offline cards are normally applied to instantly spend for goods and products and services from a cardholder’s lender account with no necessitating a PIN amount. But given that these transactions are not linked to an online technique, there is a delay of 24 to 72 several hours in advance of the bank confirms the transaction’s legitimacy working with the cryptogram, and the amount of money of the order is debited from the account.
A legal can leverage this delayed processing mechanism to use their card to total a reduced-benefit and offline transaction without getting charged, in addition to earning absent with buys by the time the issuing bank declines the transaction thanks to the wrong cryptogram.
“This constitutes a ‘free lunch’ attack in that the felony can invest in minimal-worth merchandise or services without having actually being billed at all,” the scientists reported, including the low-value mother nature of these transactions is not likely to be an “attractive company model for criminals.”
Mitigating PIN bypass and offline assaults
Aside from notifying Visa of the flaws, the scientists have also proposed 3 computer software fixes to the protocol to avert PIN bypass and offline assaults, which include working with Dynamic Details Authentication (DDA) to secure significant-price on the internet transactions and necessitating the use of online cryptogram in all PoS terminals, which results in offline transactions to be processed on-line.
“Our attack clearly show[ed] that the PIN is worthless for Visa contactless transactions [and] discovered stunning discrepancies between the security of the contactless payment protocols of Mastercard and Visa, exhibiting that Mastercard is more secure than Visa,” the researchers concluded. “These flaws violate fundamental security properties such as authentication and other guarantees about recognized transactions.”
Identified this short article attention-grabbing? Stick to THN on Fb, Twitter and LinkedIn to browse additional unique content we publish.
Some pieces of this short article is sourced from:
thehackernews.com


 How Zero Trust and SASE Can Redefine Network Defenses for Remote Workforces
How Zero Trust and SASE Can Redefine Network Defenses for Remote Workforces