The menace actor driving the attacks on Twilio and Cloudflare before this month has been connected to a broader phishing marketing campaign aimed at 136 companies that resulted in a cumulative compromise of 9,931 accounts.
The exercise has been condemned 0ktapus by Team-IB simply because the preliminary aim of the attacks was to “receive Okta id credentials and two-factor authentication (2FA) codes from buyers of the focused companies.”
Contacting the attacks well created and executed, the Singapore-headquartered enterprise explained the adversary singled out personnel of corporations that are shoppers of identification services service provider Okta.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

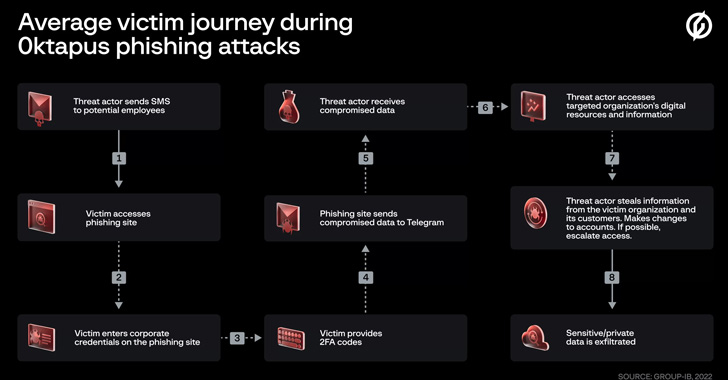
The modus operandi associated sending targets text messages that contains back links to phishing web-sites that impersonated the Okta authentication page of the respective focused entities.
“This circumstance is of curiosity due to the fact regardless of working with lower-ability approaches it was capable to compromise a large variety of very well-identified companies,” Team-IB said. “In addition, at the time the attackers compromised an organization they have been quickly equipped to pivot and launch subsequent provide chain attacks, indicating that the attack was prepared diligently in progress.”
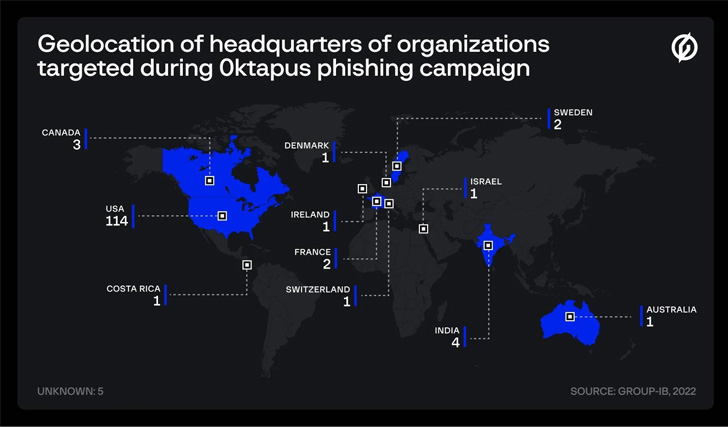
At the very least 169 exclusive phishing domains are said to have been set up for this intent, with target corporations largely situated in the U.S. (114), India (4), Canada (3), France (2), Sweden (2), and Australia (1), amongst others. These internet websites had been united by the truth that they produced use of a beforehand undocumented phishing package.
A vast majority of the impacted companies are application corporations, followed by those belonging to telecom, business companies, finance, education and learning, retail, and logistics sectors.
What is actually noteworthy about the attacks is the use of an actor-controlled Telegram channel to fall the compromised facts, which involved person qualifications, email addresses, and multi-factor authentication (MFA) codes.
Group-IB stated it was able to website link one particular of the channel administrators, who goes by the alias X, to a Twitter and a GitHub account that suggests the particular person could be centered in the U.S. condition of North Carolina.

The greatest aims of the campaign keep on being unclear, but it’s suspected to be espionage and economically inspired, enabling the menace actor to accessibility confidential info, mental property, and company inboxes, as perfectly as siphon cash.
On top of that, the attempts to hack into Sign accounts suggest that the attackers are also striving to get keep of private conversations and other sensitive facts. It is nevertheless not recognized how the hackers acquired phone figures and the names of workers.
“While the threat actor may well have been fortunate in their attacks it is much additional probable that they cautiously prepared their phishing campaign to launch advanced offer chain attacks,” Group-IB analyst Roberto Martinez claimed.
“It is not however apparent if the attacks were being planned finish-to-finish in advance or whether or not opportunistic actions have been taken at just about every phase. Regardless, the 0ktapus marketing campaign has been incredibly thriving, and the entire scale of it may well not be identified for some time.”
Uncovered this report exciting? Stick to THN on Facebook, Twitter and LinkedIn to study extra distinctive material we publish.
Some elements of this short article are sourced from:
thehackernews.com

 U.S. Government Spending Billions on Cybersecurity
U.S. Government Spending Billions on Cybersecurity