The cell risk campaign tracked as Roaming Mantis has been joined to a new wave of compromises directed towards French cell phone end users, months following it expanded its focusing on to contain European nations.
No less than 70,000 Android units are stated to have been infected as aspect of the active malware procedure, Sekoia said in a report printed very last week.
Attack chains involving Roaming Mantis, a monetarily motivated Chinese risk actor, are recognised to either deploy a piece of banking trojan named MoqHao (aka XLoader) or redirect iPhone buyers to credential harvesting landing pages that mimic the iCloud login web page.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

“MoqHao (aka Wroba, XLoader for Android) is an Android distant accessibility trojan (RAT) with data-stealing and backdoor capabilities that probably spreads through SMS,” Sekoia scientists said.
It all starts off with a phishing SMS, a technique identified as smishing, enticing customers with package delivery-themed messages made up of rogue back links, that, when clicked, commence to download the malicious APK file, but only following pinpointing if a victim’s area is in just French borders.
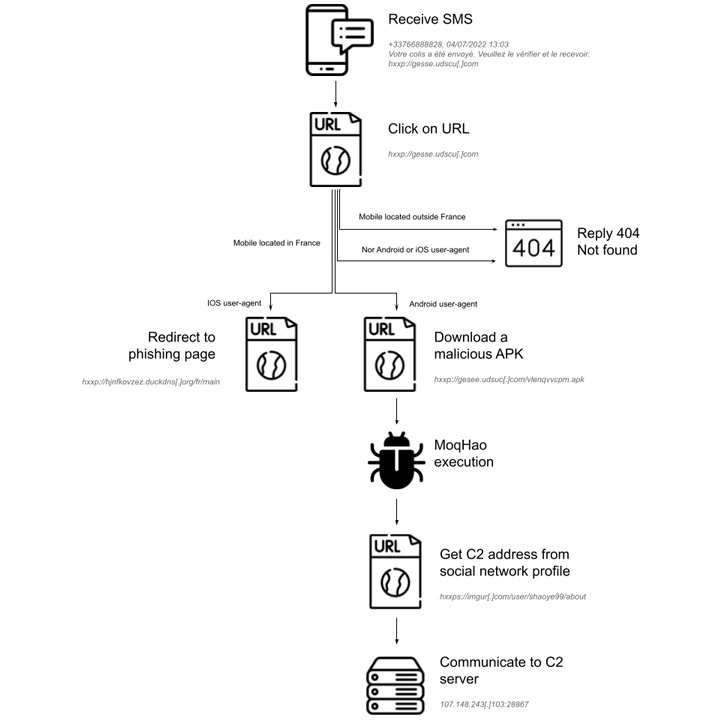
Should really a recipient be situated outdoors France and the machine running method is neither Android nor iOS – a factor ascertained by checking the IP address and the Consumer-Agent string – the server is built to respond with a “404 Not uncovered” standing code.

“The smishing marketing campaign is therefore geofenced and aims to put in Android malware, or obtain Apple iCloud credentials,” the scientists pointed out.
MoqHao commonly works by using domains created through the dynamic DNS assistance Duck DNS for its 1st-phase shipping infrastructure. What is actually a lot more, the malicious app masquerades as the Chrome web browser software to trick consumers into granting it invasive permissions.
The spy ware trojan gives a pathway window for distant conversation with the infected devices, enabling the adversary to stealthily harvest delicate information this sort of as iCloud details, get hold of lists, call history, SMS messages, between other individuals.
Sekoia also assessed that the amassed details could be utilized to aid extortion schemes or even marketed to other threat actors for financial gain. “extra than 90.000 exceptional IP addresses that requested the C2 server distributing MoqHao,” the scientists pointed out.
Identified this post intriguing? Comply with THN on Facebook, Twitter and LinkedIn to examine far more unique content we article.
Some parts of this short article are sourced from:
thehackernews.com


 SonicWall Issues Patch for Critical Bug Affecting its Analytics and GMS Products
SonicWall Issues Patch for Critical Bug Affecting its Analytics and GMS Products