A danger actor recognized as Prolific Puma has been protecting a lower profile and working an underground link shortening service that is provided to other risk actors for at the very least over the past 4 many years.
Prolific Puma results in “area names with an RDGA [registered domain generation algorithm] and use these domains to offer a link shortening company to other malicious actors, assisting them evade detection although they distribute phishing, frauds, and malware,” Infoblox explained in a new investigation pieced jointly from Area Identify Method (DNS) analytics.
With malicious actors regarded to use website link shorteners for phishing attacks, the adversary performs an significant part in the cybercrime supply chain, registering between 35,000 to 75,000 distinctive domain names due to the fact April 2022. Prolific Puma is also a DNS risk actor for leveraging DNS infrastructure for nefarious needs.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
A noteworthy facet of the risk actor’s functions is the use of an American area registrar and web hosting business named NameSilo for registration and name servers thanks to its affordability and an API that facilitates bulk registration.

Prolific Puma, which does not market its shortening support on underground markets, has also been observed resorting to strategic growing old to park registered domains for numerous weeks prior to hosting their provider with nameless companies.
“Prolific Puma domains are alphanumeric, pseudo-random, with variable length, generally 3 or 4 people extended, but we have also observed SLD labels as prolonged as 7 people,” Infoblox stated.
Additionally, the threat actor has registered countless numbers of domains in the U.S. prime-level domain (usTLD) considering the fact that May perhaps 2023, frequently using an email deal with that contains a reference to the tune OCT 33 by a psychedelic soul band referred to as Black Pumas: blackpumaoct33@ukr[.]net.
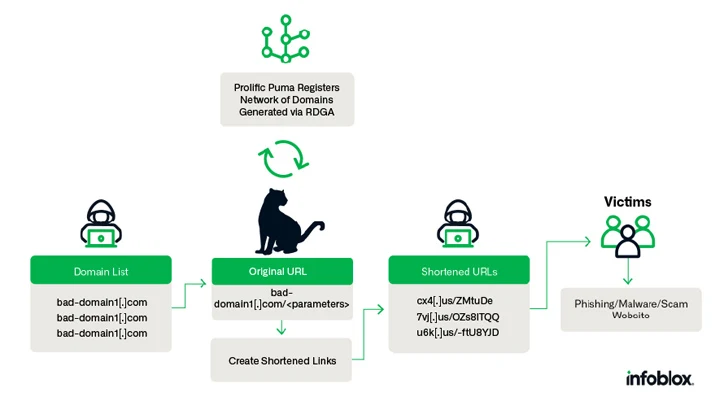
The actual-globe identity and origins of Prolific Puma continues to be not known as still. That explained, multiple menace actors are stated to be employing the presenting to consider people to phishing and scam web pages, CAPTCHA troubles, and even other shortened backlinks produced by a distinct service.
In one particular instance of a phishing-cum-malware attack documented by Infoblox, victims clicking on a shortened connection are taken to a landing web page that requests them to supply personal facts and make a payment, and in the long run infect their methods with browser plugin malware.
The disclosure will come months following the corporation uncovered a different persistent DNS threat actor codenamed Open Tangle that leverages a huge infrastructure of lookalike domains of reputable monetary institutions to concentrate on consumers for phishing and smishing attacks.
“Prolific Puma demonstrates how the DNS can be abused to guidance criminal activity and continue being undetected for yrs,” it explained.
Kopeechka Hacking Resource Floods On the internet Platforms with Bogus Accounts
The progress also follows a new report from Trend Micro, which uncovered that lesser-qualified cybercriminals are making use of a new tool termed Kopeechka (indicating “penny” in Russian) to automate the development of hundreds of pretend social media accounts in just a couple seconds.
“The support has been active because the commencing of 2019 and provides straightforward account registering expert services for preferred social media platforms, like Instagram, Telegram, Facebook, and X (previously Twitter),” security researcher Cedric Pernet reported.
Kopeechka presents two varieties of various email addresses to help with the mass-registration method: email addresses hosted in 39 domains owned by the danger actor and all those that are hosted on additional preferred email hosting products and services such as Gmail, Hotmail, Outlook, Rambler, and Zoho Mail.

“Kopeechka does not in fact provide accessibility to the true mailboxes,” Pernet stated. “When customers request for mailboxes to produce social media accounts, they only get the email deal with reference and the specific email that has the affirmation code or URL.”
It can be suspected that these email addresses are both compromised or produced by the Kopeechka actors themselves.

With on the internet providers incorporating phone selection verification to full registration, Kopeechka enables its consumers to pick out from 16 diverse on the web SMS services, most of which originate from Russia.
In addition to accelerating cybercrime and equipping threat actors to launch full-fledged functions at scale, these tools – made as component of the “as-a-service” organization product – highlight the professionalization of the criminal ecosystem.
“Kopeechka’s providers can facilitate an quick and inexpensive way to mass-build accounts on the net, which could be handy to cybercriminals,” Pernet stated.
“When Kopeechka is predominantly made use of for multiple accounts creation, it can also be made use of by cybercriminals who want to increase a degree of anonymity to their routines, as they do not want to use any of their individual email addresses to generate accounts on social media platforms.”
Located this posting interesting? Observe us on Twitter and LinkedIn to browse additional unique content we submit.
Some elements of this short article are sourced from:
thehackernews.com


 Hands on Review: LayerX’s Enterprise Browser Security Extension
Hands on Review: LayerX’s Enterprise Browser Security Extension