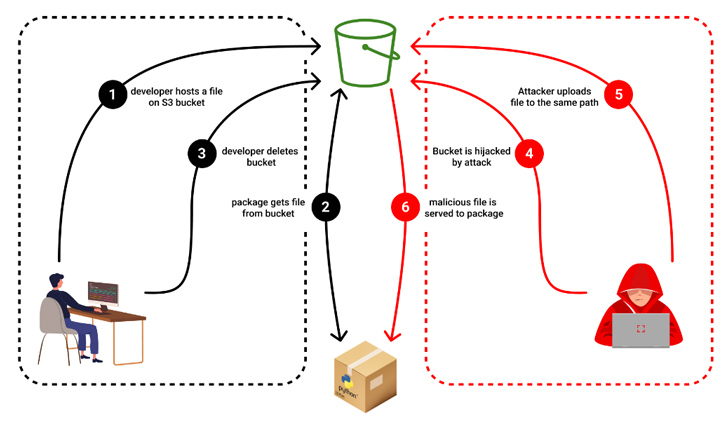
In what is actually a new type of application offer chain attack aimed at open up supply projects, it has emerged that risk actors could seize management of expired Amazon S3 buckets to provide rogue binaries with no altering the modules themselves.
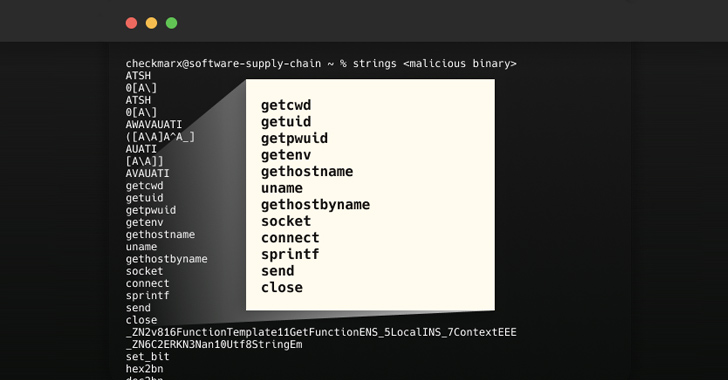
“Destructive binaries steal the user IDs, passwords, community device surroundings variables, and local host name, and then exfiltrates the stolen knowledge to the hijacked bucket,” Checkmarx researcher Dude Nachshon reported.
The attack was initial observed in the case of an npm offer called bignum, which, until version .13., relied on an Amazon S3 bucket to download pre-crafted binary versions of an addon named node-pre-gyp for the duration of set up.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

“These binaries were being released on a now-expired S3 bucket which has since been claimed by a malicious 3rd party which is now serving binaries made up of malware that exfiltrates details from the user’s laptop,” in accordance to a GitHub advisory printed on Could 24, 2023.
An unknown danger actor is claimed to have seized on the prospect that the S3 bucket was when lively to provide malware when unsuspecting customers downloaded the deal in question.
“If a bundle pointed to a bucket as its resource, the pointer would carry on to exist even after the bucket’s deletion,” Nachshon defined. “This abnormality permitted the attacker to reroute the pointer toward the taken-above bucket.”
A reverse engineering of the malware sample has revealed that it truly is capable of plundering person qualifications and environment specifics, and transmitting the information and facts to the exact same hijacked bucket.
Checkmarx mentioned it observed several deals employing deserted S3 buckets, building them prone to the novel attack vector. If anything at all, the advancement is a signal that danger actors are regularly on the lookout for distinct ways to poison the software program source chain.
Forthcoming WEBINAR🔐 Mastering API Security: Comprehension Your True Attack Floor
Uncover the untapped vulnerabilities in your API ecosystem and get proactive ways in the direction of ironclad security. Join our insightful webinar!
Be a part of the Session.wn-button,.wn-label,.wn-label:followingdisplay:inline-block.look at_two_webinarmargin:20px 10px 30px 0background:#f9fbffcolor:#160755padding: 5%border:2px stable #d9deffborder-radius:10pxtext-align:leftbox-shadow:10px 10px #e2ebff-webkit-border-prime-still left-radius:25px-moz-border-radius-topleft:25px-webkit-border-bottom-appropriate-radius:25px-moz-border-radius-bottomright:25px.wn-labelfont-measurement:13pxmargin:20px 0font-weight:600letter-spacing:.6pxcolor:#596cec.wn-label:right afterwidth:50pxheight:6pxcontent:”border-prime:2px reliable #d9deffmargin: 8px.wn-titlefont-measurement:21pxpadding:10px 0font-bodyweight:900text-align:leftline-top:33px.wn-descriptiontext-align:leftfont-size:15.6pxline-peak:26pxmargin:5px !importantcolor:#4e6a8d.wn-buttonpadding:6px 12pxborder-radius:5pxbackground-color:#4469f5font-sizing:15pxcolor:#fff!importantborder:0line-peak:inherittext-decoration:none!importantcursor:pointermargin:15px 20pxfloat:leftfont-fat:500letter-spacing:.2px
“This new twist in the realm of subdomain takeovers serves as a wake-up call to builders and organizations,” Nachshon mentioned. “An deserted hosting bucket or an out of date subdomain is not just a neglected artifact in the improper arms, it can grow to be a strong weapon for info theft and intrusion.”
The growth also comes nearly a 7 days after Cyble unearthed 160 malicious python offers that are approximated to have been downloaded in excess of 45,000 periods and showcased capabilities to extract login qualifications and credit card facts.
Identified this report exciting? Comply with us on Twitter and LinkedIn to browse more distinctive content material we submit.
Some pieces of this article are sourced from:
thehackernews.com

 #InfosecurityEurope: New Study Takes a Deep Dive Into Lookalike Attacks
#InfosecurityEurope: New Study Takes a Deep Dive Into Lookalike Attacks