Cybersecurity scientists have disclosed a new variation of the SolarMarker malware that packs in new advancements with the objective of updating its defense evasion skills and staying beneath the radar.
“The current variation demonstrated an evolution from Windows Transportable Executables (EXE data files) to functioning with Windows installer deal data files (MSI documents),” Palo Alto Networks Unit 42 researchers mentioned in a report published this thirty day period. “This marketing campaign is however in improvement and likely back to making use of executables data files (EXE) as it did in its earlier versions.”
SolarMarker, also termed Jupyter, leverages manipulated research engine optimization (Web optimization) practices as its most important infection vector. It can be recognized for its information and facts thieving and backdoor functions, enabling the attackers to steal info stored in web browsers and execute arbitrary commands retrieved from a distant server.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
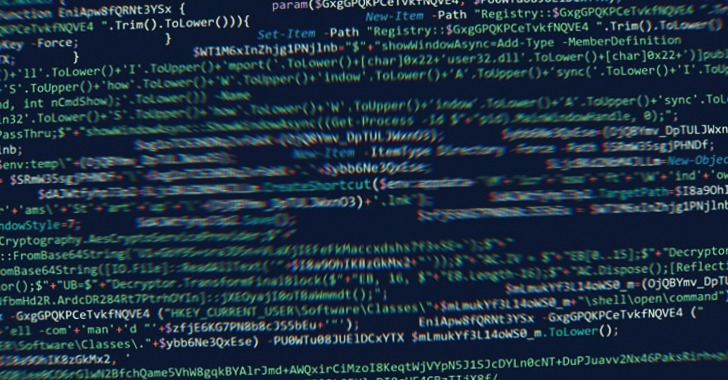
In February 2022, the operators of SolarMarker were noticed applying stealthy Windows Registry tips to set up very long-time period persistence on compromised methods.
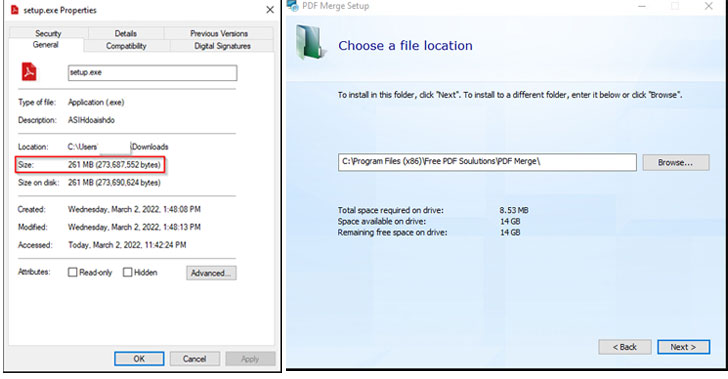
The evolving attack designs noticed by Unit 42 are a continuation of this behavior, what with the infection chains taking the sort of 250MB executables for PDF viewers and utilities that are hosted on fraudulent web sites packed with key phrases and use Search engine optimization tactics to rank them better in the look for benefits.
The massive file size not only permits the initial stage dropper to avoid automated examination by antivirus engines, it’s also made to obtain and set up the authentic program when, in the background, it activates the execution of a PowerShell installer that deploys the SolarMarker malware.
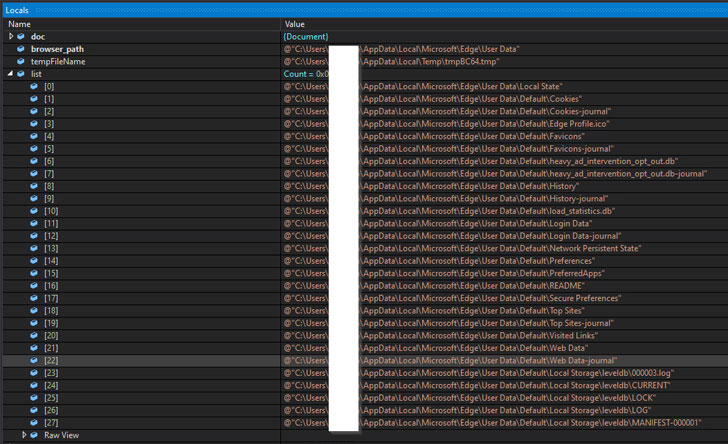
A .NET-based mostly payload, the SolarMarker backdoor is geared up with abilities to conduct inner reconnaissance and vacuum procedure metadata, all of which is exfiltrated to the remote server around an encrypted channel.

The implant also features as a conduit to deploy the SolarMarker’s information and facts-thieving module on the sufferer machine. The stealer, for its aspect, can siphon autofill data, cookies, passwords, and credit rating card information from web browsers.
“The malware invests important effort into defense evasion, which consists of procedures like signed information, huge information, impersonation of respectable computer software installations and obfuscated PowerShell scripts,” the scientists explained.
Identified this write-up fascinating? Follow THN on Fb, Twitter and LinkedIn to read through a lot more exclusive information we put up.
Some pieces of this write-up are sourced from:
thehackernews.com

 New Hacking Campaign Targeting Ukrainian Government with IcedID Malware
New Hacking Campaign Targeting Ukrainian Government with IcedID Malware