Cloud environments go on to be at the receiving stop of an ongoing advanced attack campaign dubbed SCARLETEEL, with the risk actors now placing their sights on Amazon Web Services (AWS) Fargate.
“Cloud environments are nevertheless their primary goal, but the instruments and techniques employed have tailored to bypass new security actions, together with a far more resilient and stealthy command and handle architecture,” Sysdig security researcher Alessandro Brucato said in a new report shared with The Hacker News.
SCARLETEEL was 1st uncovered by the cybersecurity firm in February 2023, detailing a innovative attack chain that culminated in the theft of proprietary facts from AWS infrastructure and the deployment of cryptocurrency miners to gain off the compromised systems’ methods illegally.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
A abide by-up evaluation by Cado Security uncovered prospective hyperlinks to a prolific cryptojacking group recognized as TeamTNT, though Sysdig instructed The Hacker Information that it “could be someone copying their methodology and attack patterns.”
The most up-to-date exercise carries on the risk actor’s penchant for heading following AWS accounts by exploiting vulnerable community-dealing with web purposes with an ultimate purpose to achieve persistence, steal mental residence, and potentially deliver revenue to the tune of $4,000 per working day applying crypto miners.
“The actor found out and exploited a error in an AWS policy which allowed them to escalate privileges to AdministratorAccess and gain command above the account, enabling them to then do with it what they wanted,” Brucato spelled out.
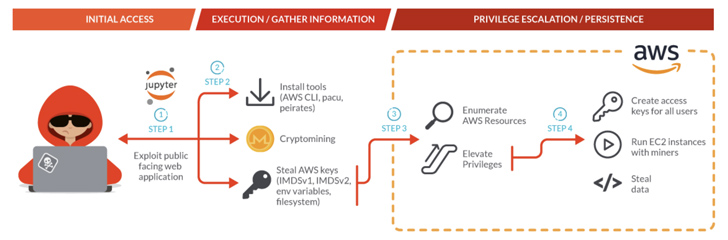
It all commences with the adversary exploiting JupyterLab notebook containers deployed in a Kubernetes cluster, leveraging the original foothold to conduct reconnaissance of the concentrate on network and acquire AWS qualifications to acquire deeper access into the victim’s environment.
This is followed by the installation of the AWS command line tool and an exploitation framework referred to as Pacu for subsequent exploitation. The attack also stands out for its use of numerous shell scripts to retrieve AWS credentials, some of which target AWS Fargate compute engine situations.
“The attacker was noticed employing the AWS customer to join to Russian techniques which are appropriate with the S3 protocol,” Brucato claimed, including the SCARLETEEL actors made use of stealthy strategies to make certain that info exfiltration occasions are not captured in CloudTrail logs.
Future WEBINAR🔐 PAM Security – Pro Remedies to Secure Your Sensitive Accounts
This pro-led webinar will equip you with the know-how and strategies you require to rework your privileged obtain security technique.
Reserve Your Location
Some of the other steps taken by the attacker consist of the use of a Kubernetes Penetration Tests tool recognised as Peirates to exploit the container orchestration technique and a DDoS botnet malware identified as Pandora, indicating further more attempts on the element of the actor to monetize the host.
“The SCARLETEEL actors continue on to operate from targets in the cloud, such as AWS and Kubernetes,” Brucato explained. “Their desired strategy of entry is exploitation of open compute expert services and vulnerable programs. There is a continued concentrate on financial attain via crypto mining, but […] mental assets is nevertheless a priority.”
Discovered this posting attention-grabbing? Adhere to us on Twitter and LinkedIn to examine much more special content material we article.
Some parts of this report are sourced from:
thehackernews.com


 Beware of Big Head Ransomware: Spreading Through Fake Windows Updates
Beware of Big Head Ransomware: Spreading Through Fake Windows Updates