A new wave of a cell surveillance campaign has been noticed focusing on the Uyghur community as element of a prolonged-standing adware operation active given that at least 2015, cybersecurity scientists disclosed Thursday.
The intrusions, initially attributed to a danger actor named Scarlet Mimic back again in January 2016, is reported to have encompassed 20 unique variants of the Android malware, which have been disguised as guide, photographs, and an audio version of the Quran.
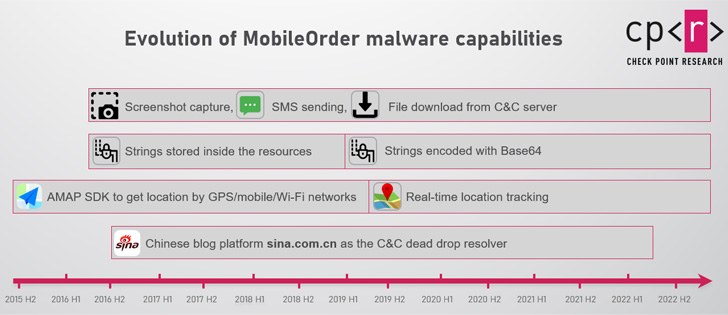
The malware, when reasonably unsophisticated from a specialized standpoint, arrives with intensive capabilities to steal sensitive info from an infected device, deliver SMS messages on the victim’s behalf, make phone calls, and keep track of their areas.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

Furthermore, it allows the recording of incoming and outgoing phone calls as effectively as surrounding audio.
“All this will make it a effective and unsafe surveillance resource,” Israeli cybersecurity organization Check Issue explained in a specialized deepdive, contacting the adware MobileOrder.
It is really really worth noting that a part of the marketing campaign was not too long ago disclosed by researchers from the MalwareHunterTeam and Cyble, in which a e-book written by the exiled Uyghur chief Dolkun Isa was applied as a lure to deliver the malware.
Look at Level stated it observed MobileOrder artifacts in the wild ideal from 2015 to mid-August 2022, with the exception of 2021, when none were detected.
Attack campaigns very likely contain the use of social engineering practices to trick unsuspecting victims into launching destructive applications that reference seemingly innocuous paperwork, images, and audio information.
These apps include a selection of baits, like a PDF about guerrilla warfare and photographs linked to the deployment of paramilitary forces in Ürümqi, the cash of the Xinjiang Uyghur Autonomous Location, in the aftermath of the deadly April 2014 attack.
Opening the rogue app, in flip, launches a decoy doc intended to distract the concentrate on from noticing the destructive steps in the background.
“Some of the variations also request for Gadget Admin and root access, which not only gives the malware full access to the machine, but also prevents the target from very easily uninstalling the application,” the scientists reported.

Other attributes supported by MobileOrder contain executing a distant shell and even dropping added Android Deal (APK) files.
The campaign’s attribution to Scarlet Mimic, per Test Issue, stems from clear code overlaps, shared infrastructure, and the exact victimology patterns.
Furthermore, the ongoing use of MobileOrder indicators a shift in attack vector from desktop to mobile surveillance, what with the actor beforehand connected to a Windows malware termed Psylo Trojan.
When it really is not obvious which of these attacks through the past 7 yrs have been profitable, the pretty actuality that the malware authors are continuing to deploy the spyware is an indicator that some of these endeavours have paid out off.
“The persistence of the campaign, the evolution of the malware and the persistent focus on targeting particular populations indicate that the group’s functions above the decades are profitable to some extent,” Examine Point said.
Located this write-up fascinating? Stick to THN on Fb, Twitter and LinkedIn to browse additional special articles we post.
Some pieces of this short article are sourced from:
thehackernews.com


 Morgan Stanley Fined $35m By SEC For Data Security Lapse
Morgan Stanley Fined $35m By SEC For Data Security Lapse